I'm looking for a good overview/comparison of different #MFA/#2FA or #PasswordLess authentication protocols.
The recent #Fido2 #MitM risk made me aware that I need to learn more.
Pointers and #BoostWelcome
#fedipower #wisdomOfTheCrowd #FollowerPower
As the best way to get an answer on the internet, is to state something wrong, let's try this 😜
#FIDO and FIDO2 are actually a whole set of (related?) protocols.
FIDO includes FIDO #UAF (Universal Authentication Framework) and FIDO #U2F (Universal Second Factor).
FIDO2 is the "successor" of FIDO and consists of two parts.
#WebAuthn and #CTAP (Client to Authenticator Protocol). From the name I would guess that WebAuthn is for web stuff (requiring browser support) and CTAP is for IT infrastructure stuff (???)
#Passkey is based on #Fido2
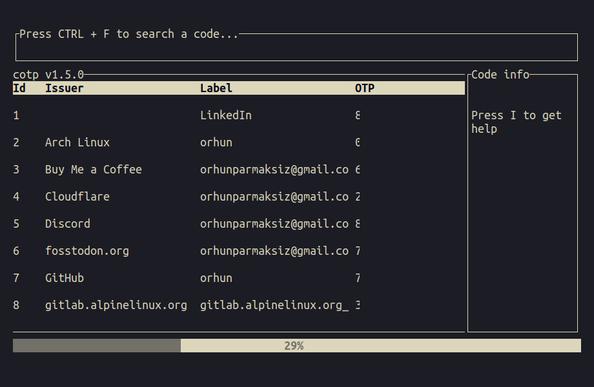
Other related concepts or protocols are #OTP (one-time passwords), #TOTP (Time-based One-time Password) and #HOTP (“H” in HOTP stands for Hash-based Message Authentication Code (HMAC))
Not sure how #SmartCards play into this.
And not sure which of these methods would work for an offline authentication login into your laptop (and ideally also as key for whole disk encryption)