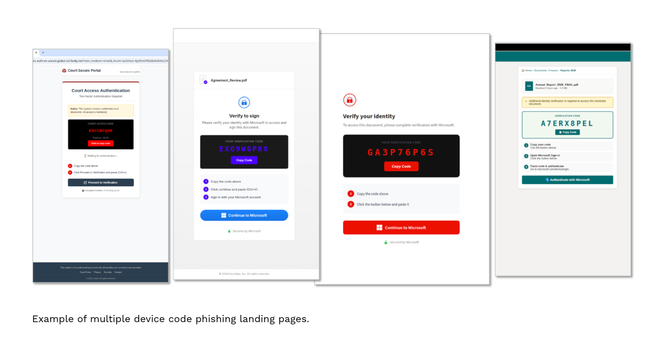
Device code phishing is exploding across the threat landscape, with new device code phishing tools emerging every week.
The technique abuses legitimate enterprise resources for account takeovers. It involves social engineering to trick a target into authorizing a malicious app on their enterprise email accounts.
It was first observed around 2020 but has grown in popularity over recent years due to the publication of criminal device code phishing tools and on-demand code generation.
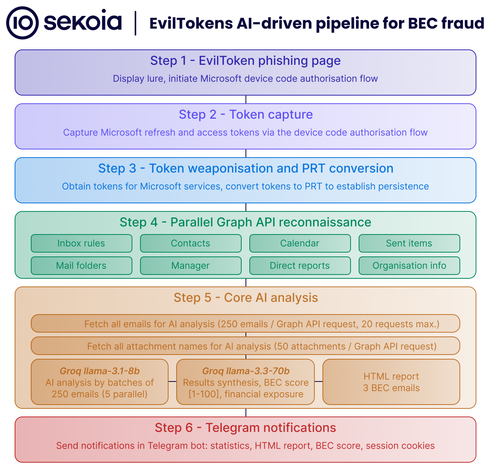
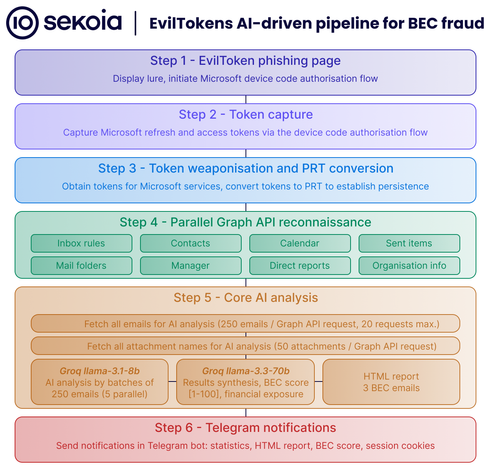
Successful attacks can lead to:
• Full account takeover
• Theft of sensitive information
• Fraud and business email compromise
• Lateral movement within a compromised environment
• Ransomware
Our new research blog explores why adoption of this technique has surged over the past year, shows real campaign examples, and offers defense recommendations.