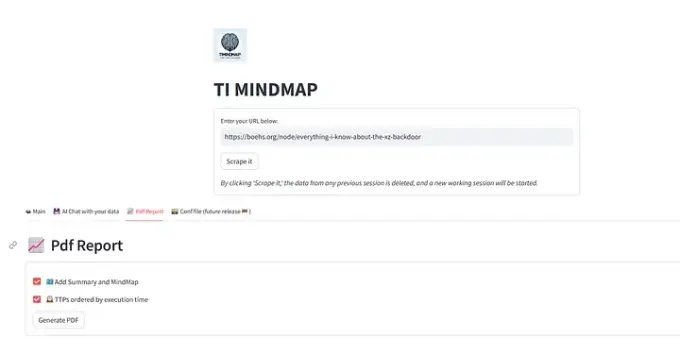
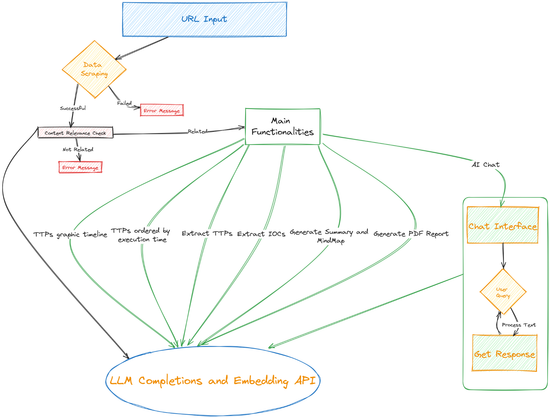
I share this report generated with 𝐓𝐈 𝐌𝐢𝐧𝐝𝐦𝐚𝐩.
Tool: https://ti-mindmap-gpt.streamlit.app/
I invite you to contribute and add a star on GitHub: https://github.com/format81/TI-Mindmap-GPT
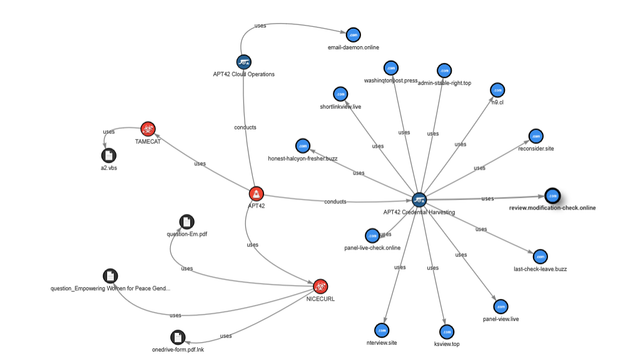
Title: 𝐍𝐞𝐛𝐮𝐥𝐚 𝐁𝐫𝐨𝐤𝐞𝐫: 𝐈𝐭𝐚𝐥𝐢𝐚𝐧-𝐛𝐚𝐬𝐞𝐝 𝐓𝐡𝐫𝐞𝐚𝐭 𝐎𝐩𝐞𝐫𝐚𝐭𝐢𝐨𝐧
Summary: 𝘛𝘩𝘦 𝘳𝘦𝘱𝘰𝘳𝘵 𝘱𝘳𝘦𝘴𝘦𝘯𝘵𝘴 𝘢𝘯 𝘢𝘯𝘢𝘭𝘺𝘴𝘪𝘴 𝘰𝘧 𝘰𝘧𝘧𝘦𝘯𝘴𝘪𝘷𝘦 𝘰𝘱𝘦𝘳𝘢𝘵𝘪𝘰𝘯𝘴 𝘤𝘰𝘯𝘥𝘶𝘤𝘵𝘦𝘥 𝘣𝘺 𝘢𝘯 𝘐𝘵𝘢𝘭𝘪𝘢𝘯 𝘵𝘩𝘳𝘦𝘢𝘵 𝘢𝘤𝘵𝘰𝘳 𝘬𝘯𝘰𝘸𝘯 𝘢𝘴 𝘕𝘦𝘣𝘶𝘭𝘢 𝘉𝘳𝘰𝘬𝘦𝘳. 