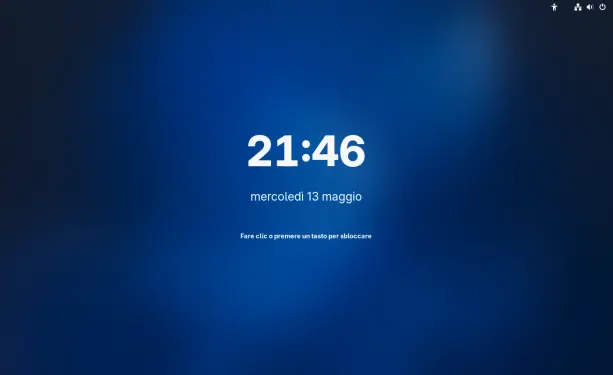
We forked the #KDE Plasma Login Manager. It now runs on #X11, drops privileges after init, and supports #systemd-free too. We tested it on Artix Linux with OpenRC, CachyOS with systemd, and on the #FreeBSD-based GhostBSD. https://www.youtube.com/watch?v=rTnV7-nfgX4 https://github.com/Sonic-DE/sonic-login-manager