ClickFix Evolves with PySoxy Proxying
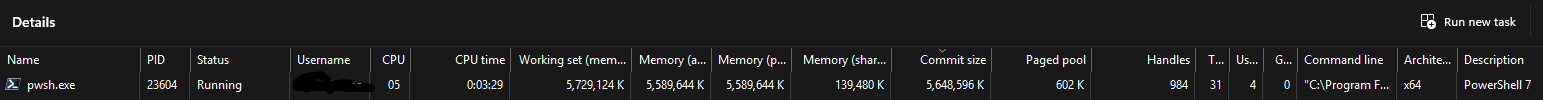
A sophisticated ClickFix campaign was observed in April 2026 deploying PySoxy, a decade-old open-source Python SOCKS5 proxy tool, to establish encrypted proxy access on compromised hosts. The attack chain begins with social engineering that tricks users into executing obfuscated PowerShell commands, which then establishes scheduled task persistence and deploys an in-memory PowerShell-based command-and-control agent. Following domain reconnaissance activities, attackers deploy PySoxy to create a redundant encrypted access channel. The persistence mechanism continues attempting re-execution even after initial connections are blocked, demonstrating how single ClickFix executions can evolve into modular post-exploitation chains. This development represents a significant evolution from simple one-time execution to durable access with multiple redundant pathways, requiring comprehensive remediation beyond blocking initial callbacks.
Pulse ID: 6a04a9a171b2ad5ef57d9993
Pulse Link: https://otx.alienvault.com/pulse/6a04a9a171b2ad5ef57d9993
Pulse Author: AlienVault
Created: 2026-05-13 16:41:05
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#CyberSecurity #InfoSec #OTX #OpenThreatExchange #PowerShell #Proxy #Python #RAT #RCE #SocialEngineering #bot #socks5 #AlienVault