𝘚𝘪𝘯𝘤𝘦 𝘦𝘢𝘳𝘭𝘺 2020, 𝘕𝘦𝘣𝘶𝘭𝘢 𝘉𝘳𝘰𝘬𝘦𝘳 𝘩𝘢𝘴 𝘦𝘮𝘱𝘭𝘰𝘺𝘦𝘥 𝘤𝘶𝘴𝘵𝘰𝘮-𝘮𝘢𝘥𝘦 𝘮𝘢𝘭𝘸𝘢𝘳𝘦 𝘵𝘰 𝘤𝘰𝘮𝘱𝘳𝘰𝘮𝘪𝘴𝘦 𝘴𝘺𝘴𝘵𝘦𝘮𝘴 𝘮𝘢𝘪𝘯𝘭𝘺 𝘪𝘯 𝘵𝘩𝘦 𝘵𝘳𝘢𝘯𝘴𝘱𝘰𝘳𝘵 𝘢𝘯𝘥 𝘢𝘦𝘳𝘰𝘯𝘢𝘶𝘵𝘪𝘤𝘴 𝘪𝘯𝘥𝘶𝘴𝘵𝘳𝘪𝘦𝘴. 𝘛𝘩𝘦 𝘷𝘪𝘳𝘶𝘴'𝘴 𝘱𝘦𝘳𝘷𝘢𝘴𝘪𝘷𝘦 𝘱𝘳𝘦𝘴𝘦𝘯𝘤𝘦 𝘢𝘤𝘳𝘰𝘴𝘴 𝘷𝘢𝘳𝘪𝘰𝘶𝘴 𝘴𝘦𝘤𝘵𝘰𝘳𝘴 𝘪𝘮𝘱𝘭𝘪𝘦𝘴 𝘵𝘩𝘢𝘵 𝘵𝘩𝘦 𝘵𝘩𝘳𝘦𝘢𝘵 𝘢𝘤𝘵𝘰𝘳 𝘪𝘴 𝘱𝘶𝘳𝘴𝘶𝘪𝘯𝘨 𝘢 𝘯𝘰𝘯-𝘵𝘢𝘳𝘨𝘦𝘵𝘦𝘥 𝘰𝘧𝘧𝘦𝘯𝘴𝘪𝘷𝘦 𝘴𝘵𝘳𝘢𝘵𝘦𝘨𝘺, 𝘢𝘯 𝘢𝘴𝘴𝘶𝘮𝘱𝘵𝘪𝘰𝘯 𝘴𝘵𝘳𝘦𝘯𝘨𝘵𝘩𝘦𝘯𝘦𝘥 𝘣𝘺 𝘵𝘩𝘦 𝘮𝘢𝘭𝘸𝘢𝘳𝘦'𝘴 𝘜𝘚𝘉 𝘱𝘳𝘰𝘱𝘢𝘨𝘢𝘵𝘪𝘰𝘯 𝘤𝘢𝘱𝘢𝘣𝘪𝘭𝘪𝘵𝘪𝘦𝘴.
𝘕𝘦𝘣𝘶𝘭𝘢 𝘉𝘳𝘰𝘬𝘦𝘳 𝘴𝘩𝘰𝘸𝘤𝘢𝘴𝘦𝘴 𝘥𝘪𝘴𝘵𝘪𝘯𝘤𝘵 𝘛𝘛𝘗𝘴 𝘵𝘩𝘢𝘵 𝘦𝘷𝘰𝘭𝘷𝘦 𝘰𝘷𝘦𝘳 𝘵𝘪𝘮𝘦. 𝘍𝘳𝘰𝘮 𝘣𝘶𝘤𝘰𝘭𝘪𝘤 𝘰𝘣𝘧𝘶𝘴𝘤𝘢𝘵𝘪𝘰𝘯 𝘢𝘯𝘥 𝘦𝘯𝘤𝘰𝘥𝘪𝘯𝘨 𝘵𝘦𝘤𝘩𝘯𝘪𝘲𝘶𝘦𝘴 𝘵𝘩𝘢𝘵 𝘦𝘮𝘱𝘭𝘰𝘺 𝘪𝘯𝘵𝘦𝘳𝘮𝘦𝘥𝘪𝘢𝘵𝘦 𝘎𝘪𝘵𝘏𝘶𝘣-𝘩𝘰𝘴𝘵𝘦𝘥 𝘧𝘪𝘭𝘦𝘴 𝘧𝘪𝘭𝘭𝘦𝘥 𝘸𝘪𝘵𝘩 𝘣𝘭𝘢𝘯𝘬 𝘴𝘱𝘢𝘤𝘦𝘴 𝘵𝘰 𝘵𝘩𝘦 𝘶𝘴𝘦 𝘰𝘧 𝘱𝘭𝘢𝘵𝘧𝘰𝘳𝘮𝘴 𝘭𝘪𝘬𝘦 𝘝𝘪𝘮𝘦𝘰 𝘢𝘯𝘥 𝘈𝘳𝘴𝘛𝘦𝘤𝘩𝘯𝘪𝘤𝘢 𝘧𝘰𝘳 𝘤𝘰𝘥𝘦 𝘩𝘰𝘴𝘵𝘪𝘯𝘨.
