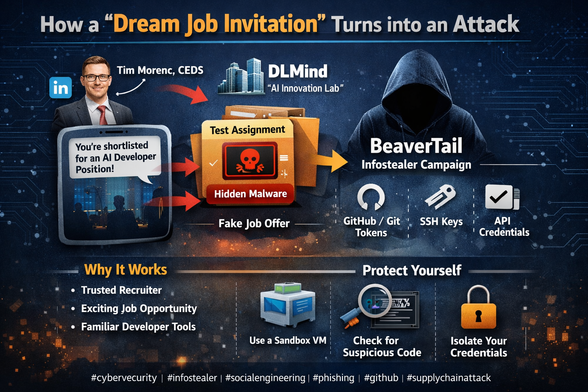
[Translation] How a “dream job invitation” turns into an attack
It all starts with a notification that feels familiar and exciting for any developer: “You’ve been shortlisted for an AI developer position.” The company looks impressive — DLMind, an “AI innovation lab.” The recruiter appears legitimate — Tim Morenc, CEDS, with a polished LinkedIn profile, professional communication style, and mutual connections.
But behind this friendly outreach is BeaverTail — a malicious operation designed to steal your code, credentials, and developer assets.
The attack is part of a broader pattern associated with North Korean cyber operations, including groups such as Lazarus Group.
How the attack works
The victim is approached via LinkedIn or similar platforms
A convincing fake company and recruiter profile is used
A “technical assignment” or test task is provided
The task contains malicious code or a compromised dependency
Once executed, it extracts sensitive data such as:
GitHub / Git credentials
SSH keys
API tokens
browser session data
Why it works
The campaign relies on social engineering rather than technical exploitation:
trust in recruitment processes
desire for career opportunities
familiarity of developer workflows (GitHub, npm, Python, etc.)
Key takeaway
Any unsolicited “test assignment” should be treated as potentially hostile code. Execution environments must be isolated, and credentials should never be exposed in evaluation setups.
---
#hashtags
#cybersecurity #infosec #malware #socialengineering #phishing #infostealer #supplychainattack #github #developers #techsecurity #beavertail #lazarusgroup
@habr25 [Translation] How a “dream job invitation” turns into an attack
It all starts with a notification that feels familiar and exciting for any developer: “You’ve been shortlisted for an AI developer position.” The company looks impressive — DLMind, an “AI innovation lab.” The recruiter appears legitimate — Tim Morenc, CEDS, with a polished LinkedIn profile, professional communication style, and mutual connections.
But behind this friendly outreach is BeaverTail — a malicious operation designed to steal your code, credentials, and developer assets.
The attack is part of a broader pattern associated with North Korean cyber operations, including groups such as Lazarus Group.
How the attack works
The victim is approached via LinkedIn or similar platforms
A convincing fake company and recruiter profile is used
A “technical assignment” or test task is provided
The task contains malicious code or a compromised dependency
Once executed, it extracts sensitive data such as:
GitHub / Git credentials
SSH keys
API tokens
browser session data
Why it works
The campaign relies on social engineering rather than technical exploitation:
trust in recruitment processes
desire for career opportunities
familiarity of developer workflows (GitHub, npm, Python, etc.)
Key takeaway
Any unsolicited “test assignment” should be treated as potentially hostile code. Execution environments must be isolated, and credentials should never be exposed in evaluation setups.
---
#hashtags
#cybersecurity #infosec #malware #socialengineering #phishing #infostealer #supplychainattack #github #developers #techsecurity #beavertail #lazarusgroup
Federal prosecutors charged a 20-year-old Texas man with attempted murder after he allegedly threw a Molotov cocktail at OpenAI CEO Sam Altman's home, then tried to break into the company's headquarters. Court filings say he carried a list of AI executives' addresses and told security he came to "kill anyone inside." A separate, unrelated shooting at the same residence occurred Sunday.

