🇺🇸 #Democrats pave way for $70 billion infusion to #ICE and Border
https://www.wsws.org/en/articles/2026/05/02/puyu-m02.html
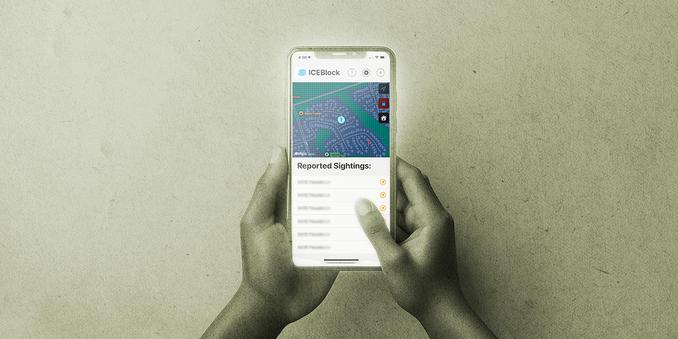
#Abolishice
#demos #usa #uspol #news #socialmedia #billionaires #plutocracy #oligarchy #resistance #democraticparty #us #democracy #civilrights #resistance #fuckice #usa #policestate #minnesota #minneapolis #chicago #michigan #portland @politics #Iran #Palestine #IsraelWarCrimes #uspol #resistance #humanrights #education #health #law #protest #freespeech #activism #congress #cbp #immigration #dhs