𝘈 𝘥𝘦𝘵𝘢𝘪𝘭𝘦𝘥 𝘪𝘯𝘴𝘱𝘦𝘤𝘵𝘪𝘰𝘯 𝘰𝘧 𝘵𝘩𝘦 𝘮𝘢𝘭𝘸𝘢𝘳𝘦'𝘴 𝘰𝘱𝘦𝘳𝘢𝘵𝘪𝘰𝘯 𝘳𝘦𝘷𝘦𝘢𝘭𝘴 𝘤𝘰𝘯𝘴𝘵𝘢𝘯𝘵 𝘥𝘰𝘸𝘯𝘭𝘰𝘢𝘥𝘴 𝘰𝘧 𝘢𝘥𝘥𝘪𝘵𝘪𝘰𝘯𝘢𝘭 𝘱𝘢𝘺𝘭𝘰𝘢𝘥𝘴 𝘶𝘱𝘰𝘯 𝘭𝘢𝘶𝘯𝘤𝘩𝘪𝘯𝘨 𝘙𝘶𝘯𝘵𝘪𝘮𝘦𝘉𝘳𝘰𝘬𝘦𝘳.𝘦𝘹𝘦. 𝘋𝘰𝘮𝘢𝘪𝘯𝘴 𝘢𝘳𝘦 𝘢𝘭𝘴𝘰 𝘳𝘦𝘨𝘶𝘭𝘢𝘳𝘭𝘺 𝘴𝘸𝘪𝘵𝘤𝘩𝘦𝘥 𝘵𝘰 𝘢𝘷𝘰𝘪𝘥 𝘱𝘳𝘦𝘥𝘪𝘤𝘵𝘪𝘷𝘦 𝘢𝘯𝘢𝘭𝘺𝘴𝘪𝘴 𝘧𝘳𝘰𝘮 𝘵𝘩𝘦 𝘤𝘺𝘣𝘦𝘳𝘴𝘦𝘤𝘶𝘳𝘪𝘵𝘺 𝘵𝘦𝘢𝘮. 𝘛𝘩𝘦 𝘳𝘦𝘱𝘰𝘳𝘵 𝘤𝘰𝘯𝘧𝘪𝘥𝘦𝘯𝘵𝘭𝘺 𝘢𝘵𝘵𝘳𝘪𝘣𝘶𝘵𝘦𝘴 𝘵𝘩𝘦 𝘢𝘵𝘵𝘢𝘤𝘬𝘴 𝘵𝘰 𝘕𝘦𝘣𝘶𝘭𝘢 𝘉𝘳𝘰𝘬𝘦𝘳 𝘸𝘪𝘵𝘩 𝘴𝘰𝘭𝘪𝘥 𝘦𝘷𝘪𝘥𝘦𝘯𝘤𝘦, 𝘪𝘯𝘤𝘭𝘶𝘥𝘪𝘯𝘨 𝘶𝘯𝘪𝘲𝘶𝘦 𝘮𝘢𝘭𝘸𝘢𝘳𝘦 𝘯𝘢𝘮𝘪𝘯𝘨 𝘤𝘰𝘯𝘷𝘦𝘯𝘵𝘪𝘰𝘯𝘴 𝘢𝘯𝘥 𝘐𝘵𝘢𝘭𝘪𝘢𝘯 𝘮𝘢𝘯𝘪𝘧𝘦𝘴𝘵𝘴 𝘪𝘯 𝘵𝘩𝘦 𝘨𝘦𝘯𝘦𝘳𝘢𝘵𝘦𝘥 𝘙𝘶𝘯𝘵𝘪𝘮𝘦𝘉𝘳𝘰𝘬𝘦𝘳.𝘦𝘹𝘦 𝘧𝘪𝘭𝘦𝘴.
𝘍𝘰𝘳 𝘥𝘦𝘵𝘦𝘤𝘵𝘪𝘰𝘯 𝘰𝘱𝘱𝘰𝘳𝘵𝘶𝘯𝘪𝘵𝘪𝘦𝘴, 𝘬𝘦𝘺 𝘐𝘖𝘊𝘴 𝘪𝘯𝘤𝘭𝘶𝘥𝘦 𝘶𝘯𝘪𝘲𝘶𝘦 𝘯𝘢𝘮𝘪𝘯𝘨 𝘱𝘢𝘵𝘵𝘦𝘳𝘯𝘴 𝘪𝘯 𝘴𝘰𝘮𝘦 𝘴𝘢𝘮𝘱𝘭𝘦𝘴, 𝘥𝘪𝘴𝘵𝘪𝘯𝘤𝘵 𝘊2𝘴 𝘶𝘵𝘪𝘭𝘪𝘻𝘦𝘥, 𝘦𝘯𝘤𝘰𝘥𝘦𝘥 𝘧𝘪𝘭𝘦𝘴 𝘦𝘹𝘱𝘭𝘰𝘪𝘵𝘦𝘥 𝘧𝘰𝘳 𝘮𝘢𝘭𝘸𝘢𝘳𝘦 𝘱𝘳𝘰𝘱𝘢𝘨𝘢𝘵𝘪𝘰𝘯, 𝘢𝘯𝘥 𝘵𝘩𝘦 𝘱𝘳𝘦𝘴𝘦𝘯𝘤𝘦 𝘰𝘧 𝘴𝘱𝘦𝘤𝘪𝘧𝘪𝘤 𝘧𝘪𝘭𝘦𝘴 𝘴𝘶𝘤𝘩 𝘢𝘴 “𝘙𝘶𝘯𝘵𝘪𝘮𝘦𝘉𝘳𝘰𝘬𝘦𝘳.𝘦𝘹𝘦”.
Original blog by Fortgale: https://fortgale.com/blog/featured/nebula-broker-offensive-operations-italy/
#timindmap #threatintelligence #ai #genai #openai #azureopenai #azure #ioc #ttp #timeline #soc #llm