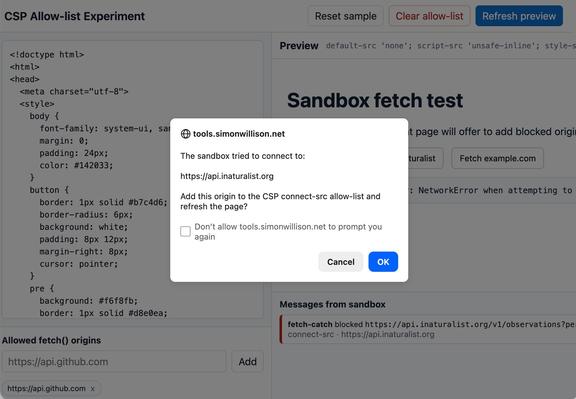
The one header I didn't add yet: CSP.
For sites that render untrusted input it mitigates an active surface. For a static site it guards against rarer-but-bigger events: a compromised analytics script, a poisoned CDN, a future change that adds an input path.
Astro 6 added an integration for what it emits; iframes, external fonts, and third-party services stay manual. Will inshallah follow when the audit fits.
📆 21 May 2026, 16:00–16:10 CDT
"What Are Web Developers Doing About Security?" by @torgo at Open Source SSF Community Day, Minneapolis, MN, USA 🇺🇸
The W3C SWAG community group ran a survey to see what web security features and technologies web developers are using and how they're using them. This talk will be a brief introduction to SWAG, an overview of the surprising results, and what it means for the work ahead.
https://www.w3.org/events/talks/2026/what-are-web-developers-doing-about-security/
#WebStandards #WebSecurity #OpenSSFCommunity
Enabled HSTS with includeSubDomains and preload.
The cost is real and one-way: every current and future subdomain must serve HTTPS or become unreachable. Removal from the preload list is in browser-release hands, not yours.
Accepted because the site is HTTPS-only by intent and Caddy provisions certs for every subdomain automatically via Let's Encrypt.
CSP Allow-list Experiment
https://simonwillison.net/2026/May/13/csp-allow/#atom-everything
Ben Dechrai presents 'Ten Key Steps for Enhanced Web App Security' this July at Nebraska.Code().
https://nebraskacode.amegala.com/
#WebApps #WebAppSecurity #DataIntegrity #SoftwareCraftsmanship #WebVulnerabilities #WebSecurity #CyberSecurity #TechConference #softwaredevelopment #SiliconPrairie #HeartlandDevelopers #Tech
Skipped Permissions-Policy on the static site.
It disables browser APIs (camera, mic, geolocation) the site doesn't use. Disabling something you're not using doesn't protect you from anything.
Embedding YouTube with fullscreen would also mean carving exceptions back in. More config for zero gain.
The scanner score drops one notch. The site is no less safe.
🌐 Website của bạn đang dùng HTTP hay HTTPS?
📈 HTTPS không chỉ giúp mã hóa dữ liệu & tăng bảo mật, mà còn cải thiện độ tin cậy với khách hàng và hỗ trợ SEO hiệu quả hơn.
🔒 Cùng Nhân Hòa tìm hiểu ngay sự khác biệt giữa HTTP và HTTPS: https://nhanhoa.com/tin-tuc/http-https-la-gi-so-sanh-giao-thuc-http-https.html

HTTP/HTTPS là gì? So sánh sự khác nhau giữa HTTP và HTTPS
HTTP và HTTPS đều là các giao thức truyền tải dữ liệu giữa trình duyệt và máy chủ website. Tìm hiểu sự khác nhau, cơ chế hoạt động, khả năng bảo mật và hướng dẫn chuyển website sang HTTPS.