𝐌𝐢𝐜𝐫𝐨𝐬𝐨𝐟𝐭 𝐃𝐞𝐟𝐞𝐧𝐝𝐞𝐫 𝐟𝐨𝐫 𝐀𝐏𝐈 𝐒𝐞𝐜𝐮𝐫𝐢𝐭𝐲 𝐃𝐚𝐬𝐡𝐛𝐨𝐚𝐫𝐝
Microsoft Defender for API plan provides amazing capabilities like
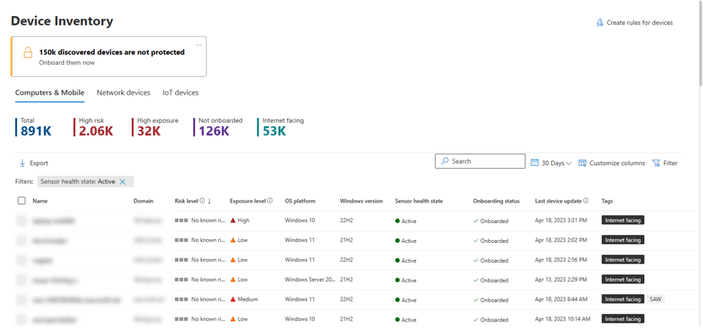
➡️visibility to business-critical managed APIs
➡️security findings to investigate and improve your API security posture
➡️sensitive-data classification (API data classification)
➡️real-time threat detection that generates alerts for suspicious activities.
➡️misconfiguration finding
➡️security recommendations
and more.
Defender for API Security Dashboard allows you to visualize the state of your API posture for the API endpoints that you have onboarded to better understand your unhealthy recommendations and the identified data classifications, authorization status, usage, and exposure of your APIs.
https://techcommunity.microsoft.com/t5/microsoft-defender-for-cloud/microsoft-defender-for-api-security-dashboard/ba-p/3848291
#azure #microsoftsecurity #microsoft #defender #xdr #api #apisecurity #soc #monitoring #cybersecurity #securityplatform #security #cloud #cloudnative #threat #threatdetection