Hey infosec folks 👋
I built RYN27 — a free, open-source CLI recon tool written in Python.
MIT licensed — fork it, contribute, do whatever you want with it.
I’d love feedback from people who actually do this work.
What it does:
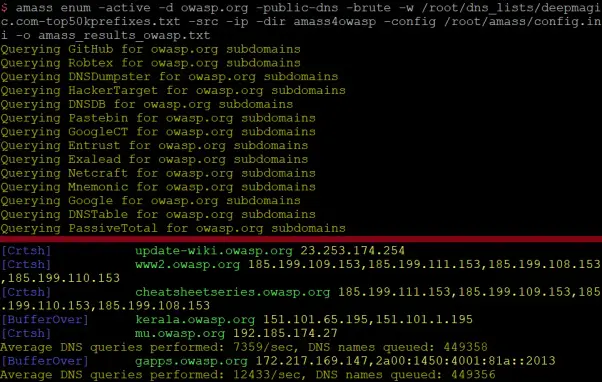
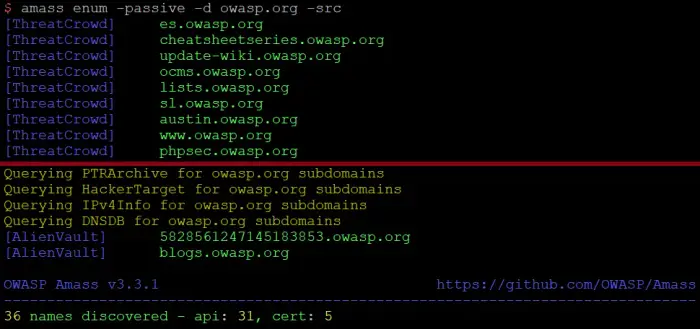
🔍 WHOIS · Full DNS enumeration · Subdomain brute-force
🔒 SSL/TLS cert inspection with expiry countdown
⚡ Threaded port scan + banner grabbing (30 workers)
📊 HTTP security header audit with 0–100% scoring
🌍 IP geolocation + proxy/VPN detection
✉️ Email & contact harvester
🛠️ Tech stack fingerprinting
📄 robots.txt reader, metadata crawler, zone transfer
19 modules. One interactive menu. Zero config.
Runs on:
Linux · macOS · Windows · Termux ✓
All dependencies auto-install on first run.
If you try it — I genuinely want to know:
→ What’s missing?
→ What’s broken?
→ What would you do differently?
Open to all feedback, suggestions, PRs, criticism — all of it. 🙏
🔗 https://github.com/ruyynn/RYN27
⭐ A star helps more people find it
#infosec #bugbounty #osint #recon #pentesting #opensource #python