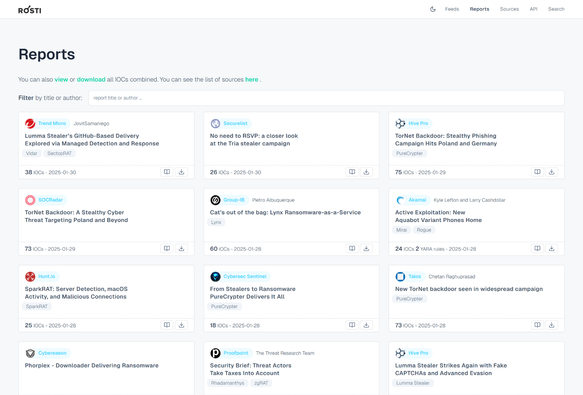
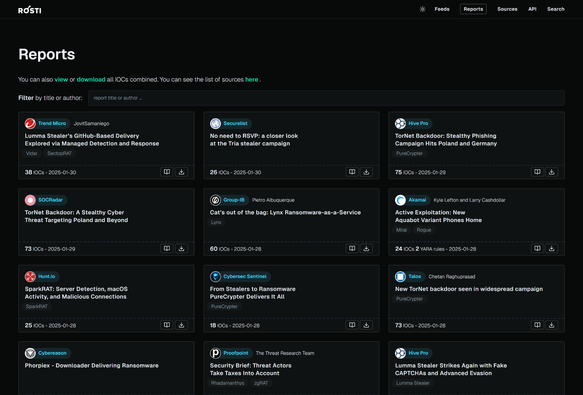
@threatcat_ch is tracking BSC as well, and we share our gained information on Threatfox/MalwareBazaar @abuse_ch As a side note, most of the delivered payloads led to Rhadamantys (https://malpedia.caad.fkie.fraunhofer.de/details/win.rhadamanthys) instead of Lumma in the last few days.
ThreatCat.ch has been founded in the autumn 2022 and consists of a bunch of experienced Cyber Threat Analysts and Incident Responders who have been working together for many years. We decided to create ThreatCat.ch to be able to serve the community by providing warnings and insights about emerging cyber threats. Occasionally we may also write about tools and tricks we have learned in our daily work life. And of course, ThreatCat.ch is about having fun doing interesting stuff together.
Currently we are publishing information on https://twitter.com/threatcat_ch and https://github.com/threatcat-ch/. All our information is distributed under Creative Commons CC BY 4.0 and all our opinions is ours and not that of our employers. You can always reach out to us via [email protected].
| https://twitter.com/threatcat_ch | |
| Bluesky | @threatcat-ch.bsky.social |
| GitHub | https://github.com/threatcat-ch |