Texas Man Charged in Molotov Attack on Sam Altman; Prosecutors Say He Kept AI Executive Target List
Federal and state prosecutors charged a 20-year-old Texas man Monday with attempted murder in Friday's Molotov cocktail attack on OpenAI CEO Sam Altman's San Francisco home. Court filings say Daniel Moreno-Gama traveled from Spring, Texas, hit Altman's Russian Hill residence at 3:45 a.m., then tried to break into OpenAI's headquarters with a chair. In his backpack: incendiary devices, a jug of kerosene, and a document naming other AI CEOs by home address.
Two separate attacks on OpenAI CEO Sam Altman's San Francisco home within 72 hours raise questions about AI executive security. Police arrested two people after Sunday gunfire incident, following Friday's Molotov cocktail attack by Texas man. Three firearms seized. No injuries reported. Investigators haven't confirmed if incidents are connected.
#AISafety #TechSecurity #OpenAI
https://www.implicator.ai/sam-altmans-home-hit-by-gunfire-days-after-molotov-attack-two-arrested/

Sam Altman Home Hit by Gunfire, Two Arrested in SF
San Francisco police arrested two people Sunday after reported gunfire near OpenAI CEO Sam Altman's Russian Hill home, 48 hours after a 20-year-old Texas man allegedly firebombed the property. Three guns seized. Nobody hurt either time. FBI is watching.
Windows 95 defenses against installers that overwrite a file with an older one
https://devblogs.microsoft.com/oldnewthing/20260324-00/?p=112159
#HackerNews #Windows95 #Installers #FileOverwrite #SoftwareHistory #TechSecurity
Anthropic accidentally published Claude Code's complete 512,000-line source code to npm's public registry for the second time in 13 months. The leak exposed system prompts, feature flags, and internal codenames before being removed. Pattern suggests operational challenges at a company positioning itself as the responsible AI leader heading toward IPO.
#AIGovernance #TechSecurity #Anthropic
https://www.implicator.ai/opinion-anthropic-built-undercover-mode-then-shipped-the-blueprints/
The recent Iranian 🇮🇷 cyber attack on Stryker, a Michigan-based medical device giant, marks a sobering escalation in the digital shadow war. Thousands of employees woke up yesterday to find their laptops and cellphones remotely wiped and disabled. This was not a standard data breach but a targeted disruptive operation launched by the Handala hacking group, which has documented ties to the Iranian Ministry of Intelligence.
The attackers did not use traditional malware. Instead, they compromised the company’s Microsoft Intune account—the very platform used by IT departments to manage and secure corporate devices. By triggering the remote wipe feature intended for lost or stolen hardware, the hackers effectively paralyzed the workforce. This incident serves as a stark reminder that our greatest security assets can quickly become our most significant liabilities when access is compromised.
🧠 Hackers hijacked the Microsoft Intune management console to wipe employee devices.
⚡ Handala Team claims the attack is retaliation for a recent missile strike on an Iranian school.
🎓 This is the first major Iranian cyberattack on a U.S. firm since current hostilities began.
🔍 Sophos and other security firms have officially linked the perpetrators to Iranian state intelligence.
https://www.nbcnews.com/world/iran/iran-appears-conducted-significant-cyberattack-us-company-first-war-st-rcna263084
#CyberWarfare #TechSecurity #Geopolitics #War #security #privacy #cloud #infosec #cybersecurity

Iran appears to have conducted a significant cyberattack against a U.S. company, a first since the war started
An Iran-linked hacker group has claimed responsibility for a cyberattack on a medical tech company in what appears to be the first significant instance of Iran’s hacking an American company since the start of the war between the countries
Warum ich 1000 E-Mail-Adressen nutze - und warum Du das auch tun solltest
Die meisten Menschen nutzen eine einzige E-Mail-Adresse für alles: Online-Shops, Foren, Newsletter, Apps und soziale Netzwerke. Klingt praktisch – ist aber ein Sicherheitsproblem. Denn sobald diese Adresse in einem Datenleck landet, verbreitet sie sich unkontrolliert im Netz. Spam, Phishing und dubiose Werbung sind dann nur eine Frage der Zeit.
Ich gehe einen anderen Weg: Für jeden Dienst verwende ich eine eigene E-Mail-Adresse. Möglich macht das eine simple Technik namens Catch-All. Das Ergebnis ist überraschend effektiv: Ich erkenne sofort, woher Spam kommt, kann einzelne Adressen gezielt abschalten und behalte die Kontrolle über meinen Posteingang.
Warum dieses System funktioniert – und warum es jeder nutzen sollte – erkläre ich im Artikel. [Mehr lesen...]
#Email #Spam #Datenleck #CyberSecurity #InfoSec #Privacy #DataProtection #EmailSecurity #Phishing #CyberSecurityAwareness #ITSecurity #DataSecurity #OnlineSecurity #StaySafeOnline #CyberAware #SecurityTips #PhishingAlert #CyberDefense #InternetSecurity #DigitalSecurity #Datenschutz #CyberCrime #TechSecurity