#jobs #work #billionaires #life #ethicalHacking
#jobs #work #billionaires #life #ethicalHacking
Comprehensive List of Top 10 Uses for #VPS Servers If you've ever wondered, "what are common use-cases for VPS servers?", you have come to the right place!
We have compiled a list of the top 10 uses for VPS servers, as observed by Rad Web Hosting staff, during the course of providing VPS hosting services since 2015.
It should be noted that this compilation is not ...
Continued 👉 https://blog.radwebhosting.com/top-10-uses-for-vps-servers/?utm_source=mastodon&utm_medium=social&utm_campaign=mastodon.social #scalability #backup #vpnhosting #vpsservers #ethicalhacking #cloudstorage #gameservers
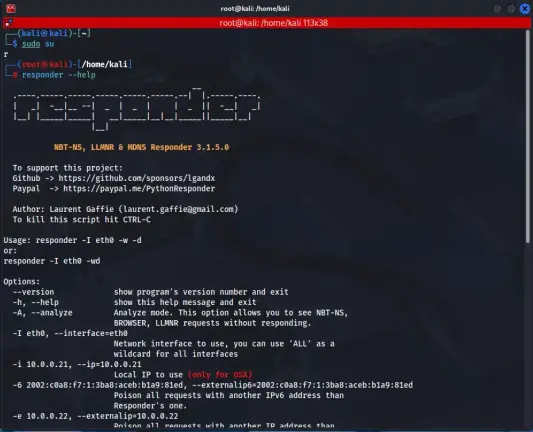
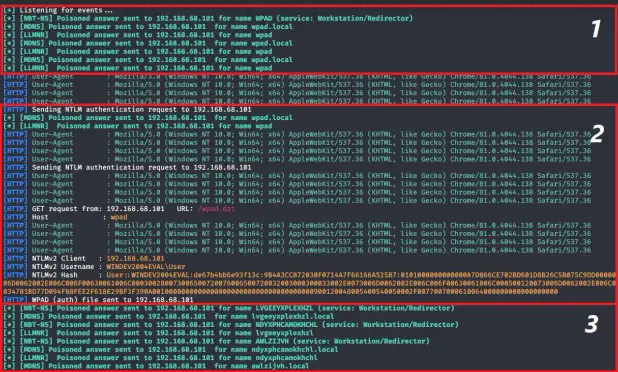
Responder Tool for Network Credential Capture in Active Directory
In this article, I cover how Responder works, common credential capture techniques, and practical mitigation strategies for defending Active Directory environments.
https://denizhalil.com/2026/05/18/responder-tool-active-directory-credential-capture/
#CyberSecurity #ActiveDirectory #Responder #LLMNR #NTLM #CredentialCapture #RedTeam #BlueTeam #Pentesting #WindowsSecurity #InfoSec #EthicalHacking #DenizHalil
Comprehensive List of Top 10 Uses for #VPS Servers If you've ever wondered, "what are common use-cases for VPS servers?", you have come to the right place!
We have compiled a list of the top 10 uses for VPS servers, as observed by Rad Web Hosting staff, during the course of providing VPS hosting services since 2015.
It should be noted that this compilation is not ...
Continued 👉 https://blog.radwebhosting.com/top-10-uses-for-vps-servers/?utm_source=mastodon&utm_medium=social&utm_campaign=mastodon.raddemo.host #ethicalhacking #cloudstorage #gameservers #backup #vpnhosting #vpsservers #scalability
#AdultESOL finished. Have one weekend off before classes start up again at the very end of May.
#k12 school year is almost finished, but I am doing an intensive, 2-week #ReadingInstruction / #dyslexia PD at the start of summer break.
My final #CyberSecurity course starts tomorrow --- #EthicalHacking! Very excited, but also very exhausted. Love it, but looking forward to being done with CYSC courses. Unfortunately, I won't be teaching it at #HighSchool next year.
#Malware #EthicalHacking #CyberDefense #NetworkSecurity #IncidentResponse

260516 rootshell.online
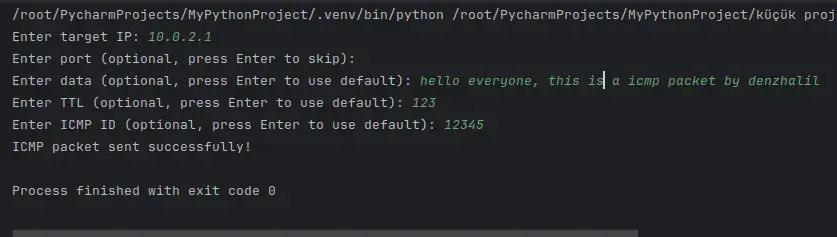
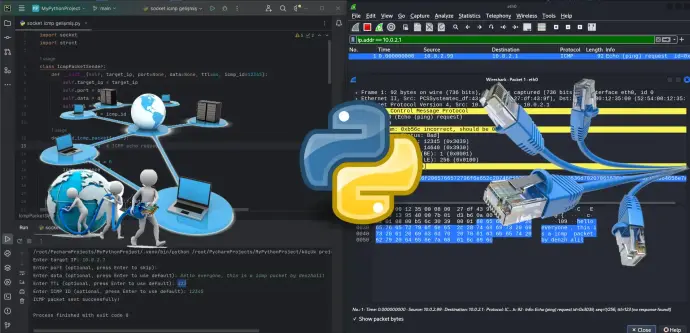
Sending ICMP Packets with Python Socket: Adventure in Signaling
In this article, I demonstrate how to craft and send ICMP packets using Python raw sockets, covering packet structure, checksum calculation, and low-level network communication.
https://denizhalil.com/2024/04/06/sending-icmp-packets-with-python-socket-adventure-in-signaling/
#CyberSecurity #Python #ICMP #SocketProgramming #NetworkSecurity #PacketCrafting #RawSockets #InfoSec #EthicalHacking #NetworkProgramming #DenizHalil
#Malware #EthicalHacking #CyberDefense #NetworkSecurity #IncidentResponse