Ledger — прохождение сложной машины от Tryhackme
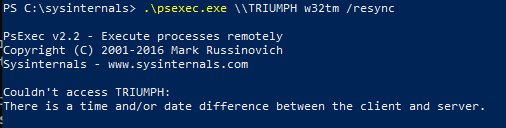
Ledger — это сложная машина Windows на TryHackMe, в центре которой находится неправильная конфигурация служб сертификатов Active Directory (AD CS). Первоначальная разведка выявляет контроллер домена ( labyrinth.thm.local ) с включенной аутентификацией SMB null и LDAP, раскрывающим учетные данные пользователя в примечаниях. Через certipy-ad находим шаблон сертификата ServerAuth , который уязвим к ESC1 , что позволяет любому аутентифицированному пользователю запросить сертификат, выдавая себя за администратора домена. Хэш NT администратора извлекается из поддельного сертификата, а psexec предоставляет командную оболочку NT AUTHORITY SYSTEM. Альтернативный путь эксплуатации через аутентификацию LDAP Schannel для случаев, когда Kerberos PKINIT не срабатывает.
https://habr.com/ru/articles/1032298/
#active_directory #certificate #esc #windows #nmap #cvss_v3 #mitre_attack #certipy #psexec #ldap









 🛩️ 🏴☠️
🛩️ 🏴☠️