PROSPERO & Proton66: Uncovering the links between bulletproof networks
#SocGholish #FakeBat #Coper #AS198953 #AS200593
Researchers report a surge in #FakeBat #malware infections from malvertising, targeting users searching for business software via trojanized MSIX installers.
https://thehackernews.com/2024/08/cybercriminals-exploit-popular-software.html
It's time to buckle up and stay alert because cybercriminals are on the prowl, spreading FakeBat malware through popular software searches. Yes, you heard it right – your favorite software could be a potential gateway for these sneaky hackers to infiltrate your devices.
#Cybercrime #FakeBatMalware #Cybersecurity #MalwareAttack #SoftwareSecurity #PopularSoftwareSearches #CyberCriminals #FakeBat
https://cloudhosting.evostrix.eu/cybercriminals-spread-fakebat-malware-through-popular-software-searches/
「 #FakeBat #Loader #マルウェア が #ドライブバイ ダウンロード 攻撃を通じて広く拡散 」: The Hacker News
「FakeBat として知られるローダー アズ ア サービス (LaaS) は、今年ドライブバイ ダウンロード技術を使用して配布される最も広範囲に及ぶローダー マルウェア ファミリの 1 つとなっていることが、Sekoia の調査結果で明らかになりました。
「FakeBat は主に、 IcedID 、 Lumma 、 RedLine 、 SmokeLoader 、 SectopRAT 、 Ursnif などの次段階のペイロードをダウンロードして実行することを目的としている 」と同社は 火曜日の分析で 述べた。 」
https://thehackernews.com/2024/07/fakebat-loader-malware-spreads-widely.html
🔍 The Sekoia TDR team delved into the drive-by download technique used for malware distribution via web browsing.
Our latest report analyses #FakeBat, a widespread loader using this technique.
https://blog.sekoia.io/exposing-fakebat-loader-distribution-methods-and-adversary-infrastructure/
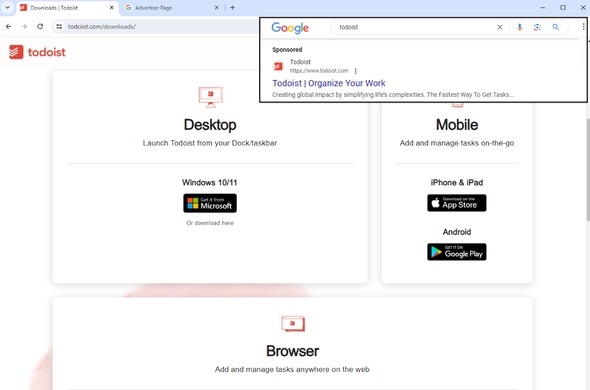
Malicious Google ad for Todoist -> #Fakebat
todciist[.]com
hxxps[://]ultra-fasteners[.]com/data/Todoist-x86[.]msix
