Les petites structures sont souvent les plus exposées — pas par négligence, mais parce que les ressources manquent et que les risques restent invisibles jusqu'au jour où ils ne le sont plus.
Trois angles faciles à oublier, utiles à rappeler. Parce que la sécurité, ça commence souvent par les détails qu'on reporte à demain. ☕
#infosec #cybersecurity #SMB
https://malware.news/t/3-easy-to-miss-cybersecurity-risks-for-small-businesses/106629

3 easy-to-miss cybersecurity risks for small businesses
There’s a lot to security that isn’t necessarily “cyber.” It’s not all hackers or complex network attacks. Introduction to Malware Binary Triage (IMBT) Course Looking to level up your skills? Get 10% off using coupon code: MWNEWS10 for any flavor. Enroll Now and Save 10%: Coupon Code MWNEWS10 Note: Affiliate link – your enrollment helps support this platform at no extra cost to you. Alongside traditional cyberattacks that deploy malware or exploit known software vulnerabilities, there are ...
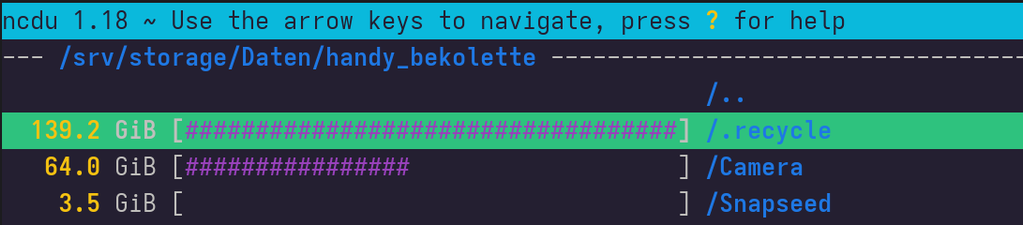
Wondered why my images folder is so huge. Turns out there's a hidden .recycle folder used by Samba/CIFS to act as network level trash bin. You know… in case someone deletes something from a network share by accident.
So all the time I was freeing up space on purpose I ended up with an additional copy on the remote fs 😩
* I use the F-Droid app SMBSync2 to backup my images from the smartphone automatically to my local network share.
Analysis of Attack Activities Using SSH+TOR Tunnels to Achieve Covert Persistence
APT-C-13 (Sandworm), also known as FROZENBARENTS, is a state-sponsored advanced persistent threat group conducting global cyber espionage operations. The organization recently deployed malicious campaigns using nested SSH and TOR tunnel infrastructure to establish covert remote access channels. Attackers distribute ZIP archives containing weaponized LNK files via spearphishing emails, which extract and execute payloads that create scheduled tasks disguised as legitimate software. The attack establishes dual-encrypted anonymous tunnels using obfs4 protocol to bypass deep packet inspection, while mapping sensitive ports (SMB/445, RDP/3389) to Onion domains for persistent backdoor access. The campaign leverages sophisticated anti-analysis techniques including sandbox detection, file disguise, and process masquerading to evade detection and maintain long-term unauthorized control over compromised systems for intelligence collection.
Pulse ID: 69f1f50a5410ca637c84368c
Pulse Link: https://otx.alienvault.com/pulse/69f1f50a5410ca637c84368c
Pulse Author: AlienVault
Created: 2026-04-29 12:09:46
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#BackDoor #CyberSecurity #Email #Espionage #InfoSec #LNK #OTX #Onion #OpenThreatExchange #Phishing #RAT #RDP #SMB #SSH #Sandworm #SpearPhishing #Worm #ZIP #bot #AlienVault
Komari Red: The Monitoring Tool with a Built-in Reverse Shell
On April 16, 2026, a threat actor leveraged stolen VPN credentials to access a Windows workstation and deployed a SYSTEM-level backdoor using the Komari agent, an open-source monitoring tool with built-in command-and-control capabilities. The attacker authenticated through an SSLVPN session from IP 45.153.34[.]132 and used Impacket smbexec.py to enable RDP on the target system. The Komari agent was installed as a persistent Windows service named 'Windows Update Service' using NSSM, pulling the installer directly from the official GitHub repository. Komari provides bidirectional control through WebSocket connections, offering arbitrary command execution, interactive reverse shell access, and network probing capabilities by default. Microsoft Defender quarantined an earlier registry dump attempt, forcing the adversary to pivot to this GitHub-based approach. This represents the first publicly documented case of Komari being abused in a real-world intrusion.
Pulse ID: 69f29e7612b827a15dfc7787
Pulse Link: https://otx.alienvault.com/pulse/69f29e7612b827a15dfc7787
Pulse Author: AlienVault
Created: 2026-04-30 00:12:38
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#BackDoor #CyberSecurity #GitHub #InfoSec #Microsoft #MicrosoftDefender #OTX #OpenThreatExchange #RCE #RDP #SMB #SSL #VPN #Windows #bot #AlienVault
ich habe die letzten Tage mein #Raspberry Projekt etwas ausgebaut.
Ein Raspi 4 mit 4GB läuft hier mit #PiHole #wachtyourlan #minidlna und #smb.
2Stück zero 2w Pi´s laufen als #spotifyclient und mit #mopidy streamen die mit USB-Soundkarte vom minidlna. Ich liebe es! 😃
Mopidy-Musicbox geht gut vom Handy über Browser zu steuern.
Einen zero w Pi hab ich noch zum basteln und testen. Die 32bit ARM_v6 wird leider nicht mehr so gut unterstützt.
Ganz ohne Spotify geht es noch nicht ganz...
Attack Activity Analysis Using SSH+TOR Tunnels for Covert Persistence
APT-C-13 (Sandworm), also known as FROZENBARENTS, is a state-sponsored advanced persistent threat group conducting global cyber espionage targeting government agencies, diplomatic departments, energy enterprises, and research organizations. Recently detected samples reveal the group's use of nested SSH and TOR tunnel architecture to establish covert communication channels. The attack begins with spear-phishing emails delivering malicious LNK files disguised as PDF documents. Upon execution, the payload deploys TOR hidden services mapping internal ports (SMB/445, RDP/3389) to onion domains, while SSH services with public key authentication provide encrypted remote access. The malware employs obfs4 protocol to obfuscate TOR traffic, evading deep packet inspection. Persistence is achieved through scheduled tasks masquerading as legitimate applications like Opera GX and Dropbox, establishing an anonymous shadow management infrastructure for sustained intelligence collection.
Pulse ID: 69f06b1eeeb1fca735cb0bb8
Pulse Link: https://otx.alienvault.com/pulse/69f06b1eeeb1fca735cb0bb8
Pulse Author: AlienVault
Created: 2026-04-28 08:09:02
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#CyberSecurity #Dropbox #Email #Espionage #Government #InfoSec #LNK #Malware #OTX #Onion #OpenThreatExchange #Opera #PDF #Phishing #RDP #SMB #SSH #Sandworm #SpearPhishing #Worm #bot #AlienVault
📰 AI-Driven Attacks Fueling MSP Supply Chain Risk, Guardz Report Finds
🤖 AI-driven attacks are hammering MSPs & SMBs. A new Guardz report finds 9/10 SMBs have compromised users, with attackers abusing RMM tools like ScreenConnect for massive supply chain attacks. #MSP #SMB #CyberSecurity #AI #RMM