Shodan Dork Cheat Sheet
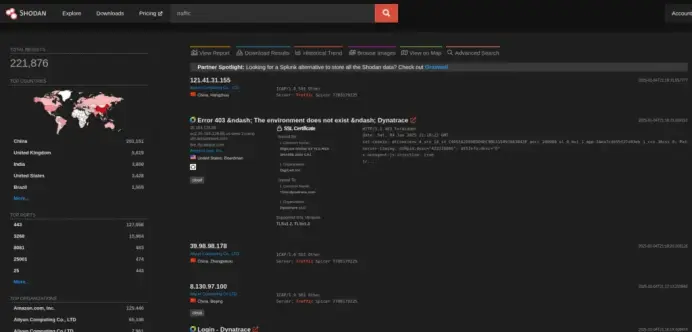
In this cheat sheet, I cover useful Shodan search queries, filtering techniques, and practical reconnaissance workflows for cybersecurity assessments
https://denizhalil.com/2023/12/19/shodan-dork-cheat-sheet/
#CyberSecurity #Shodan #OSINT #Reconnaissance #AttackSurface #ThreatIntelligence #Pentesting #RedTeam #InfoSec #EthicalHacking #SecurityResearch #DenizHalil