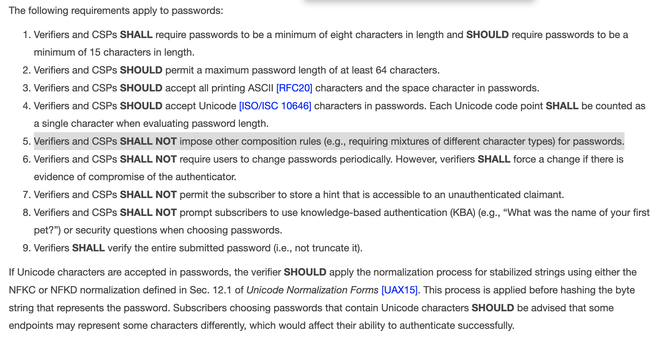
GREAT change is approaching. NIST will standardise prohibition of requirement of composing passwords from various character styles, and requirement for periodic password changes. These are harmful and obsolete rules. Now they will be treated as a cybersecurity weakness https://pages.nist.gov/800-63-4/sp800-63b.html
@LukaszOlejnik I still don't get why they should limit the password length.
@delegatevoid @LukaszOlejnik Upper limits on passphrase length are mostly about closing a possible resource exhaustion vector on the authenticating system. If you hash it all down to 64 bytes, there’s no point dealing with passphrases longer than 128 characters. Further characters don’t add any further entropy, but if you have no upper bound, some knucklehead is going to make your server hash the entirety of War and Peace over and over.
@bob_zim @LukaszOlejnik Ah yes, that does make sense. Still I would have liked them to put the maximum length at 128. The minimum length should be long enough so no human can possibly remember it (to discourage them from doing exactly that, and to force them to use a password manager) and the maximum has to make sense like you explained.
Password managers only work for websites. For everything else, and it is most of the systems I deal with, we need to remember the password. And how do we authenticate to our password manager if the passwords are too long to remember?
@dmaonR @bob_zim @LukaszOlejnik I have over 500 accounts in different systems, I don't remember a single one of them. Password managers work great for any system that requires a password, I don't see why it would only work for websites. What you are probably saying is that you use browsers plugins which help you fill in usernames/passwords in web browsers. And some password managers can also input data into other apps. (Acting as a keyboard or using the copy/paste buffer automatically)
@dmaonR @bob_zim @LukaszOlejnik As for authenticating / entering the master password for the password manager, there are many solutions. You can remember a passphrase for that, or like me, you can use a hardware device (in my case a device that authenticates my fingerprint and then inputs the master password as a keyboard). We also built a simple HID device with a very cheap USB chip that stored a master password and typed it into the PC upon touching the device. So I remember nothing.
@dmaonR @bob_zim @LukaszOlejnik And if you're looking at open source solutions, #keypass for example allows you to write plugins (C#) that "provide" the master password to keypass so that means you can develop anything you want to act as a master password provider.
@delegatevoid
These NIST standards are for password authentication. Everything from websites (your use case) to things that require a keyboard and VGA. You are making the argument that everything should use a hardware token. A different set of NIST standards. A different set of risks. Password managers have another set of risks. Okta was compromised via a password manager. Passwords are bad, but you fundamentally misunderstand the scope of the problem.
These NIST standards are for password authentication. Everything from websites (your use case) to things that require a keyboard and VGA. You are making the argument that everything should use a hardware token. A different set of NIST standards. A different set of risks. Password managers have another set of risks. Okta was compromised via a password manager. Passwords are bad, but you fundamentally misunderstand the scope of the problem.
@LukaszOlejnik @delegatevoid one practical reason is that bcrypt has an input length limit of 72 chars