Im Grunde benötige ich kein Reverse #Proxy um Dienste entsprechend öffentlich zu machen ist für meinen Spaß unnötig. Es geht auch per #Wireguard. Damit wird auch die Sicherheit meiner sensiblen Daten erhöht.
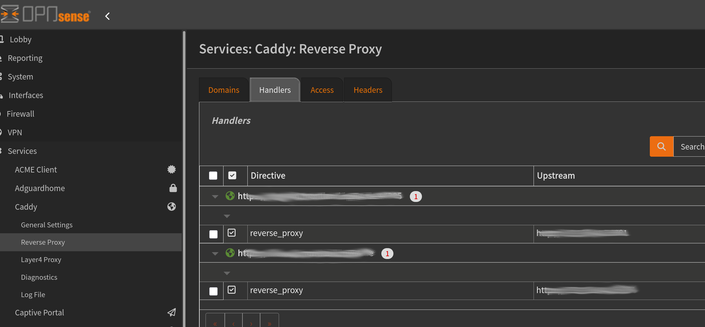
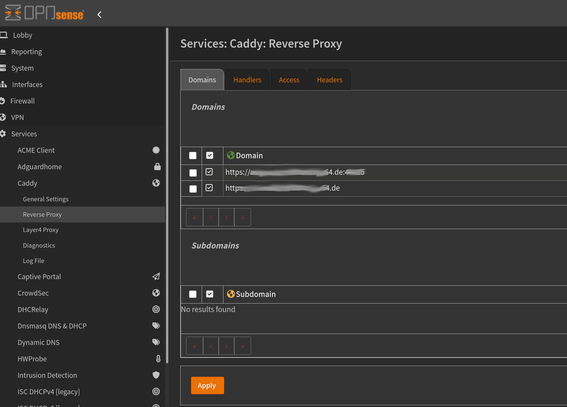
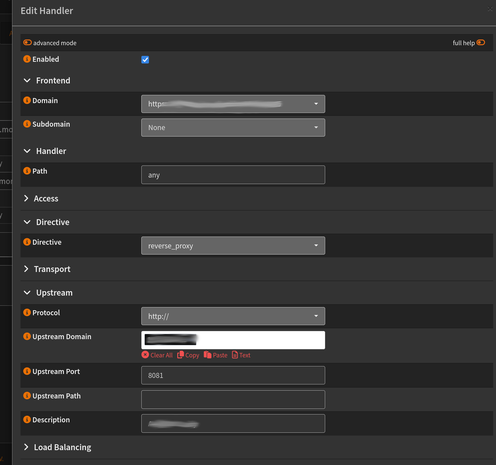
Trotzdem versuche ich dazu zulernen und diesmal ist #Caddy als #OPNsense #Plugin mein neues Tool. Als Proxy eine #DynDNS Adresse und lokal gebunden. Der externe Zugriff dann per Wireguard.
Домашний сервер без белого IP: безопасная публикация сервисов через VPS, обратный SSH-туннель и Caddy
Как безопасно опубликовать домашний сервер без белого IP и проброса портов: домашний сервер сам устанавливает исходящее SSH-соединение к VPS, на VPS создаётся локальный endpoint обратного SSH-туннеля, а внешний доступ к сервисам отдаётся через Caddy по HTTPS. Backend-порты вроде Nextcloud, Home Assistant или Jellyfin не открываются напрямую в интернет, а остаются доступными только через loopback и reverse proxy. Отдельное внимание уделено hardening: ограниченный пользователь tunneluser, SSH-ключи, autossh, systemd, UFW, проверка sshd_config и диагностика типовых ошибок. Поехали
Домашний сервер без белого IP: безопасная публикация сервисов через VPS, обратный SSH-туннель и Caddy
Аннотация Если домашний сервер находится за NAT или CGNAT, не имеет белого IP-адреса, а проброс портов на роутере невозможен или нежелателен, сервисы всё равно можно опубликовать безопасно. Один из...
VPS-бастион: доступ к домашнему серверу без белого IP
У вас дома крутятся полезные сервисы: Home Assistant, Jellyfin, code-server или Nextcloud. Или вы только собираетесь их запустить. Пока вы дома, всё открывается по локальному IP. Но стоит выйти за пределы квартиры, и сервисы пропадают. Причина: провайдер выдал серый IP-адрес, то есть применяет CGNAT. Белый адрес получить либо нельзя (примерно, как советский дефицит), либо он стоит дополнительных денег.
https://habr.com/ru/articles/1038186/
#VPS #SSHтуннель #проброс_портов #CGNAT #серый_IP #домашний_сервер #удаленный_доступ #autossh #systemd #Caddy
Finally I have a new #caddy server running which can get Lets Encrypt certificates but not be exposed to the internet by default.
Now to work out why when I connect with #wireguard it won’t connect to it.
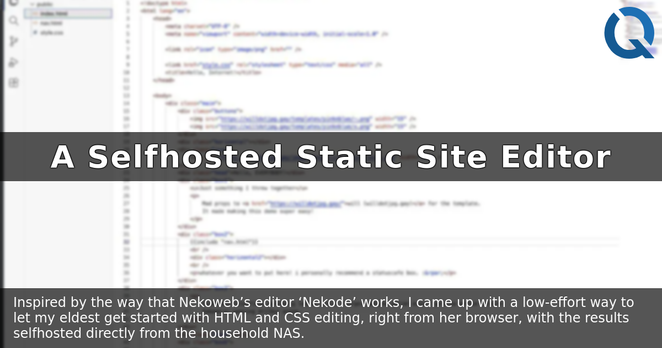
Imagine my pride when the eldest of my two #children, aged 12, said she'd like to learn #HTML and #CSS and build her own #staticSite.
I briefly considered pointing her at e.g. #NekoWeb, but then realised: hey - I've got a #NAS and a full fibre connection: I could #selfhost something "like" the Nekode editor, right?
A couple of dozen lines of #Caddy and Docker configuration later, she had a working browser-based #VSCode with drag-drop file support that publishes directly to her domain. Super easy. Highly recommended.
Here's how I did it:
🔗 https://danq.me/selfhosted-static-site-editor
Inspired by the way that Nekoweb's editor 'Nekode' works, I came up with a low-effort way to let my eldest get started with HTML and CSS editing, right from her browser, with the results selfhosted directly from the household NAS.
Read more: https://danq.me/2026/05/22/selfhosted-static-site-editor/
#article #caddy #css #geocities #hosting #html #indieweb #nas #smolweb #textEditors #webDesign #webDevelopment
We're cookin', y'all.
I'll be done soon, but just you wait, it's getting brown on the edges.
#sigal #python #caddy #selfhosted