When Old Breaches Meet New Code: Why Historical Leaks Still Matter
This vulnerability demonstrates the persistence of historical breaches in current systems due to a lack of code updates or inadequate data sanitization. In this instance, the application used email addresses from an old data breach in its password recovery feature, allowing attackers to obtain user credentials by matching leaked emails to hashed passwords in a rainbow table (a precomputed table of hashed passwords). The attacker was able to bypass rate-limiting and CAPTCHA protections by using a Python script to automate the process. The mechanism relied on a combination of brute force and dictionary attacks, taking advantage of weak password choices by some users. The impact was significant, as attackers could gain unauthorized access to user accounts. No bounty amount was disclosed, but the platform addressed the issue by implementing a more secure password recovery process that no longer relies on leaked email addresses. Key takeaway: Keep your code updated and data secure by regularly sanitizing and rotating credentials from historical breaches. #BugBounty #Cybersecurity #WebSecurity #PasswordRecovery #DataBreach
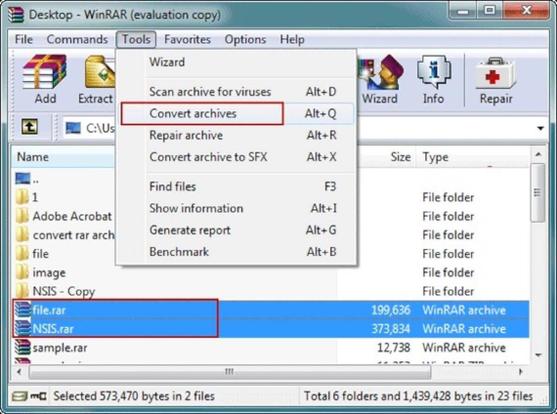
Need to remove the password from a WinRAR file without losing your data? 🔐📂 Discover a simple, safe method to unlock your files and regain access in no time! Check out the full guide here! ⬇️ #TechTips #WinRAR #PasswordRecovery #FileManagement
https://pupuweb.com/how-can-you-remove-password-from-winrar-file-without-losing-data/
So if you are an idiot like me and install a Windows 11 VM using TPM and set a complex password that you obviously will forget, there is a way to recover from this.
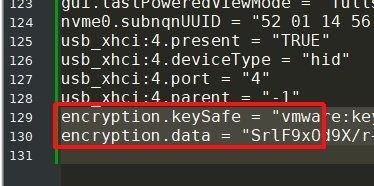
1. Open up the .vmx file in the VM folder.
2. Delete the following lines from the file (also seen in picture)
-> encryption.keySafe
-> encryption.data
3. Save the .vmx file
4. Open up the VM, go into settings, hardware.
5. Remove the TPM.
6. Go to options -> access control. Chose to encrypt the VM (forgot this step in my original post).
7. Now - numb-nuts - set a password for the TPM that you will remember.
8. Add a new TPM back.
9. Done!
NirSoft - freeware utilities: password recovery, system utilities, desktop utilities
Link📌 Summary:NirSoft網站提供多款免費軟體工具,涵蓋密碼恢復、系統工具、桌面工具等多個方面。這些工具由Nir Sofer開發,適用於Windows系統。使用者可以通過點擊相應連結來下載所需工具。
🎯 Key Points:
- NirSoft提供密碼恢復工具,例如WebBrowserPassView、RouterPassView、Mail PassView、Dialupass等,可以恢復瀏覽器密碼、路由器密碼、郵箱密碼、撥號密碼等。
- NirSoft提供網路監控工具,例如WirelessNetView、Wireless Network Watcher、BluetoothView、SmartSniff、CurrPorts等,可以監控無線網路、藍牙、TCP/IP封包等。
- NirSoft提供網際網路相關工具,例如BrowsingHistoryView、IPNetInfo、MyLastSearch、VideoCacheView、SiteShoter、DNSDataView、IECookiesView、IEHistoryView、WhoisThisDomain等,可以檢視瀏覽器歷史記錄、獲取IP地址信息、檢視最新搜索記錄、截圖網站、檢視DNS記錄等。
- NirSoft提供命令列工具,例如NirCmd、SoundVolumeView、GUIPropView、UninstallView、SearchMyFiles、Volumouse、FileTypesMan、ProduKey、ShellExView、WhatInStartup、USBDeview、DevManView、DriverView、RegScanner、OpenedFilesView、SysExporter、BlueScreenView等,可以從命令列執行多種任務,例如控制音量、檢視設備信息、掃描註冊表、抓取應用程式中的資料等。
- NirSoft定期更新軟體,並提供最新的功能和修復。
🔖 Keywords:
#NirSoft #freeware #tools #Windows #passwordrecovery #systemtools #networktools #desktoptools #commandline #update #news #registryscanner #tcpip #tcpconnectproblem #networkpasswordrecovery #chromecookies #dns #autofilter
Friends, sometimes, call me asking for help to recover their lost passwords. I finally had some time to write down the procedure that most people can follow to recover lost passwords on #Windows , #Linux, #macos , #bsd and other platforms.
#password #ethicalhacking #cybersecurity #PasswordRecovery #TechHelp
How to Recover Saved Passwords From Google | @BigTvTechMan
How to Recover Saved Passwords From Google | @BigTvTechMan #passwordrecovery #passwordtricks #googlepassword #gmailpasswordrecovery #bigtvtechman #shortfeed #technewstoday #technewsupdates Unlock the secrets to your Google Chrome passwords with our comprehensive guide! Learn how to view saved passwords on Google Chrome, recover deleted passwords, and retrieve lost data effortlessly. Discover expert tips on…
#vulnerability #passwordrecovery #forgotpassword #urltoken #wtf
https://www.ostechnix.com/find-wifi-password-of-connected-networks-in-linux/


 ✅🎯🙄
✅🎯🙄