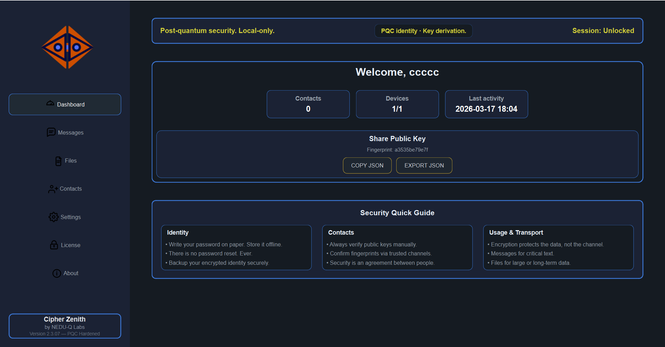
Cipher Zenith is finally breathing. 🌿
More than an app, it's a fort of digital sovereignty built in Chile. Implementing NIST Category 5 (ML-KEM/ML-DSA) has been a brutal but rewarding journey. 🔒
Seeing high-level defense tech become a fluid, local-first experience makes the code worth it. Real privacy: no clouds, no masters. Just you and your data. ✨
@infosec
@matthew_d_green
@hyperelliptic
@filippo
#PQC #CyberSecurity #BuildInPublic #NIST #Cryptography #Privacy