Tracking TamperedChef Clusters via Certificate and Code Reuse
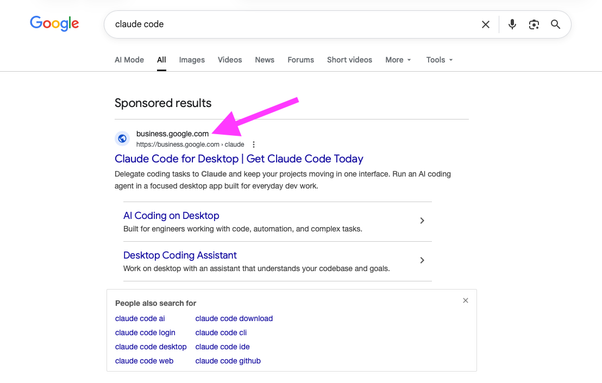
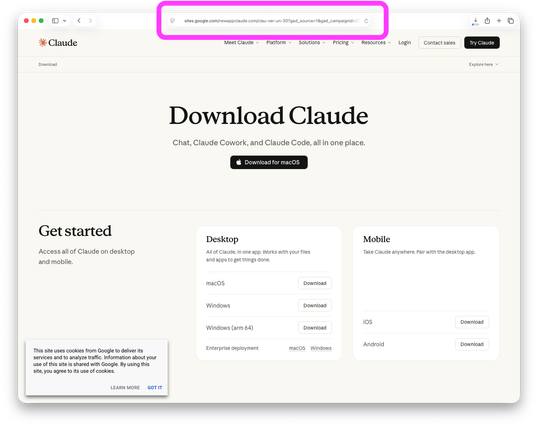
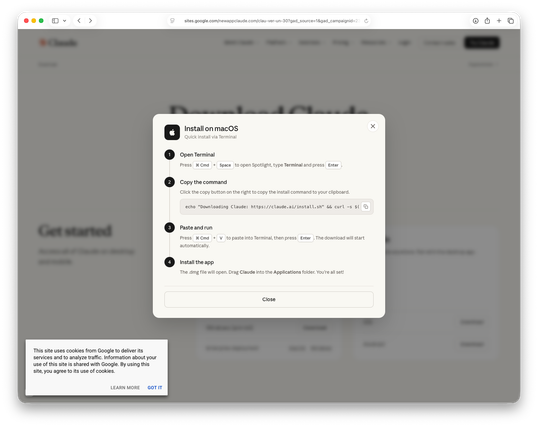
Multiple threat clusters designated as CL-CRI-1089, CL-UNK-1090, and CL-UNK-1110 have been distributing trojanized productivity software through malicious advertising campaigns since 2023. These applications, including PDF editors, calendars, and compression tools, appear legitimate but contain remote access capabilities enabling deployment of information stealers, proxy tooling, and RATs. The campaigns leverage code-signing certificates, remain dormant for weeks to months before activation, and affect organizations globally with over 4,000 samples identified across 100 variants. CL-CRI-1089 operations utilize Ukrainian, Malaysian, and British infrastructure with 34 unique code-signing entities, while CL-UNK-1090 demonstrates vertical integration between advertising agencies and malware creation using primarily Israeli infrastructure with 39 corporations involved. Distribution occurs through sophisticated malvertising employing professional websites, CDN delivery, and search engine optimization techniques.
Pulse ID: 6a0dae41682ec38e55d1aa12
Pulse Link: https://otx.alienvault.com/pulse/6a0dae41682ec38e55d1aa12
Pulse Author: AlienVault
Created: 2026-05-20 12:51:13
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#CDN #CyberSecurity #InfoSec #Israel #Malvertising #Malware #OTX #OpenThreatExchange #PDF #Proxy #RAT #Trojan #UK #Ukr #Ukrainian #bot #AlienVault