🌟 Excited to announce that I'll be presenting a talk at 𝐁𝐒𝐢𝐝𝐞𝐬 𝐀𝐭𝐡𝐞𝐧𝐬 on June 29th! 🌟
🎤 Title of the talk: "𝐅𝐫𝐨𝐦 𝐃𝐚𝐭𝐚 𝐃𝐞𝐥𝐮𝐠𝐞 𝐭𝐨 𝐀𝐜𝐭𝐢𝐨𝐧𝐚𝐛𝐥𝐞 𝐈𝐧𝐬𝐢𝐠𝐡𝐭𝐬 𝐰𝐢𝐭𝐡 𝐋𝐋𝐌𝐬: 𝐈𝐧𝐭𝐫𝐨𝐝𝐮𝐜𝐢𝐧𝐠 𝐓𝐈 𝐌𝐢𝐧𝐝𝐦𝐚𝐩"
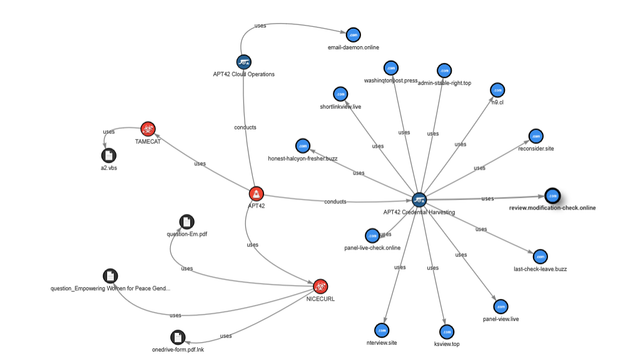
📜 I'll introduce TI Mindmap, an open-source project designed to empower Infosec professionals in navigating the complexities of Threat Intelligence write-ups. I'll explore how TI Mindmap leverages the capabilities of LLMs to enhance the efficiency of processing and extracting crucial information from a variety of Threat Intelligence sources.
Key Features of TI Mindmap:
▶Summarizing Threat Intelligence articles
▶Mapping entity relationships with Mindmaps
▶Engaging in AI-driven chats on your data
▶Generating comprehensive PDF reports
▶IOCs extraction
▶Extract adversary tactics, techniques, and procedures
▶TTPs by execution time
During the session, I'll not only showcase the capabilities of TI Mindmap but also share insights from development journey. I'll discuss the challenges we've encountered, the lessons we've learned, and the future directions of this open-source project.
🔗 Learn more about TI Mindmap, GitHub Repository: https://lnkd.in/dJDSQx8Y
BSides Athens: https://www.bsidesath.gr/
Tracks: https://lnkd.in/dC9znupr
#BSidesAthens #Cybersecurity #ThreatIntelligence #OpenSource #LLMs hashtag#AIdriven #TIMindmap #streamlit hashtag#mermaid #mindmap #TI #genai #python #mistral #openai #azureopenai #stix #ttp #conference #bsides