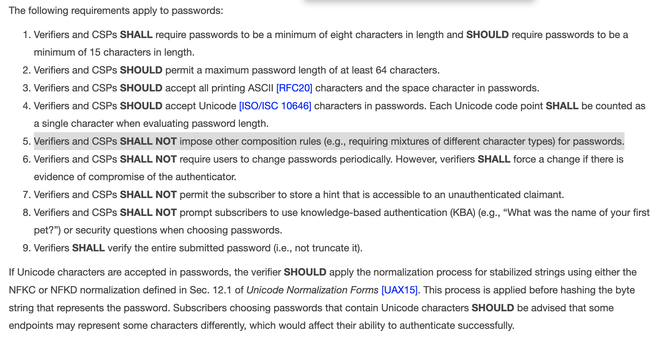
GREAT change is approaching. NIST will standardise prohibition of requirement of composing passwords from various character styles, and requirement for periodic password changes. These are harmful and obsolete rules. Now they will be treated as a cybersecurity weakness https://pages.nist.gov/800-63-4/sp800-63b.html
@LukaszOlejnik cringe that they still allow a maximum password length. There's literally no need for that
@miles @LukaszOlejnik Kind of? Bcrypt caps out at 72, and that's what you'll see a lot of stuff using.
Setting that max to at least 64 is pretty solid.
Setting that max to at least 64 is pretty solid.
@privateger @LukaszOlejnik Mhhh, I'm reading more about it. I find it silly that bcrypt has a cap at 72 bytes. I don't really have the brainpower right now to understand why that limitation was needed, but I wonder if it could be increased and if we could use a normal hashing function in the first step (from the little I've understood you need an arbitrary limit, but it doesn't have to be 72 bytes), call this algorithm something else and use this one.
Plus the document says it SHOULD be at least 64 characters, not that it SHALL be. And again, it says characters, and says that multiple bytes unicode characters should be counted as one single character, so the 64 characters thing sounds really arbitrary.
Plus the document says it SHOULD be at least 64 characters, not that it SHALL be. And again, it says characters, and says that multiple bytes unicode characters should be counted as one single character, so the 64 characters thing sounds really arbitrary.