C2: cdn-inform[.]com
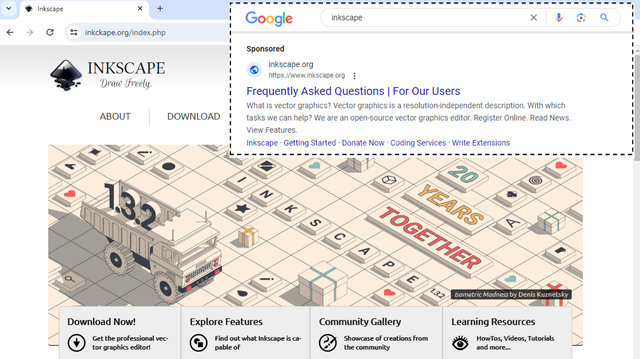
⚠️ Malicious Google ad for
inkscape leads to #FakeBat
➡️ Impostor site: inkckape[.]org
➡️ Payload:
hxxps[://]planbooknfly[.]com/data/Inkscape-x86[.]msix
dc471b087413ea64f7693b27e38ac568dea00ec1c7f699e48a6ef96b9cb4e30e
➡️ C2: utm-adschuk[.]com
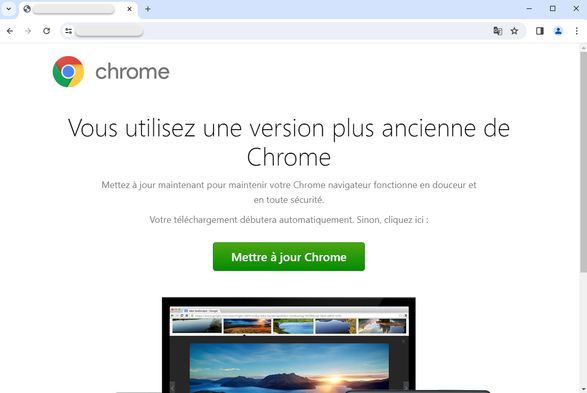
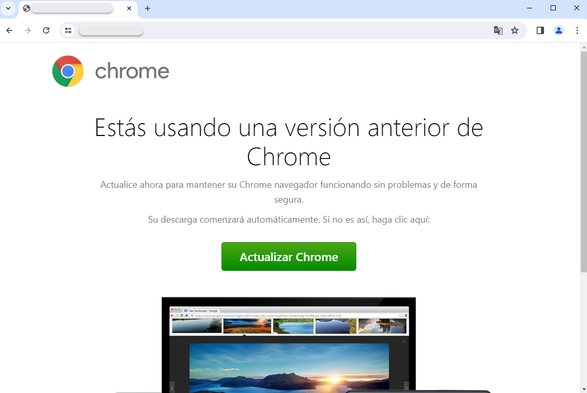
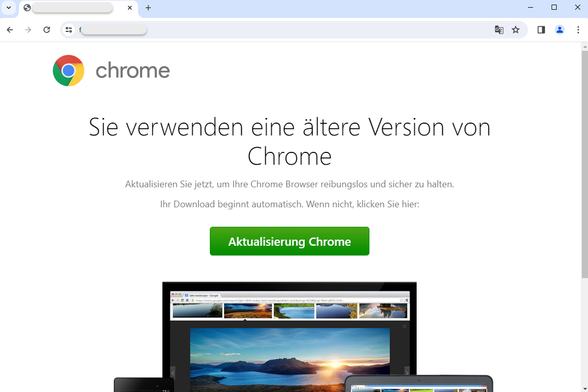
#SocGholish (AKA FakeUpdates) landing page localized in French, Spanish and German.
Payload is #FakeBat.
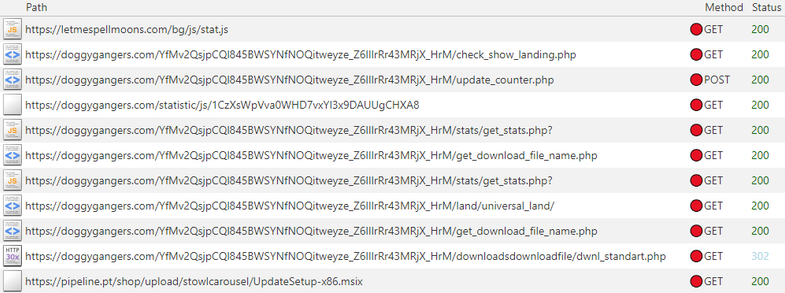
This campaign is also known as 'doggygangers' based on network traffic.
Cross posting from eSentire Threat Intel on Twitter, curious if anyone has seen this yet.
The payload they listed is tagged by Mandiant as UNC4536 on VT, which is associated with eugenloader, which makes sense given the payload here. Very interesting switch from them to do a fake update compared to their usual delivery by camping on web forums.
https://twitter.com/esthreat/status/1778121392933794299?s=46&t=HKDXXwkgNa-X1sZatgSsHQ
“eSentire's Threat Response Unit has observed #FakeBat loader🦇 being distributed via #FakeUpdates, ultimately leading to #LummaC2 infection via a custom-written PaykRunPE provided by the FakeBat Threat Actors.
@eSentire
✅ MSIX payload: UpdateSetup-x86.msix (MD5: 569d206636b75c33240ba4c1739c04d6)
✅ Initial check-in with C2: hxxps://utm-msh[.]com/profile/
✅LummaC2: awardlandscareposiw[.]shop
✅LummaC2 LID: G5nXy1--“
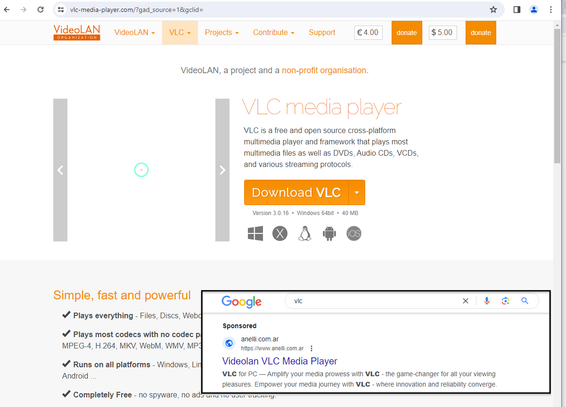
Google ad for VLC media player leads to #malvertising and drops #FakeBat
Fake site: vlc-media-player[.]com
Payload: fabulousfontshop[.]com/vlc-3[.]0[.]20-win64[.]msix
C2: utm_adsname[.]com