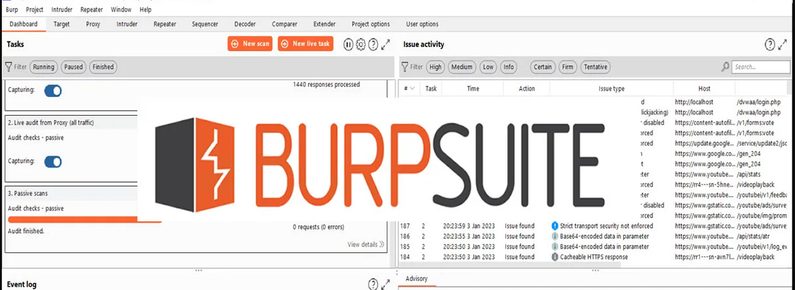
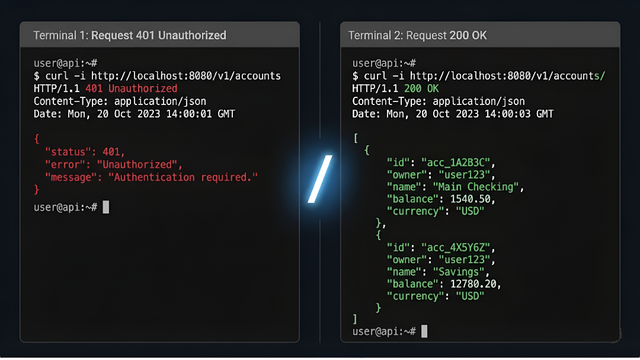
What is Web Security and Web Penetration Testing Tools
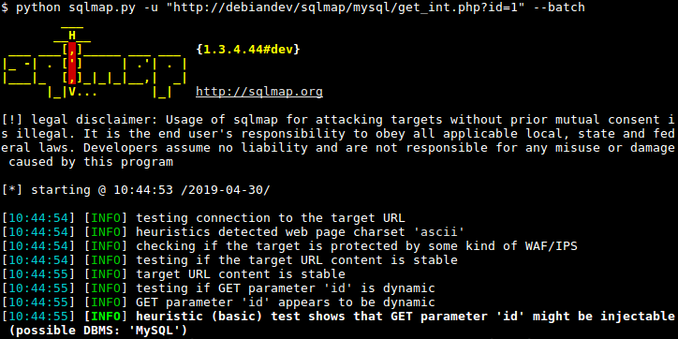
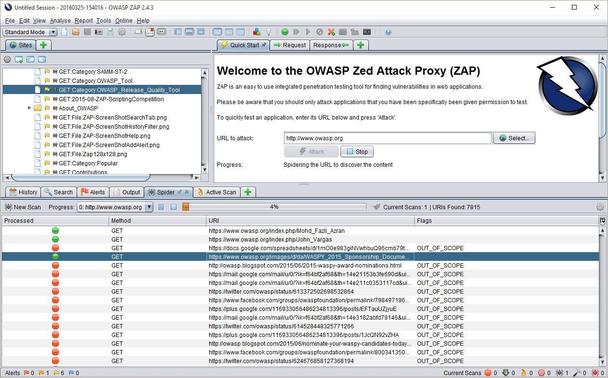
In this article, I cover essential web penetration testing tools and how they fit into different stages of the assessment process.
https://denizhalil.com/2024/12/19/web-penetration-testing-tools/
#CyberSecurity #WebSecurity #Pentesting #BurpSuite #Nmap #SQLMap #BugBounty #RedTeam #InfoSec #EthicalHacking #SecurityTools #DenizHalil



 🐘
🐘