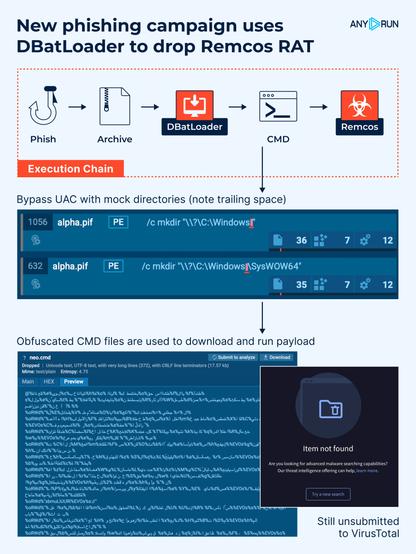
🚨 New #phishing campaign uses #DBatLoader to drop #Remcos RAT.
The infection relies on #UAC bypass with mock directories, obfuscated .cmd scripts, Windows #LOLBAS techniques, and advanced persistence techniques. At the time of analysis, the samples had not yet been submitted to #VirusTotal ⚠️
🔗 Execution chain:
#Phish ➡️ Archive ➡️ DBatLoader ➡️ CMD ➡️ SndVol.exe (Remcos injected)
👨💻 #ANYRUN allows analysts to quickly uncover stealth techniques like LOLBAS abuse, injection, and UAC bypass, all within a single interactive analysis session. See analysis: https://app.any.run/tasks/c57ca499-51f5-4c50-a91f-70bc5a60b98d/?utm_source=mastodon&utm_medium=post&utm_campaign=dbatloader&utm_term=150525&utm_content=linktoservice
🛠️ Key techniques:
🔹 #Obfuscated with #BatCloak .cmd files are used to download and run #payload.
🔹 Remcos injects into trusted system processes (SndVol.exe, colorcpl.exe).
🔹 Scheduled tasks trigger a Cmwdnsyn.url file, which launches a .pif dropper to maintain persistence.
🔹 Esentutl.exe is abused via LOLBAS to copy cmd.exe into the alpha.pif file.
🔹 UAC bypass is achieved with fake directories like “C:\Windows “ (note the trailing space), exploiting how Windows handles folder names.
⚠️ This threat uses multiple layers of stealth and abuse of built-in Windows tools. Behavioral detection and attention to unusual file paths or another activity are crucial to catching it early. #ANYRUN Sandbox provides the visibility needed to spot these techniques in real time 🚀