🚨 𝗪𝗵𝘆 𝗣𝗵𝗶𝘀𝗵𝗶𝗻𝗴 𝗦𝘁𝗶𝗹𝗹 𝗚𝗲𝘁𝘀 𝗧𝗵𝗿𝗼𝘂𝗴𝗵: 𝗗𝗲𝘁𝗲𝗰𝘁𝗶𝗼𝗻 𝗚𝗮𝗽𝘀 𝗶𝗻 𝗥𝗲𝗱𝗶𝗿𝗲𝗰𝘁 & 𝗖𝗔𝗣𝗧𝗖𝗛𝗔 𝗙𝗹𝗼𝘄𝘀
Redirect chains, fake CAPTCHA, and fast-changing delivery paths make traditional detection unreliable. By the time credentials are targeted, the signal is already lost, which creates a critical gap in triage. The key is detecting #phishing earlier, while patterns are still stable, before the flow fully unfolds.
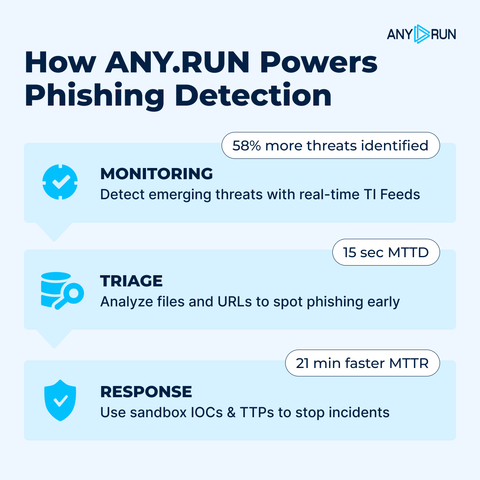
⚡️ With #ANYRUN TI Lookup, teams can move from isolated indicators to full context, identify attack patterns, and validate detection logic against real attack data from 15K+ organizations.
📌 Here are two examples showing how early-stage signals help identify phishing activity before it escalates:
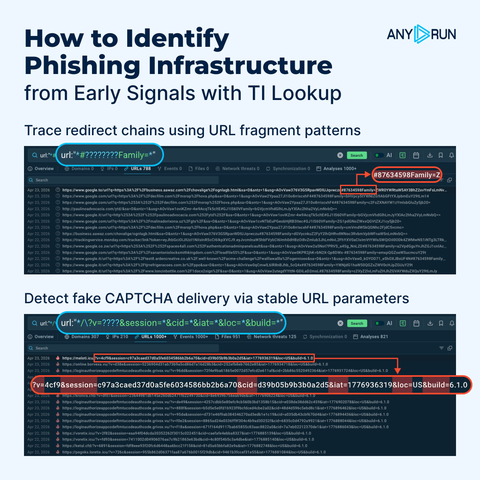
1️⃣ 𝗥𝗲𝗱𝗶𝗿𝗲𝗰𝘁 𝗶𝗻𝗳𝗿𝗮𝘀𝘁𝗿𝘂𝗰𝘁𝘂𝗿𝗲
The chain starts from a Google link leading to a compromised site. A hidden HTML page extracts victim data from the URL fragment and triggers a redirect before any user interaction. Analysis session: https://app.any.run/tasks/05c1017e-397c-4cb9-a666-e715402a943a/?utm_source=mastodon&utm_medium=post&utm_campaign=redirect_and_captcha_phishing&utm_content=linktoservice&utm_term=230426
🔍 In TI Lookup, this activity can be traced by searching for URL fragments containing the #...Family= parameter, which is used to pass victim data and drive redirection. This helps uncover similar samples and track reuse across campaigns.
⚡️ Use this query to pivot from this signal and uncover related activity: https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=redirect_and_captcha_phishing&utm_content=linktotilookup&utm_term=230426#%7B%22query%22%3A%22url%3A%5C%22*%23%3F%3F%3F%3F%3F%3F%3F%3FFamily%3D*%5C%22%22%2C%22dateRange%22%3A180%7D
2️⃣ 𝗙𝗮𝗸𝗲 𝗖𝗔𝗣𝗧𝗖𝗛𝗔 𝗱𝗲𝗹𝗶𝘃𝗲𝗿𝘆
After the initial redirect, the victim is presented with a legit-looking CAPTCHA to build trust before being redirected to a phishing page, a fake Microsoft login page powered by #EvilProxy. Analysis session: https://app.any.run/tasks/3ef22bb3-b331-4211-9526-b95c7b19d4ab/?utm_source=mastodon&utm_medium=post&utm_campaign=redirect_and_captcha_phishing&utm_content=linktoservice&utm_term=230426
🔍 Detection here relies on consistent URL parameters (v, session, cid, iat, loc, build) that appear early in the execution chain. Searching for this structure helps surface related signals and build early-stage detection, reducing MTTD, improving coverage and MTTR.
⚡️ Use this query to surface related phishing activity and validate detection patterns: https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=redirect_and_captcha_phishing&utm_content=linktotilookup&utm_term=230426#%7B%22query%22%3A%22url%3A%5C%22*%2F%5C%5C%3Fv%3D%3F%3F%3F%3F%26session%3D*%26cid%3D*%26iat%3D*%26loc%3D*%26build%3D*%5C%22%22%2C%22dateRange%22%3A60%7D
🚀 𝗬𝗼𝘂 𝗰𝗮𝗻 𝗻𝗼𝘄 𝘁𝗲𝘀𝘁 𝗧𝗜’𝘀 𝗶𝗺𝗽𝗮𝗰𝘁 𝗼𝗻 𝘁𝗿𝗶𝗮𝗴𝗲, 𝗿𝗲𝘀𝗽𝗼𝗻𝘀𝗲, 𝗮𝗻𝗱 𝘁𝗵𝗿𝗲𝗮𝘁 𝗵𝘂𝗻𝘁𝗶𝗻𝗴 𝗱𝗶𝗿𝗲𝗰𝘁𝗹𝘆 𝗶𝗻 𝘆𝗼𝘂𝗿 𝘄𝗼𝗿𝗸𝗳𝗹𝗼𝘄𝘀. With 20 premium search requests available, SOC and MSSP teams can validate activity against real-world data, reduce uncertainty, and make faster, evidence-based decisions.
⚡️ Learn how to integrate #ANYRUN Threat Intelligence into your SOC to strengthen detection and improve overall performance: https://any.run/cybersecurity-blog/expanded-free-ti-plan/?utm_source=mastodon&utm_medium=post&utm_campaign=redirect_and_captcha_phishing&utm_content=linktoblog&utm_term=230426