Zcash Foundation Issues Emergency Zebra 4.5.0 Update to Fix Critical Consensus Flaw
The Zcash Foundation released Zebra 4.5.0 to address 13 vulnerabilities, including a critical consensus flaw (GHSA-gf9r-m956-97qx) that could cause a chain split and high-severity issues leading to permanent node halts.
**If you're running a Zebra Zcash node, upgrade to version 4.5.0 ASAP to patch 13 vulnerabilities, including a critical flaw that could split you off from the rest of the network. Until you upgrade, your node is at risk of crashing, getting stuck, or disagreeing with other nodes about the state of the blockchain.**
#cybersecurity #infosec #advisory #vulnerability
https://beyondmachines.net/event_details/zcash-foundation-issues-emergency-zebra-4-5-0-update-to-fix-critical-consensus-flaw-s-h-g-l-8/gD2P6Ple2L

Zcash Foundation Issues Emergency Zebra 4.5.0 Update to Fix Critical Consensus Flaw
The Zcash Foundation released Zebra 4.5.0 to address 13 vulnerabilities, including a critical consensus flaw (GHSA-gf9r-m956-97qx) that could cause a chain split and high-severity issues leading to permanent node halts.
on: ⚠️hxxp[:]//divinedownload[.]com/eov[.]php?id=0f304eddb4ad6007a3093fd6d963a1d2
🧬 Analysis at: https://urldna.io/scan/6a1bba173b775000066b319a
#cybersecurity #phishing #infosec #urldna #scam #infosec
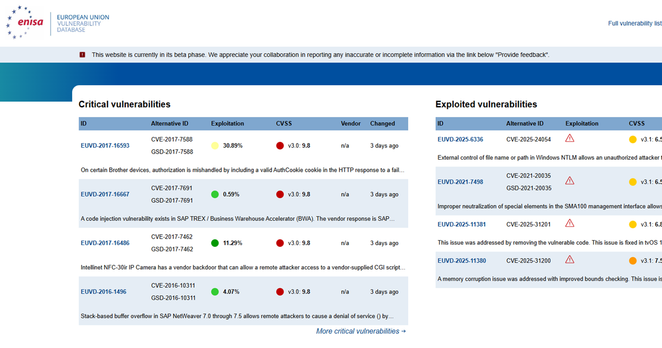
🚨 EUVD-2026-33490
📊 Score: 5.3/10 (CVSS v3.1)
📦 Product: Visitor Management System
🏢 Vendor: code-projects
📅 Updated: 2026-05-31
📝 A flaw has been found in code-projects Visitor Management System 1.0. Affected by this issue is some unknown functionality of the file /vms/php/phone_0.php. This manipulation of the argument phone causes sql injection. The attack may ...
🔗 https://euvd.enisa.europa.eu/vulnerability/EUVD-2026-33490
🚨 EUVD-2026-33491
📊 Score: 5.1/10 (CVSS v3.1)
📦 Product: Online Music Site
🏢 Vendor: code-projects
📅 Updated: 2026-05-31
📝 A vulnerability has been found in code-projects Online Music Site 1.0. This affects an unknown part of the file /Administrator/PHP/AdminUpdateAlbum.php. Such manipulation of the argument ID leads to sql injection. The attack may be launched r...
🔗 https://euvd.enisa.europa.eu/vulnerability/EUVD-2026-33491
ASN: AS9121
Location: Ankara, TR
Added: 2026-05-25T16:22
on: ⚠️hxxps[:]//vjf-cnrs-admin[.]weebly[.]com
🧬 Analysis at: https://urldna.io/scan/6a1b96413b775000066b2eb3
#cybersecurity #phishing #infosec #urldna #scam #infosec
🚨 CVE du jour : CVE-2026-10169
Le reset de mot de passe de ce SMS scolaire ? Un endpoint qui oublie de vérifier l'email. 🎓🔓
📊 Indice de Panique™ : 0.6/10
█░░░░░░░░░
🔴 CVSS 0.0 — meh
🔥 EPSS 0% — théorique LinkedIn
🧘 Niveau Chill — "Tu peux ignorer ça… comme tes backups"
🔗 https://vulnerability.circl.lu/vuln/CVE-2026-10169
#CVE #infosec #vulnerability
on: ⚠️hxxps[:]//yghhjsrr[.]weebly[.]com
🧬 Analysis at: https://urldna.io/scan/6a1b81d33b775000066b2d02
#cybersecurity #phishing #infosec #urldna #scam #infosec
ASN: AS63014
Location: Chicago, US
Added: 2026-05-27T22:45