#CloudZ #malware abuses #Microsoft #PhoneLink to steal #SMS and OTPs
Updated Vernier/SG: a hand cipher kernel that replaces the one-time pad.
The Vernier cipher uses an OTP at its core. OTPs are information-theoretically secure but operationally expensive — pad pages must be generated, distributed, stored, used once, destroyed. Possession is incriminating. The pad is the liability.
Vernier/SG replaces the pad with a digit stream both parties derive independently from a single shared number: a Sophie Germain prime.
A Sophie Germain prime p is one where 2p+1 is also prime. The second prime — q, the "safe prime" — is bonded to p; knowing p determines q.
The stream comes from a multiplicative walk modulo q:
s(n) = g * s(n-1) mod q
where g is the smallest primitive root of q with g >= 5. Each pad digit is the last digit of the digit sum of s(n). The period is exactly 2p, guaranteed by Fermat-Euler.
Worked example, p=83, q=167, g=5:
s: 1, 5, 25, 125, 124, 119, 94, 136, 12, 60, 133, ...
pad: 1, 5, 7, 8, 7, 1, 3, 0, 3, 6, 7, ...
Two parties starting from the same p generate the identical stream. Adding it to a Vernier-encoded message mod 10 is the encryption.
When a kernel's stream exhausts at 2p digits, both parties take the last full value and find the nearest SG prime strictly greater. That's the next kernel. The system self-extends indefinitely from the initial seed alone.
Kerckhoffs's principle holds completely. The algorithm is public, including the lookup table of SG primes — that's mathematics, not key material. The only secret is one number.
Key distribution gets interesting. Verbal: "eighty-three." Contextual: a year both parties remember, walked forward to the nearest SG prime. Dice: roll a handful of d10s in front of the other party, concatenate the digits, walk forward. The dice carry no kernel until you do the walk; the walk is mechanical and reproducible from the rolled digits alone.
Three rejected designs taught the math:
Direct mod-10 extraction produces long runs of repeated digits.
Additive walks produce linear arithmetic progressions with predictable staircases.
Fibonacci recurrences have unpredictable Pisano periods. p=1103 has period 64, shorter than one block.
The multiplicative walk with digit-sum extraction passes chi-squared and autocorrelation across all 318 SG primes tested.
For broadcast use, SKP-1 wraps it: HKDF-SHA512 stream, 10-digit kernel fingerprint, 20-digit HMAC, date-derived counter. Header is 24 digits; the rest is ciphertext plus authentication.
Threat model: informed human adversaries with intercepted traffic and patience. Not nation-state SIGINT — the binary mode with ChaCha20-Poly1305 is for that. What Vernier/SG provides: nothing physical to find, full algorithmic transparency, mathematical deniability, recovery via rotation if a kernel burns.
The pad is gone. The number remains.
Bucharest Henri Coandă International Airport - Otopeni, Romania
https://en.wikipedia.org/wiki/Henri_Coand%C4%83_International_Airport
https://www.openstreetmap.org/#map=13/44.572127/26.103396
#LROP #OTP #Otopeni #Romania #airport #aviation #avgeeks #GIS
Learn how to integrate PingID MFA using push notifications and OTP configuration for enhanced security.
📢⚠️ Watch out for this new 11-step DHL phishing scam that uses fake OTP codes and EmailJS to harvest user credentials and device telemetry.
Read: https://hackread.com/dhl-phishing-scam-attack-chain-steal-passwords/
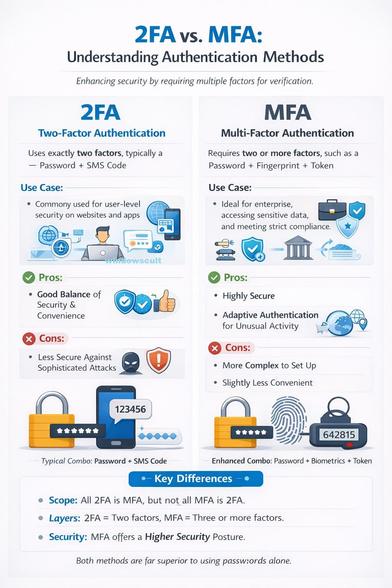
Two-Factor #Authentication (2FA) typically combines a password with a code, whereas Multi-Factor Authentication (MFA) adds more layers, such as biometrics (fingerprint/face) or hardware tokens. Read MFA vs 2FA: What's the difference https://windowspost.com/2fa-vs-mfa/
Key Differences Between 2FA and MFA
Number of Factors: 2FA limits authentication to two layers (e.g., password + OTP), while MFA can incorporate three or more (e.g., password + OTP + fingerprint).
Security Level: MFA generally provides superior security against sophisticated attacks because it relies on multiple independent factors.
Complexity & UX: 2FA offers a more streamlined user experience with fewer steps. MFA may cause more user friction due to additional login steps, but it enhances security.
Flexibility: MFA offers greater flexibility, allowing organizations to adopt adaptive, risk-based authentication, while 2FA is a fixed two-step process
2FA Example: Entering a password (knowledge) and a code texted to your phone (possession).
MFA Example: Entering a password, a code from an app, and using a biometric scan (fingerprint or face)
#2FA #MFA #security #password #otp #Fingerprint #twostepverification #MFAverification #photochallange #technology #tech #TechGuide #techterms #techarticle
An OTP (One Time Password) is valid for exactly 30–60 seconds.
Even though no one stores it anywhere. So, how does the server verify it without ever saving it?
Well, that’s usually called a Time-based One-Time Password (TOTP).
Here’s how it actually works:
• A secret key is shared between your device and the server (only once)
• Both use the current time window (like 30 seconds)
• And a secure algorithm (HMAC)
Using these, both sides generate the same OTP independently.
✅ No storage
✅ No database lookup
✅ Just math + time
When you enter the OTP, the server simply regenerates it and checks:
👉 “Does this match?”
That’s how your OTP is verified… without ever being saved. 🔐