With access to one of the largest, most diverse data sets in all of cybersecurity, Proofpoint is dedicated to tracking and reporting threat actors and their evolving TTPs. This research blog (brnw.ch/21wQMTw) is packed full of new threat insights including...
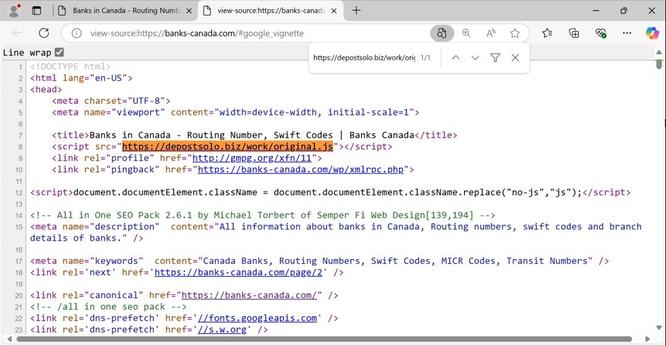
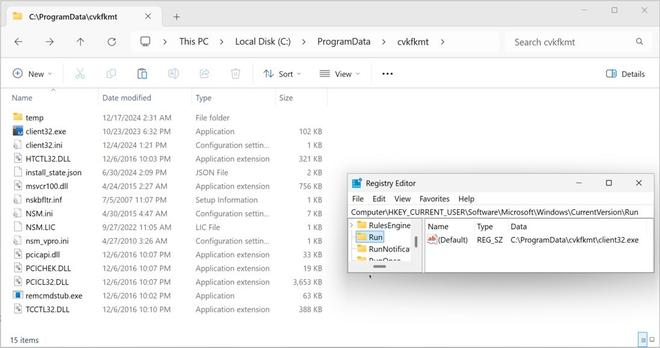
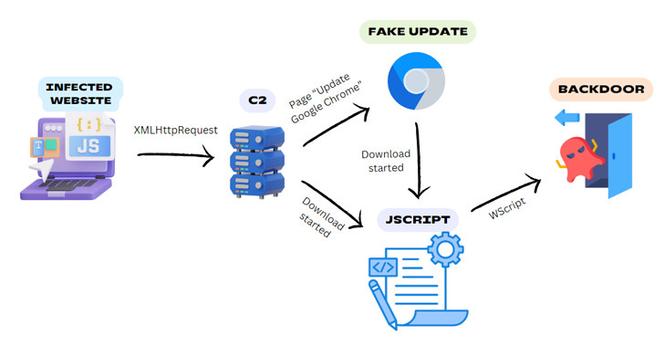
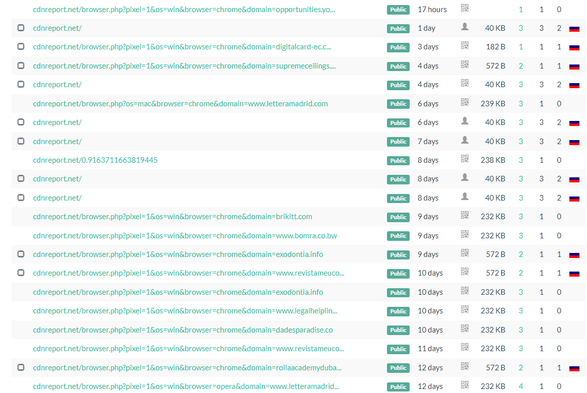
🔍 #TA2726 and#TA2727, two new cybercriminal threat actors who operate components of web inject campaigns.
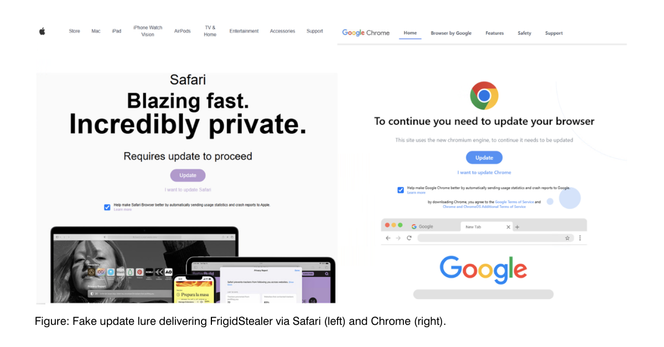
🔍 #FrigidStealer, a new info stealer for Mac computers delivered alongside malware for Windows and Android hosts.
See our blog for full details, Emerging Threats signatures, and IOCs.
#FakeUpdates #socialengineering #MacOS #TA569 #SocGholish