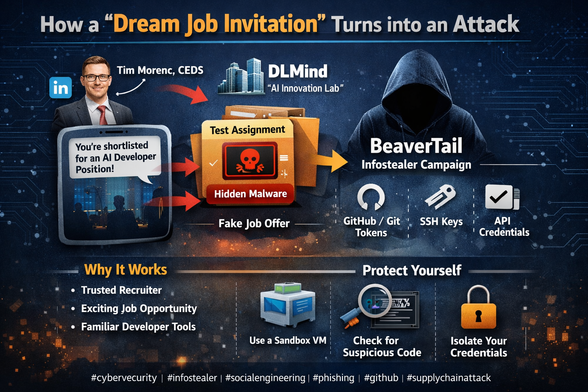
[Translation] How a “dream job invitation” turns into an attack
It all starts with a notification that feels familiar and exciting for any developer: “You’ve been shortlisted for an AI developer position.” The company looks impressive — DLMind, an “AI innovation lab.” The recruiter appears legitimate — Tim Morenc, CEDS, with a polished LinkedIn profile, professional communication style, and mutual connections.
But behind this friendly outreach is BeaverTail — a malicious operation designed to steal your code, credentials, and developer assets.
The attack is part of a broader pattern associated with North Korean cyber operations, including groups such as Lazarus Group.
How the attack works
The victim is approached via LinkedIn or similar platforms
A convincing fake company and recruiter profile is used
A “technical assignment” or test task is provided
The task contains malicious code or a compromised dependency
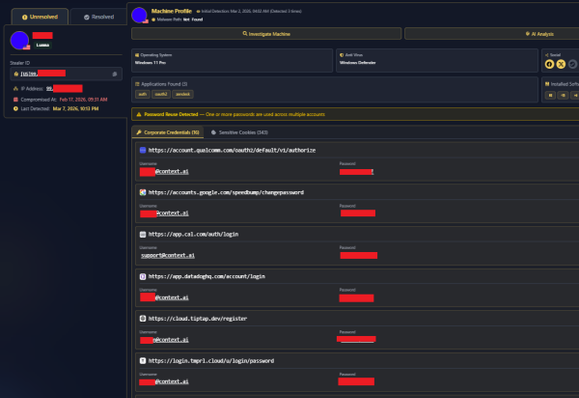
Once executed, it extracts sensitive data such as:
GitHub / Git credentials
SSH keys
API tokens
browser session data
Why it works
The campaign relies on social engineering rather than technical exploitation:
trust in recruitment processes
desire for career opportunities
familiarity of developer workflows (GitHub, npm, Python, etc.)
Key takeaway
Any unsolicited “test assignment” should be treated as potentially hostile code. Execution environments must be isolated, and credentials should never be exposed in evaluation setups.
---
#hashtags
#cybersecurity #infosec #malware #socialengineering #phishing #infostealer #supplychainattack #github #developers #techsecurity #beavertail #lazarusgroup