Sometimes, it's difficult to #decide, when presented with two #options, after reaching a #crossroad. A #door rarely reveals what is behind it. Our #choices are #obfuscated, and we have to blindly choose. That's #life. It would be nice, but mostly, we don't get to pick and chose. Choices are #fake. They just appear as if we had a say. #randomness is the #nameOfTheGame.
If they know you have an #encrypted file, they can begin work cracking it.
If you have an #obfuscated file, they may never even know it's there.
#obfuscatedCommunication #encryption #encryptedCommunication #opsec
another one from #TheCrux
"Would you like to annoy your security team even more than usual? Why not create #obfuscated links to regular websites that look like phishing attempts with Phishy URL?"
this is hilarious @daedalus thanks from my DEVs 😆🐡 #phish #urls
Here is a cool, novel advanced #algorithm for tracking #stealth and can be used for #asteroid tracking, #spacejunk etc
Also. These mosaiced screen video, you can read the #obfuscated text.
#opsec #infosec implications
"pixel voxel motion projection"
Precisely tracking Stealth fighters using cheap cameras without AI.
🚨 #Obfuscated BAT file used to deliver NetSupport RAT
At the time of the analysis, the sample had not yet been submitted to #VirusTotal ⚠️
👨💻 See sandbox session: https://app.any.run/tasks/db6fcb53-6f10-464e-9883-72fd7f1db294?utm_source=mastodon&utm_medium=post&utm_campaign=obfuscated_bat_file&utm_content=linktoservice&utm_term=050625
🔗 Execution chain:
cmd.exe (BAT) ➡️ #PowerShell ➡️ PowerShell ➡️ #client32.exe (NetSupport client) ➡️ reg.exe
Key details:
🔹 Uses a 'client32' process to run #NetSupport #RAT and add it to autorun in registry via reg.exe
🔹 Creates an 'Options' folder in %APPDATA % if missing
🔹 NetSupport client downloads a task .zip file, extracts, and runs it from %APPDATA%\Application .zip
🔹 Deletes ZIP files after execution
❗️ BAT droppers remain a common choice in attacks as threat actors continue to find new methods to evade detection.
Use #ANYRUN’s Interactive Sandbox to quickly trace the full execution chain and uncover #malware behavior for fast and informed response.
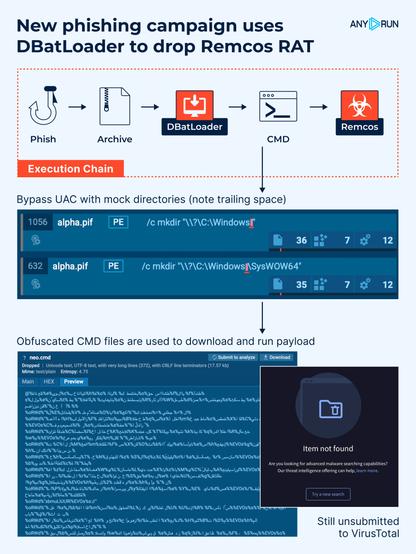
🚨 New #phishing campaign uses #DBatLoader to drop #Remcos RAT.
The infection relies on #UAC bypass with mock directories, obfuscated .cmd scripts, Windows #LOLBAS techniques, and advanced persistence techniques. At the time of analysis, the samples had not yet been submitted to #VirusTotal ⚠️
🔗 Execution chain:
#Phish ➡️ Archive ➡️ DBatLoader ➡️ CMD ➡️ SndVol.exe (Remcos injected)
👨💻 #ANYRUN allows analysts to quickly uncover stealth techniques like LOLBAS abuse, injection, and UAC bypass, all within a single interactive analysis session. See analysis: https://app.any.run/tasks/c57ca499-51f5-4c50-a91f-70bc5a60b98d/?utm_source=mastodon&utm_medium=post&utm_campaign=dbatloader&utm_term=150525&utm_content=linktoservice
🛠️ Key techniques:
🔹 #Obfuscated with #BatCloak .cmd files are used to download and run #payload.
🔹 Remcos injects into trusted system processes (SndVol.exe, colorcpl.exe).
🔹 Scheduled tasks trigger a Cmwdnsyn.url file, which launches a .pif dropper to maintain persistence.
🔹 Esentutl.exe is abused via LOLBAS to copy cmd.exe into the alpha.pif file.
🔹 UAC bypass is achieved with fake directories like “C:\Windows “ (note the trailing space), exploiting how Windows handles folder names.
⚠️ This threat uses multiple layers of stealth and abuse of built-in Windows tools. Behavioral detection and attention to unusual file paths or another activity are crucial to catching it early. #ANYRUN Sandbox provides the visibility needed to spot these techniques in real time 🚀
I had an idea for a new sequence simulator. Generate two random sequences and then define a rate for a third sequences which is a blend of the two. Code is below, though slightly obfuscated.
Anyone good in analyzing obfuscated javascript and can tell me what happens here?
https://pastebin.com/Taj4esdY
Some kind of #obfuscated #JavaScript #exploit targetting G2A users (lol)
PDF linked on PasteBin directs users to install a #Tampermonkey script.
hxxps://textbin.net/raw/awsj07eiit
#Labour’s #KeirStarmer backs #trans #sports #bans ‘Common sense has to prevail’
#Labour once #stoodfirm on #transgender #rights but amid the increasing #politicisation of #trans #lives the #party has #backtracked, #Uturned and #obfuscated on #key #issues.
- There is absolutely no difference between the #Tories or #Labour
#Women #Transgender #LGBTQ #LGBTQIA #UK #Labour #Hate #Bigotry #Violence #Genocide #Discrimination #Transphobia #TERFIsland
https://www.thepinknews.com/2024/03/12/keir-starmer-trans-athletes-ban/