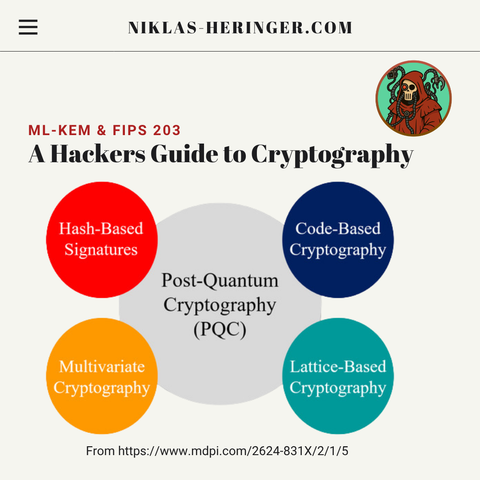
Wrote a deep-dive on ML-KEM (FIPS 203): the post-quantum key exchange already shipping in Chrome, AWS, Cloudflare and the Linux kernel.
Fully interactive rundown, covers everything from polynomial rings and Module-LWE to encapsulation, decapsulation, and why the Fujisaki-Okamoto transform turns a toy into a real primitive.
No hand-waving. Actual math, actual intuition.
🔗 https://niklas-heringer.com/research/a-hackers-guide-to-post-quantum-cryptography-ml-kem-fips-203/