Ok, so I've decided to expand on the #CAPTCHA joke a bit.
https://hacktivis.me/articles/cloudflare-turnstile-webgl-fingerprinting #Cloudflare #useragent #HackerNews #ngated
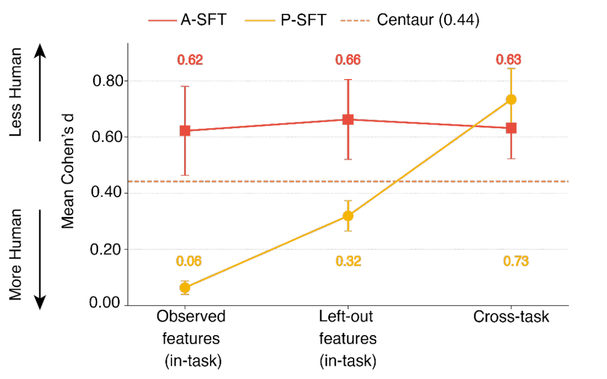
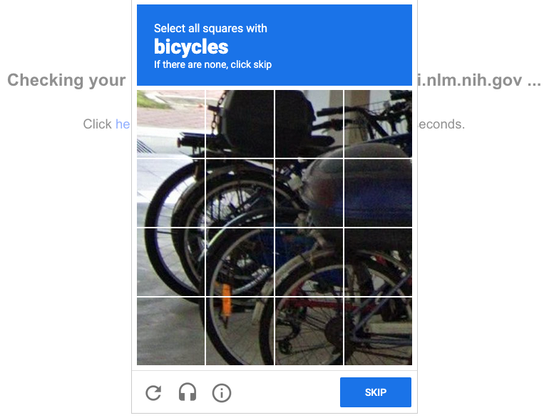
So for 20yrs #Google has been using #CAPTCHA our unpaid labor to train its learning models on scanned text, pics, its scanned books, articles & StreetView images (it couldn’t figure out) to train Waymo, #autonomous driving etc.
Same as #Pokémon Go scam.
https://research.roundtable.ai/captchas-detect-ai/ #CAPTCHA #technology #news #HackerNews #ngated
Unusual activity means the site (in this case eTsy can not grab data from my system to resell for marketing/advertising/data-mining/id-theft and all those nice things they are "usually" engaging in to provide access to "sellers' data" ...
Sellers should know their fees for listing include rights of reselling/exchanging data between seller/buyer into third parties.
#eTsy #eTsy,com #eBay #oBey #java #scripts #web #captcha
AND THIS IS AFTER allowing scripts for eTsy.com and captcha-delivery.com the only two sites listed as attempting to run scripts ...!!!!!!!!!!!!
__________
https://www.etsy.com/shop/Kosmimatis
We detected unusual activity from your device or network.
Reasons may include:
Rapid taps or clicks
JavaScript disabled or not working
Automated (bot) activity on your network (IP χχχ.χχχ.χχχ.χχχ)
Use of developer or inspection tools
Need help?
ID: χχχ.χχχ.χχχ.χχχ
"The CAPTCHA protocol
Difficult choices.
Olympus Mons Data Recovery Centre, 2830
Kael-7 felt the phantom itch in his neural interface — a topological dissonance. As lead logic archaeologist, he was accustomed to the fluid elegance of 137-base ternary systems, where data flowed like continuous, braided music. But the artefact pulsating on his retina was different. It was a clot of binary jaggedness, a relic that refused to integrate with the smooth curves of Martian reality.
(. . .)"
https://www.diffuseai.pub/p/the-structural-barriers-to-ai-lawyers #lifeWithoutJavaScript #AIChallenges #AIandLaw #technologyBarriers #HackerNews #ngated
Internet is broken, episode 358.