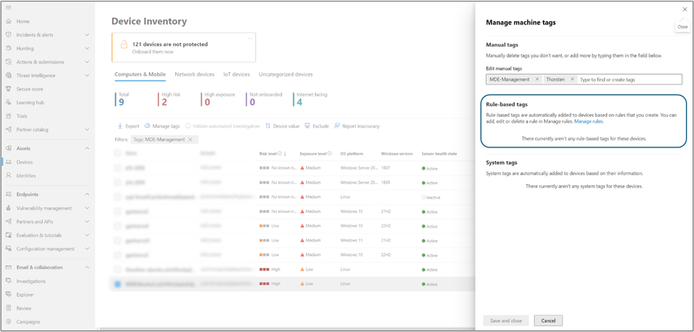
𝐌𝐚𝐧𝐚𝐠𝐞 𝐲𝐨𝐮𝐫 𝐝𝐞𝐯𝐢𝐜𝐞𝐬 𝐰𝐢𝐭𝐡 𝐞𝐚𝐬𝐞 𝐮𝐬𝐢𝐧𝐠 𝐝𝐲𝐧𝐚𝐦𝐢𝐜 𝐫𝐮𝐥𝐞𝐬 𝐟𝐨𝐫 𝐝𝐞𝐯𝐢𝐜𝐞 𝐭𝐚𝐠𝐠𝐢𝐧𝐠 𝐢𝐧 𝐌𝐢𝐜𝐫𝐨𝐬𝐨𝐟𝐭 𝐃𝐞𝐟𝐞𝐧𝐝𝐞𝐫
We are excited to announce that dynamic rules for tagging devices is now generally available. This feature enables security teams to create and manage rules that automatically assign and remove tags from devices based on user-defined criteria directly in the Microsoft Defender portal.
Dynamic tags:
- simplify tag management,
- reduce manual efforts,
- facilitate efficient device tracking,
- simplify compliance by automatically categorizing non-compliant devices
#edr #xdr #defender #defenderxdr #microsoft365defender #endpoint #management #tag #device #compliance #microsoft #microsoftsecurity #soc #cloudsecurity #cloud #cloudnative