And because one compromise never comes alone... Here's another...
TwizAdmin -- Multi-Stage Crypto Clipper, Infostealer & Ransomware Operation
Pulse ID: 69e9a4dd04205709b091f331
Pulse Link: https://otx.alienvault.com/pulse/69e9a4dd04205709b091f331
Pulse Author: Tr1sa111
Created: 2026-04-23 04:49:33
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#CyberSecurity #InfoSec #InfoStealer #OTX #OpenThreatExchange #RAT #RansomWare #bot #Tr1sa111
TwizAdmin -- Multi-Stage Crypto Clipper, Infostealer & Ransomware Operation
A sophisticated multi-stage malware operation was identified through an exposed C2 panel at 103.241.66[.]238:1337, combining cryptocurrency clipboard hijacking across eight chains, BIP-39 seed phrase theft, browser credential exfiltration, ransomware module (crpx0), and Java RAT builder managed via FastAPI-based panel with license key system. The operation targets Windows and macOS using FedEx and OnlyFans-themed social engineering lures, with complete source code exposed in open directories. The ransomware component communicates with three Russian .ru domains resolving to 31.31.198[.]206 at REG.RU hosting, operating under the identity DataBreachPlus with Telegram, qTox, and ProtonMail contacts. Ten cryptocurrency wallet addresses spanning Bitcoin, Ethereum, Tron, Dogecoin, Litecoin, Solana, Ripple, and Bitcoin Cash were extracted from configurations, indicating a Malware-as-a-Service operation with tiered licensing.
Pulse ID: 69e8c1fb96869b14e2c565a2
Pulse Link: https://otx.alienvault.com/pulse/69e8c1fb96869b14e2c565a2
Pulse Author: AlienVault
Created: 2026-04-22 12:41:31
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#BitCoin #Browser #Clipboard #CyberSecurity #InfoSec #InfoStealer #Java #Mac #MacOS #Malware #MalwareAsAService #OTX #OpenThreatExchange #RAT #RCE #RansomWare #Russia #SocialEngineering #Telegram #Windows #bot #cryptocurrency #AlienVault
macOS ClickFix Attacks Harvest Credentials via AppleScript Stealers
macOS users beware: a sneaky ClickFix campaign is using AppleScript stealers to harvest credentials from 14 browsers, 16 cryptocurrency wallets, and over 200 extensions. This targeted attack has already made off with a staggering amount of sensitive info - and it's still on the loose.
#Macos #Clickfix #Applescript #Infostealer #CredentialHarvesting
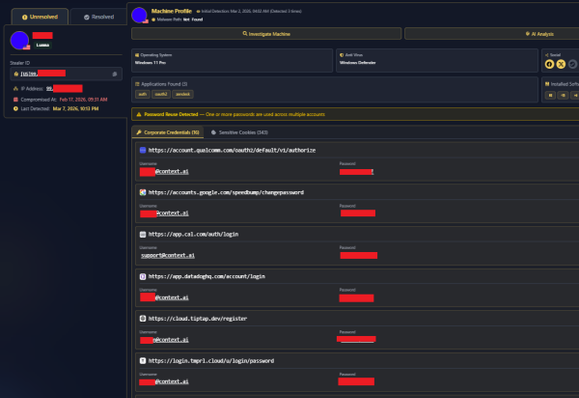
Zhackowali ich, bo pracownik SaaS z którego korzystali pobrał cheaty do gier. Czyli dlaczego trzeba uważać na OAuth!
Jaka piękna katastrofa! W tej historii jest wszystko: infekcja nie jednego, a dwóch niezbyt roztropnych pracowników różnych “technicznych” firm. Przeskok z jednej zainfekowanej infrastrukry na drugą, bo żadna z firm nie korzystała z zasady minimalnych przywilejów a można odnieść wrażenie, że w ogóle z żadnych mechanizmów bezpieczeństwa. I wreszcie grupa atakujących, która kradnie tożsamość innej grupie oraz plujący jadem internetowi przeciwnicy vibecodingu, którzy z widłami poszli na firmę, bo przecież wiadomo, że “każdy programista AI to debil”. A okazało się, że AI nie miało z tym atakiem niczego wspólnego.
Od czego się zaczęło?
19 kwietnia na znanym hackerskim forum pojawiła się informacja o tym, że popularna wśród vibecoderów platforma Vercel została zhackowana. Atakujący podpisujący się jako ShinyHunters wystawili na sprzedaż klucze i dostępy do bazy danych firmy. Zrobiło się gorąco w środowisku, bo Vercel stoi też za narzędziem v0 oraz popularną biblioteką Next.js, a to od razu przywołało ostatnie głośne ataki supply chain.
