Honeypot reveals botnet exploiting scriptText to launch DDoS attacks on game servers
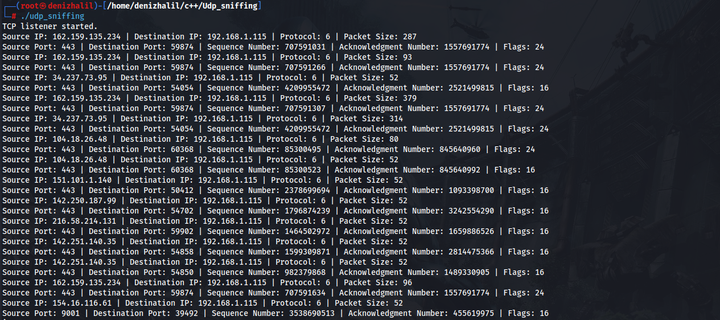
Analysts observed attackers exploiting a Jenkins honeypot to deploy a new DDoS botnet targeting video game servers. Leveraging Jenkins scriptText abuse, the threat actors achieved remote code execution by sending malicious Groovy scripts to intentionally misconfigured instances with weak passwords. The multi-platform payload targets both Windows and Linux systems, deploying malware that evades detection through process renaming and daemonization. The botnet supports multiple attack vectors including UDP floods, TCP attacks, HTTP requests, and game-specific techniques targeting Valve Source Engine servers. Infrastructure hosted in Vietnam serves dual purposes for payload distribution and command-and-control communications. The campaign demonstrates continued opportunistic exploitation of internet-facing services, with gaming industry servers being primary targets for distributed denial-of-service attacks.
Pulse ID: 6a0199674dd4cf450633dd32
Pulse Link: https://otx.alienvault.com/pulse/6a0199674dd4cf450633dd32
Pulse Author: AlienVault
Created: 2026-05-11 08:55:03
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#CyberSecurity #DDoS #DoS #HTTP #HoneyPot #InfoSec #Linux #Malware #OTX #OpenThreatExchange #Password #Passwords #RAT #RCE #RemoteCodeExecution #TCP #UDP #Vietnam #Windows #Word #bot #botnet #AlienVault