Another talk for BSides Luxembourg!
💥🔥 𝗧𝗛𝗘 𝗪𝗛𝗜𝗦𝗧𝗟𝗘𝗦 𝗚𝗢 𝗪𝗢𝗢 𝗪𝗢𝗢: 𝗦𝗜𝗘𝗠 𝗔𝗟𝗘𝗥𝗧𝗦, 𝗧𝗛𝗥𝗘𝗔𝗧 𝗗𝗘𝗧𝗘𝗖𝗧𝗜𝗢𝗡 𝗔𝗡𝗗 𝗧𝗨𝗡𝗜𝗡𝗚 𝗨𝗡𝗡𝗘𝗖𝗘𝗦𝗦𝗔𝗥𝗬 𝗡𝗢𝗜𝗦𝗘 - 𝗠𝗘𝗟𝗜𝗡𝗔 𝗣𝗛𝗜𝗟𝗟𝗜𝗣𝗦 ( @tx_princess ) 🕵️♀️⚔️
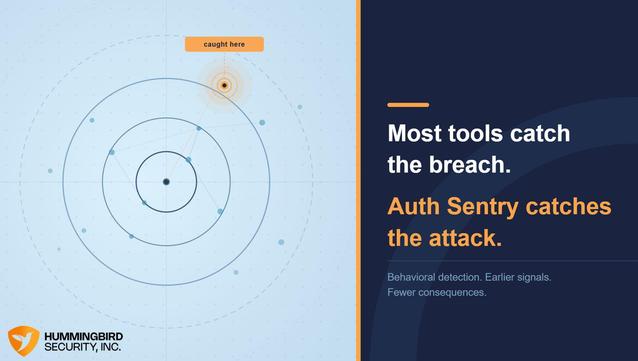
Security teams don’t miss alerts because they’re careless, they miss them because their SIEM never stops yelling. This talk shows how poorly timed, constant, or context-free alerts become meaningless noise and how simple fixes like throttling, prioritization, and timing can turn a SIEM into a tool that actually gets noticed when it matters.
Melina Phillips https://www.linkedin.com/in/melinaphillips-cissp/ is an Offensive Security Engineer with over 10 years in IT and 6 years in cybersecurity, specializing in security operations, incident detection, adversary simulation, and endpoint compromise. She has presented at BSides Cambridge, Security Fest, BruCon, LeHack, HackLu, and BlackAlps.
📅 Conference dates: 6–8 May 2026 | 09:00–18:00
📍 14, Porte de France, Esch-sur-Alzette, Luxembourg
🎟️ Tickets: https://2026.bsides.lu/tickets/
📅 Schedule Link: https://pretalx.com/bsidesluxembourg-2026/schedule/
#BSidesLuxembourg2026 #CyberSecurity #OffensiveSecurity #ThreatDetection #LinuxSecurity #Infosec