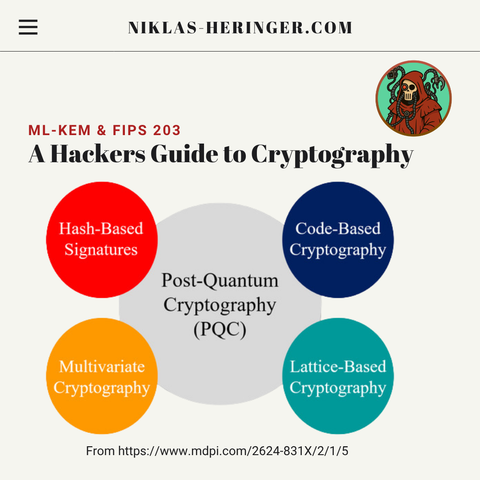
Quantum computing will not break #DNSSEC tomorrow, but @icann's latest #OCTO paper makes it clear that post quantum cryptography ( #PQC ) is no longer just a distant topic for the #DNS community.
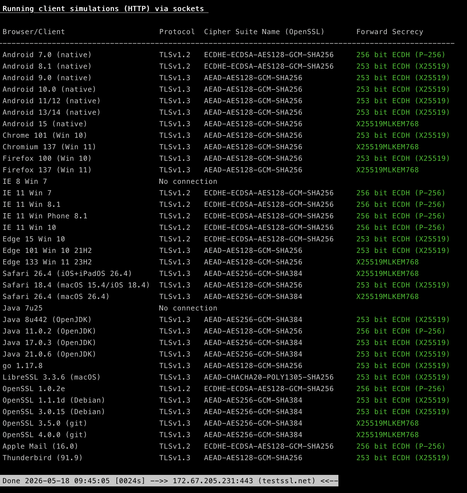
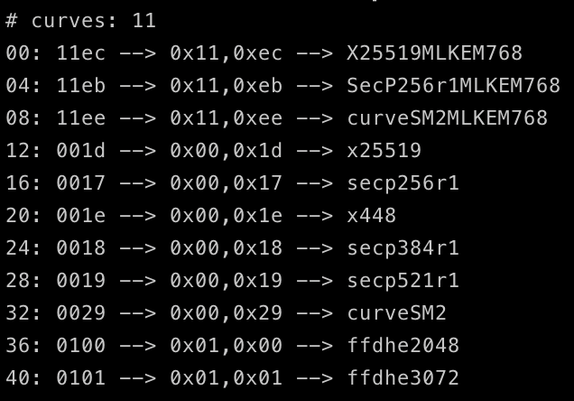
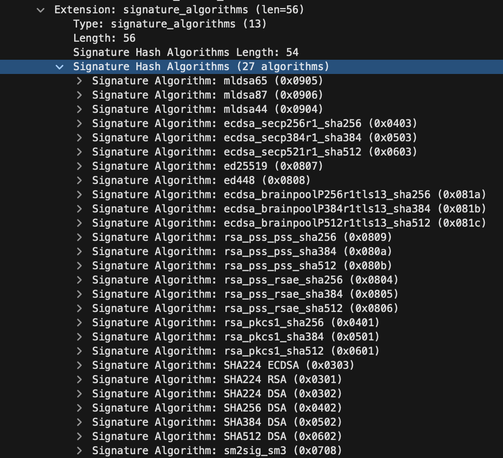
Which algorithm is cryptographically sufficiently strong, and which actually performs well in conjunction with DNS response sizes, signing processes, resolvers, and authoritative servers?
https://www.icann.org/en/system/files/files/octo-031-25may26-en.pdf