Are you on the safe side yet? 🛡️
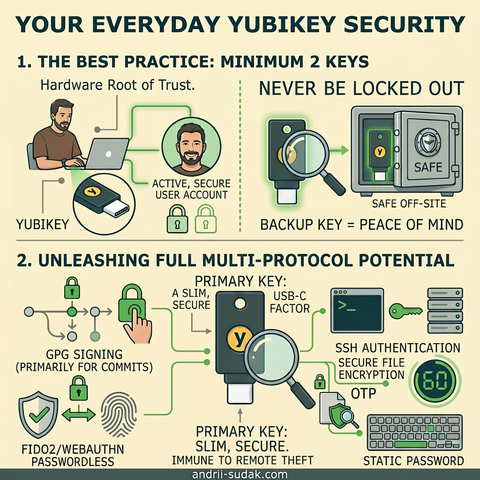
In an era of sophisticated phishing and data breaches, relying on passwords or SMS codes is like locking your front door but leaving the key under the mat. For a robust level of private security, I’ve integrated Yubico Yubikey into my daily routine as the ultimate hardware root of trust.
The true value of "Cold" Security
Hardware authenticators offer unparalleled security. Their physical nature means cryptographic keys are embedded directly, making them impossible to copy, extract, or steal remotely. No physical device, no access. Period.
My "Strict Security" Setup
I’ve minimized my attack surface by removing the weakest links:
1. Phone-Free: I have disabled phone number linkage and SMS authentication wherever possible to eliminate SIM-swapping risks.
2. Passwordless: Where supported, I use FIDO2/WebAuthn. No password means no password can be phished.
3. The Backup Rule: I use a minimum of two keys. My primary key is always with me, and a backup key is hidden in a secure, off-site location.
Hardware-Signed Workflow
I leverage the full multi-protocol potential of the key:
- GPG & Git: I use GPG primarily for signing git commits. When I push code, I am physically "touching" the hardware to sign that digital information.
- PIV/SSH: Secure access to servers without resident private keys on the machine.
- OTP & Static Passwords: Bridges for legacy services.
The Vault Strategy
For passwords and sensitive metadata, I rely on Bitwarden. Access to my vault is strictly locked behind my hardware keys.
> No, I'm not "that paranoid" ... yet. But I do keep an eye on the compromise of central servers. That’s why I’m planning to implement a fully self-hosted, self-controlled vault solution soon.
I’d love to hear your thoughts – what are your favorite self-hosted security stacks?
#CyberSecurity #YubiKey #Bitwarden #Infosec #Privacy #MFA #PGP #SSH #SecurityEngineering #SelfHosted