Matryoshka #3/3: Gamaredon's Gammasteel Infostealer
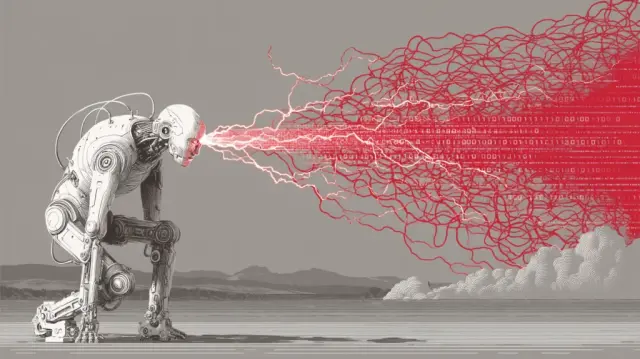
This analysis examines Gamaredon's (UAC-0010, Armagedon) advanced espionage operations targeting Ukrainian government, military, and critical infrastructure. The FSB-operated group deploys GammaSteel, a sophisticated stealer operating almost entirely from memory using Windows DPAPI encryption and storing 71 distinct payload functions in the HKCU\Printers registry key. The malware employs three concurrent data acquisition mechanisms: timed drive scans, USB monitoring for air-gapped systems, and real-time file surveillance. Exfiltration occurs via legitimate S3-compatible cloud storage (Tebi.io) with fallback to operator-controlled servers. The infection chain extensively uses VBScript for evasion, Dead Drop Resolvers on platforms like Telegram and Mastodon for C2 configuration, and includes bidirectional backdoor capabilities enabling arbitrary remote code execution. Infrastructure demonstrates high automation with servers rotated approximately every 24 hours.
Pulse ID: 6a21844636a81843ce1af3cc
Pulse Link: https://otx.alienvault.com/pulse/6a21844636a81843ce1af3cc
Pulse Author: AlienVault
Created: 2026-06-04 13:57:26
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#BackDoor #Cloud #CyberSecurity #Encryption #Espionage #Gamaredon #Government #InfoSec #InfoStealer #Malware #Military #OTX #OpenThreatExchange #RAT #RemoteCodeExecution #SMS #Telegram #Troll #UK #USB #Ukr #Ukrainian #VBS #Windows #bot #AlienVault