Na początku oczywiście spekulowano, że przełamanie zabezpieczeń to wynik użycia beztroskiego vibecodingu do budowy i konfiguracji mechanizmów bezpieczeństwa Vercela. Bo firma z vibecodingiem jest kojarzona. Ale prawda okazała jeszcze bardziej bolesna. Źródłem ataku był łańcuch dwóch pracowników.
Pierwszy to pracownik zewnętrznej firmy — Contex.ai, który pobierał …cheaty do gry Roblox zainfekowane infostealerem Lumma. Dzięki temu atakujący mieli dostęp do infrastruktury firmy Contex.ai oraz danych jej klientów. Dwa miesiące [...]
#AI #EskalacjaPrzywilejów #GoogleWorkspace #Infostealer #Malware #SaaS #Stealer #Vercel
macOS ClickFix Campaign: AppleScript Stealers & New Terminal Protections
A sophisticated ClickFix campaign targets both Windows and macOS users through fake CAPTCHA pages that trick victims into executing malicious commands. The macOS variant deploys an AppleScript-based infostealer that harvests sensitive data including keychain databases, credentials, and session cookies from 12 browsers, over 200 browser extensions, and 16 cryptocurrency wallets. The malware employs a persistent, non-closable dialog box mimicking legitimate system prompts to force victims into providing their system password. Stolen session cookies enable attackers to bypass multi-factor authentication by hijacking active sessions. The campaign uses client-side JavaScript to filter victims by user-agent, directing desktop users to OS-specific payloads while ignoring mobile devices. Latest macOS updates include native terminal security warnings designed to alert users against pasting potentially malicious commands.
Pulse ID: 69e6db546f646b9818b7bf0d
Pulse Link: https://otx.alienvault.com/pulse/69e6db546f646b9818b7bf0d
Pulse Author: AlienVault
Created: 2026-04-21 02:05:08
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#Browser #CAPTCHA #Cookies #CyberSecurity #InfoSec #InfoStealer #Java #JavaScript #Mac #MacOS #Malware #Mimic #OTX #OpenThreatExchange #Password #RCE #Windows #Word #bot #cryptocurrency #AlienVault
From fake Proton VPN sites to gaming mods, this Windows infostealer is everywhere
Pulse ID: 69e6fb953f412155415f7e5d
Pulse Link: https://otx.alienvault.com/pulse/69e6fb953f412155415f7e5d
Pulse Author: Tr1sa111
Created: 2026-04-21 04:22:45
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#CyberSecurity #InfoSec #InfoStealer #OTX #OpenThreatExchange #VPN #Windows #bot #Tr1sa111
Dal Roblox script al breach di Vercel: come un infostealer ha quasi compromesso la supply chain di Next.js
Un dipendente di Context.ai infettato da Lumma Stealer tramite script Roblox ha aperto la porta a una potenziale supply chain attack su Vercel e Next.js. ShinyHunters rivendica il furto di codice sorgente, token NPM/GitHub e 580 record di dipendenti, offrendo il pacchetto per $2 milioni. Vercel conferma accesso limitato ma esclude compromissione dei framework open source.From fake Proton VPN sites to gaming mods, this Windows infostealer is everywhere
Multiple campaigns are distributing NWHStealer through diverse delivery methods including fake VPN downloads, hardware utilities, and gaming modifications. The malware collects browser data, saved passwords, and cryptocurrency wallet information. Distribution occurs via fake websites impersonating legitimate services like Proton VPN, code hosting platforms such as GitHub and GitLab, file hosting services including MediaFire and SourceForge, and links from YouTube videos. Two primary infection methods were identified: one using a free web hosting provider distributing malicious ZIP files with self-injection, and another using fake websites with DLL hijacking that injects code into RegAsm processes. The stealer targets over 25 cryptocurrency wallets and multiple browsers, using AES-CBC encryption for command-and-control communications and employing UAC bypass techniques for privilege escalation.
Pulse ID: 69e27c47d37f66809a367479
Pulse Link: https://otx.alienvault.com/pulse/69e27c47d37f66809a367479
Pulse Author: AlienVault
Created: 2026-04-17 18:30:31
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#Browser #CyberSecurity #ELF #Encryption #GitHub #InfoSec #InfoStealer #Malware #OTX #OpenThreatExchange #Password #Passwords #RCE #VPN #Windows #Word #YouTube #ZIP #bot #cryptocurrency #AlienVault