Breaking the code: Multi-stage 'code of conduct' phishing campaign leads to AiTM token compromise
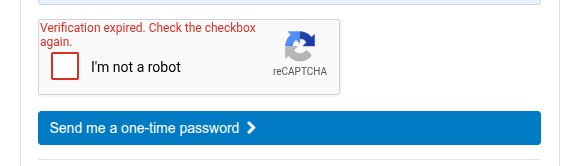
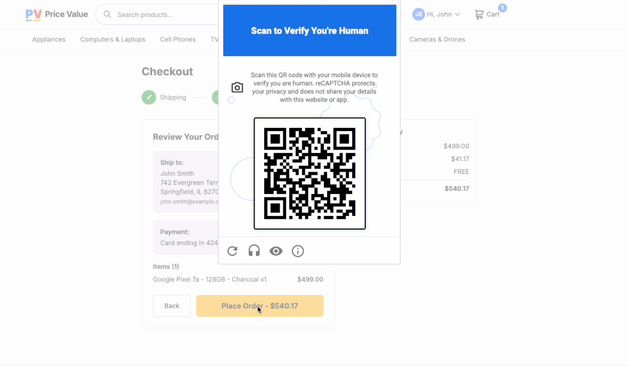
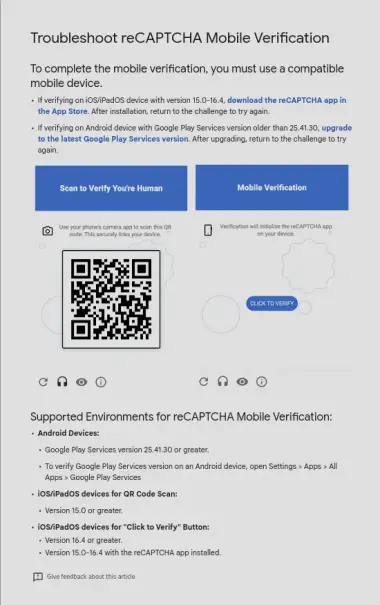
A sophisticated large-scale credential theft campaign targeted over 35,000 users across 13,000 organizations, primarily in the United States, between April 14-16, 2026. Attackers distributed fully authenticated emails from legitimate services using code of conduct-themed lures with polished HTML templates. The multi-stage attack chain included PDF attachments with embedded links, multiple CAPTCHA challenges, and intermediate staging pages designed to appear legitimate while filtering automated defenses. Recipients were directed through several layers ultimately leading to an adversary-in-the-middle phishing flow that proxied authentication sessions and captured tokens, bypassing non-phishing-resistant multifactor authentication. The campaign broadly impacted Healthcare, Financial services, Professional services, and Technology industries, using social engineering techniques that created urgency through time-bound prompts and concerning accusations.
Pulse ID: 69f8f1230f0bda494499b941
Pulse Link: https://otx.alienvault.com/pulse/69f8f1230f0bda494499b941
Pulse Author: AlienVault
Created: 2026-05-04 19:18:59
Be advised, this data is unverified and should be considered preliminary. Always do further verification.
#AdversaryInTheMiddle #AitM #CAPTCHA #CyberSecurity #Email #HTML #Healthcare #InfoSec #MultiFactorAuthentication #OTX #OpenThreatExchange #PDF #Phishing #SocialEngineering #UnitedStates #bot #AlienVault