@LukaszOlejnik Banning stupid nonsense reset questions too? Nice.
Some of these have already been standardized in previous iterations (e.g. no mandatory password cycling) but I don't recall having seen that one before.
I think the requirement to allow arbitrary Unicode is new (and very much needed).
@kickingvegas @azonenberg @LukaszOlejnik
I am very much in favor of allowing all Unicode in passwords. On the other hands the user interface should warn the user when choosing the password that they may not be able to _produce_ specific characters on other computers/smartphones (e.g. when traveling and using foreign infrastructure). This can easily be an issue for inexperienced users for some services.
@LukaszOlejnik I thought this was already the case, but maybe I'm only thinking of the password rotation requirement.
Unfortunately, despite NIST's stance, the misery will remain for many of us until the PCI (payment card industry) standards also change.
And I was pushing for that for a long time
But I think that "should not" require password rotation goes to far. For some cases, once a year is, IMHO, more than justified.
@LukaszOlejnik
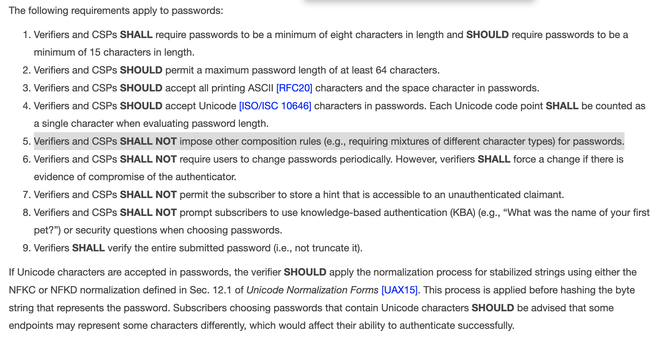
@BenAveling @mdwyer @LukaszOlejnik NIST SP 800-63B (updated 2017-06) section 5.1.1.2:
“Verifiers SHOULD NOT impose other composition rules (e.g., requiring mixtures of different character types or prohibiting consecutively repeated characters) for memorized secrets. Verifiers SHOULD NOT require memorized secrets to be changed arbitrarily (e.g., periodically). However, verifiers SHALL force a change if there is evidence of compromise of the authenticator.”
Edit: I see now this thread is about the latest version of SP 800-63B! The one I quoted above is 800-63-3, which has been replaced by 800-63-4. Seems they turned a bunch of SHOULD NOTs into SHALL NOTs.
@LukaszOlejnik Direct link to the screenshotted part;
Wonder how long till this flows to our insurance and thus IT at work.
@LukaszOlejnik Finally I can stop storing nonsense answers to KBA questions in my password manager.
Why yes, my first pet's name was G0dzi11a7heHun, why do you ask?
This! I actually had one site that (which I was on the phone with for some reason) said "oh, you'd like to use a secondary password instead of a security question?" and totally cool with it. I was shocked, in a good way.
Password managers only work for websites. For everything else, and it is most of the systems I deal with, we need to remember the password. And how do we authenticate to our password manager if the passwords are too long to remember?
These NIST standards are for password authentication. Everything from websites (your use case) to things that require a keyboard and VGA. You are making the argument that everything should use a hardware token. A different set of NIST standards. A different set of risks. Password managers have another set of risks. Okta was compromised via a password manager. Passwords are bad, but you fundamentally misunderstand the scope of the problem.
Setting that max to at least 64 is pretty solid.
Plus the document says it SHOULD be at least 64 characters, not that it SHALL be. And again, it says characters, and says that multiple bytes unicode characters should be counted as one single character, so the 64 characters thing sounds really arbitrary.
Maybe when this rule takes effect, I'll finally be allowed to create reasonable, easy-to-remember passwords for #banking apps! They're notorious for having terrible #password requirements.