Malcolm v26.05.0 delivers a mix of feature improvements, performance improvements, bug fixes, dependency updates, and deployment refinements across Malcolm and Hedgehog for both Docker- and Kubernetes-based workflows.
If you are upgrading from an existing Malcolm installation, run ./scripts/status for Malcolm to migrate some settings prior to running ./scripts/configure, ./scripts/start, or other Malcolm control scripts.
https://github.com/idaholab/Malcolm/compare/v26.04.1...v26.05.0
- ✨ Features and enhancements
- #726 — use hierarchical structure for NetBox device roles
- Expanded/reworked NetBox preloaded device roles into a hierarchical taxonomy (thanks Crubumble)
- #867 — examine large chown'ed directories in container images and see if they can be reduced
- #954 — allow users to provide custom netbox scripts to be automatically registered on startup (thanks PrudhviChanda)
- Added NetBox custom script support in the container/runtime and docs, including bind-mounting
./netbox/custom-scriptsand automatic script registration at startup - Renamed NetBox startup/control scripts from
netbox/scriptstonetbox/control-scripts
- Added NetBox custom script support in the container/runtime and docs, including bind-mounting
- Added
file.stringsextraction/indexing/search support across Strelka → Logstash → OpenSearch templates (wildcard field mapping type) → Arkime/WISE - Added configurable Zeek file analyzer timeout via
ZEEK_FILE_ANALYZER_TIMEOUT_SEC netdevusers in ISO-installed environment can runnmcliandnmtuito configure network interfaces.- the
malcolm_appliance_packager.shscript that creates a tarball of Malcolm images can now package for both Malcolm and Hedgehog profiles.
- #726 — use hierarchical structure for NetBox device roles
- ✅ Component version updates
- 🐛 Bug fixes
- #757 — multiple OpenSearch nodes (using Malcolm-Helm) fail to communicate with each other due to self-signed certs (thanks scott-jeffery)
- OpenSearch post-start setup now supports configurable default replica counts instead of always forcing single-node replicas to
0 - OpenSearch self-signed internal cert generation can now be skipped when external/preexisting certs are being used
- OpenSearch post-start setup now supports configurable default replica counts instead of always forcing single-node replicas to
- #827 — Fix raspberry pi build which is broken since v25.12.0 Hedgehog/Malcolm platform unification
- Updated Hedgehog Raspberry Pi docs and first-boot behavior/documentation
- Hedgehog Raspberry Pi image now forces password change for
sensoron first login and disables direct root password login by default - Refactored Raspberry Pi GitHub Actions build into reusable workflow
.github/workflows/raspi-build-push.yml
- #878 — Arkime capture Fails to Start on Hedgehog When WISE Web Config Is Enabled
- Arkime RBAC role-mapping injection is now only applied when role-based access control is enabled
- Arkime WISE configuration initialization now handles missing/empty persistent config files more robustly
- Arkime live capture now normalizes WISE URLs better, follows redirects when probing, and avoids some bad URL construction edge cases
- #957 — configuration script can disable ICS parsers unintentionally
- #959 — Arkime sessions view attempts to load PCAP for Zeek and Suricata logs (which don't have PCAP) (see also arkime/arkime#3934)
- Fixed one-off cleanup of interrupted Zeek intel files during
stop --wipe
- #757 — multiple OpenSearch nodes (using Malcolm-Helm) fail to communicate with each other due to self-signed certs (thanks scott-jeffery)
- 🧹 Code and project maintenance
- Documentation improvements
- #913 — replace ingress-nginx which is EOL
- Switched Kubernetes ingress example/docs from ingress-nginx to Traefik and replaced the old Vagrant example with a new RKE2/Traefik-based environment
- Fixed malformed indentation in
kubernetes/01-volumes-nfs.yml.examplefor thefilescanvolume section - Removed deprecated Kubernetes example files for ingress-nginx and the old separate NFS-server Vagrant setup
opensearchis no longer part of thehedgehogDocker Compose profile, and somedepends_onrelationships were adjusted accordingly
- #942 - Fixed mutable default argument usage in Zeek threat feed helper functions (thanks @stef41)
- #917 — develop IronBank (US DoD) images for Malcolm
- 📄 Configuration changes for Malcolm (in environment variables in
./config/). The Malcolm control script (e.g.,./scripts/status,./scripts/start) automatically handles creation and migration of variables according to./config/env-var-actions.yml.- Added
ZEEK_FILE_ANALYZER_TIMEOUT_SEC(default5) tozeek.env. This is the default amount of time a file can be inactive before the file analysis gives up and discards any internal state related to the file. ZEEK_CLUSTER_BACKENDcan be specified inzeek.envto specify the Zeek cluster backend (ZeroMQvsBroker).
- Added
- ❌ Errata
- Under NetBox → Plugins → NetBox HealthCheck Plugin → HealthCheck the error "unavailable: Unable to connect to Redis: Connection Error" is displayed. This is a side effect of #882 and does not actually indicate a problem with NetBox or its connection to Valkey. This will be fixed in the next release.
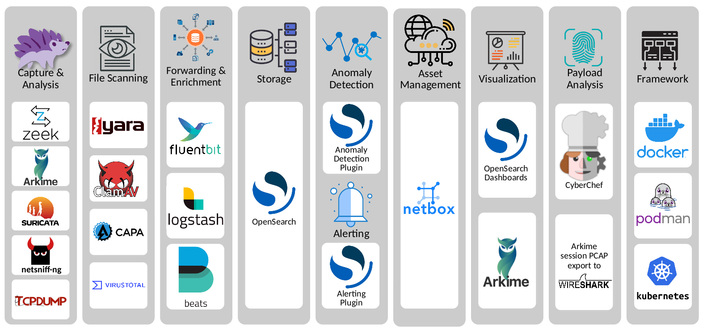
Malcolm is a powerful, easily deployable network 🖧 traffic analysis tool suite for network security monitoring 🕵🏻♀️.
Malcolm operates as a cluster of containers 📦, isolated sandboxes which each serve a dedicated function of the system. This makes Malcolm deployable with frameworks like Docker 🐋, Podman 🦭, and Kubernetes ⎈. Check out the Quick Start guide for examples on how to get up and running.
Alternatively, dedicated official ISO installer images 💿 for Malcolm and Hedgehog Linux 🦔 can be downloaded from Malcolm's releases page on GitHub. Due to limits on individual files in GitHub releases, these ISO files have been split 🪓 into 2GB chunks and can be reassembled with scripts provided for both Bash 🐧 (release_cleaver.sh) and PowerShell 🪟 (release_cleaver.ps1). See Downloading Malcolm - Installer ISOs for instructions.
As always, join us on the Malcolm discussions board 💬 to engage with the community, or pop some corn 🍿 and watch a video 📼.
#Malcolm #HedgehogLinux #Zeek #Arkime #Strelka #NetBox #OpenSearch #Elasticsearch #Suricata #PCAP #NetworkTrafficAnalysis #networksecuritymonitoring #OT #ICS #icssecurity #CyberSecurity #Cyber #Infosec #INL




 releases are published according to a fixed release schedule with security announcements between major releases.
releases are published according to a fixed release schedule with security announcements between major releases.