From Inbox to Intrusion: Multi‑Stage Remcos RAT and C2‑Delivered Payloads in Network
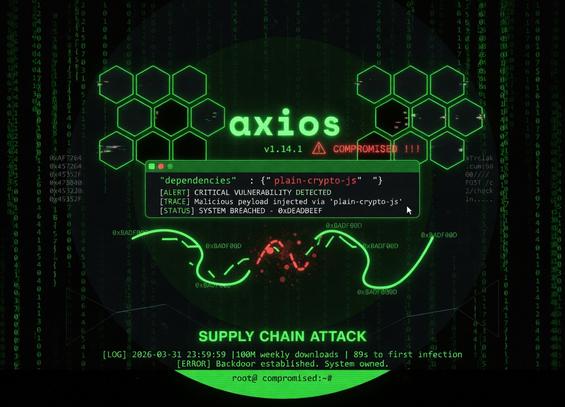
This multi-stage fileless Remcos RAT attack leverages a phishing-delivered JavaScript dropper to trigger a reflective PowerShell loader that executes payloads entirely in memory. The infection chain utilizes obfuscation techniques like rotational XOR and Base64 encoding to reconstruct .NET payloads, significantly reducing the disk-based detection footprint. Stealth is maintained by using aspnet_compiler.exe as a LOLBin to proxy malicious execution and dynamically retrieving the final payload from a remote C2 server.
Pulse ID: 69cd1ac8518646002a1a0fbc
Pulse Link: https://otx.alienvault.com/pulse/69cd1ac8518646002a1a0fbc
Pulse Author: AlienVault
Created: 2026-04-01 13:16:56
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#ASPNet #ASPNet_Compiler #CyberSecurity #InfoSec #Java #JavaScript #NET #OTX #OpenThreatExchange #Phishing #PowerShell #Proxy #RAT #Remcos #RemcosRAT #bot #AlienVault