Casting a Wider Net: Scaling Threat
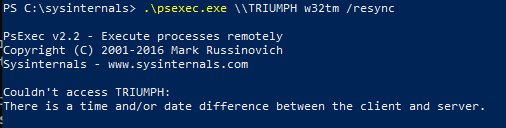
LeakNet, a ransomware operator, has expanded its initial access methods by utilizing ClickFix lures on compromised websites and implementing a new Deno-based, in-memory loader. The group has shifted from relying on initial access brokers to running its own campaigns. LeakNet's post-exploitation playbook remains consistent, involving jli.dll side-loading, PsExec-based lateral movement, and S3 bucket payload staging. The Deno loader executes base64-encoded payloads in memory, making detection challenging for traditional security tools. Defenders are advised to focus on behavioral signals and implement measures such as blocking newly registered domains, restricting Win-R access, and limiting PsExec usage to authorized administrators.
Pulse ID: 69ba8419321e1d3c9be7c4cc
Pulse Link: https://otx.alienvault.com/pulse/69ba8419321e1d3c9be7c4cc
Pulse Author: AlienVault
Created: 2026-03-18 10:53:13
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#CyberSecurity #InfoSec #OTX #OpenThreatExchange #PsExec #RAT #RansomWare #bot #AlienVault